What Is Tcp Session Hijacking

Tcp Session Hijacking En Pdf Transmission Control Protocol Data The most common method of session hijacking is called ip spoofing, when an attacker uses source routed ip packets to insert commands into an active communication between two nodes on a network and disguise itself as one of the authenticated users. What is session hijacking? in session hijacking (tcp hijacking), attackers steal a web user’s active session by acquiring their unique session id. this lets them impersonate the user, accessing data or performing actions as if they were the legitimate user.
Github Masum95 Tcp Session Hijacking Tcp ip hijacking, a significant concern in the cybersecurity space, refers to the exploitation of a legitimate computer session to illicitly gain access to data that one otherwise wouldn't have access to. It is a widely known fact that unencrypted tcp ip connections can be snooped and intercepted, but what some may not know is that it is possible to completely hijack a tcp connection and act. Session hijacking – sometimes called cookie hijacking, cookie side jacking, or tcp session hijacking – occurs when an attacker takes over your internet session. this might happen when you’re shopping online, paying a bill, or checking your bank balance. Tcp session hijacking is a type of network attack that exploits a vulnerability in the tcp ip protocol to take over an established connection between two devices. by impersonating one of the.
Github Abhik1505040 Tcp Session Hijacking Demo Tool For Hijacking Session hijacking – sometimes called cookie hijacking, cookie side jacking, or tcp session hijacking – occurs when an attacker takes over your internet session. this might happen when you’re shopping online, paying a bill, or checking your bank balance. Tcp session hijacking is a type of network attack that exploits a vulnerability in the tcp ip protocol to take over an established connection between two devices. by impersonating one of the. What is tcp session hijacking? simple definition: tcp session hijacking is an attack where an attacker takes control of an established tcp connection between two systems by predicting or manipulating sequence numbers, allowing them to inject commands or steal data from the hijacked session. Also called tcp session hijacking or cookie hijacking, session hijacking lets attackers impersonate real users without needing their original login information by taking advantage of active user sessions that are already authenticated. Definition: tcp ip hijacking, also known as session hijacking, involves an attacker taking control of an active tcp ip session between two devices. purpose: the primary goal is to intercept, modify, or inject data into the communication stream without the knowledge of the communicating parties. Transmission control protocol internet protocol (tcp ip) session hijacking involves an attacker predicting or guessing the sequence number of tcp segments exchanged between two nodes during the three way handshake. this allows the attacker to hijack the session before it is fully established.
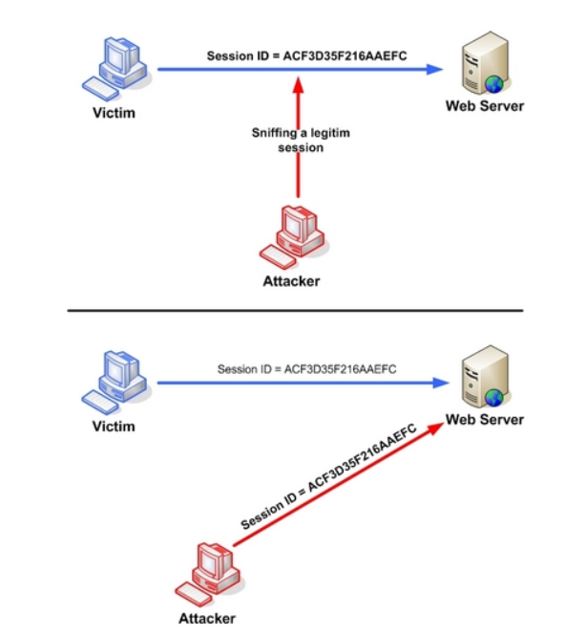
Tcp Session Hijacking K 12 Cybersecurity Educations What is tcp session hijacking? simple definition: tcp session hijacking is an attack where an attacker takes control of an established tcp connection between two systems by predicting or manipulating sequence numbers, allowing them to inject commands or steal data from the hijacked session. Also called tcp session hijacking or cookie hijacking, session hijacking lets attackers impersonate real users without needing their original login information by taking advantage of active user sessions that are already authenticated. Definition: tcp ip hijacking, also known as session hijacking, involves an attacker taking control of an active tcp ip session between two devices. purpose: the primary goal is to intercept, modify, or inject data into the communication stream without the knowledge of the communicating parties. Transmission control protocol internet protocol (tcp ip) session hijacking involves an attacker predicting or guessing the sequence number of tcp segments exchanged between two nodes during the three way handshake. this allows the attacker to hijack the session before it is fully established.

Tcp Session Hijacking Definition: tcp ip hijacking, also known as session hijacking, involves an attacker taking control of an active tcp ip session between two devices. purpose: the primary goal is to intercept, modify, or inject data into the communication stream without the knowledge of the communicating parties. Transmission control protocol internet protocol (tcp ip) session hijacking involves an attacker predicting or guessing the sequence number of tcp segments exchanged between two nodes during the three way handshake. this allows the attacker to hijack the session before it is fully established.

What Is Tcp Session Hijacking
Comments are closed.