Tcp Session Hijacking
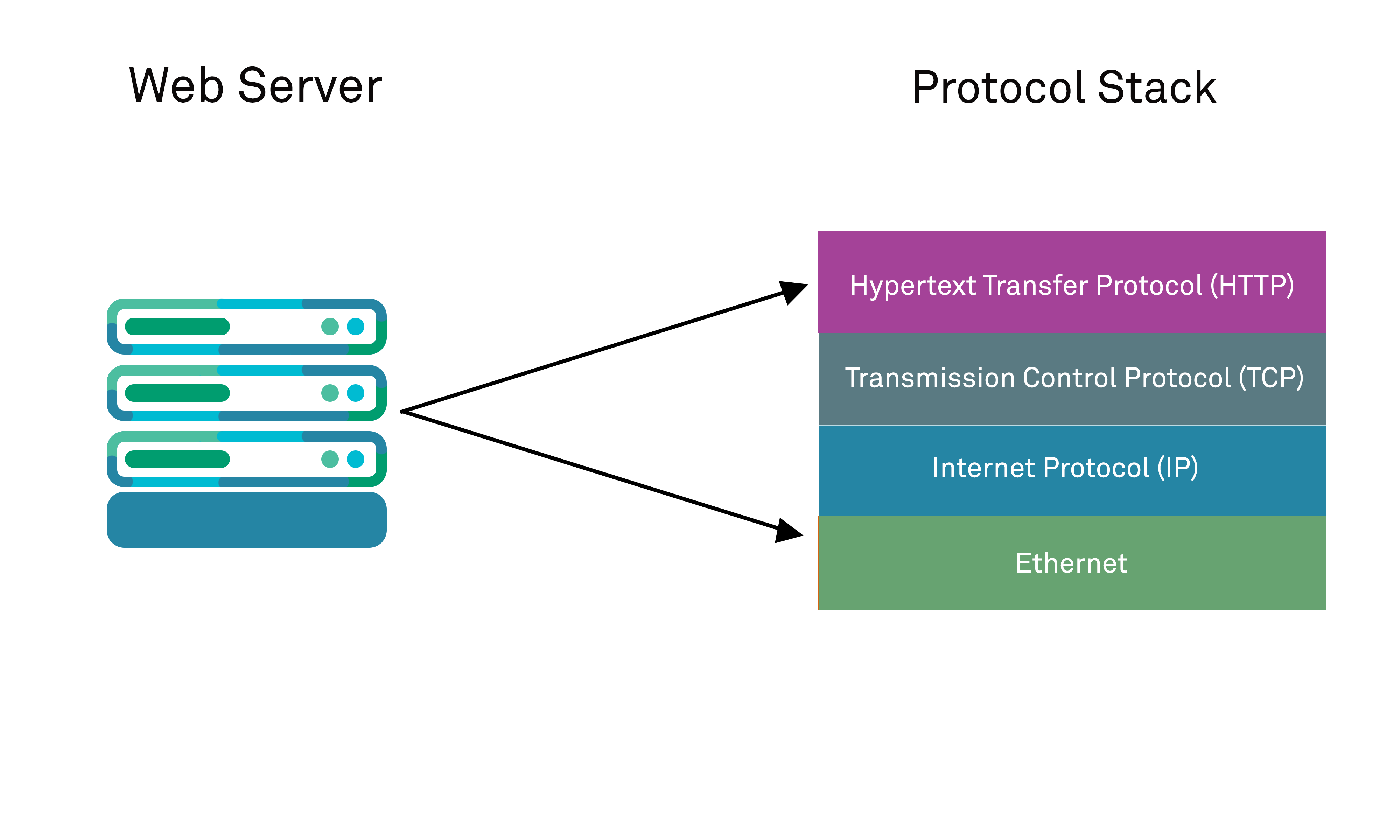
Session Hijacking In session hijacking (tcp hijacking), attackers steal a web user’s active session by acquiring their unique session id. this lets them impersonate the user, accessing data or performing actions as if they were the legitimate user. Tcp ip hijacking, a significant concern in the cybersecurity space, refers to the exploitation of a legitimate computer session to illicitly gain access to data that one otherwise wouldn't have access to.
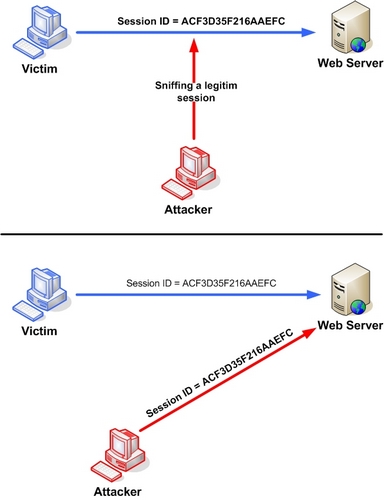
Session Hijacking Attack Owasp Foundation A session hijacking assault or tcp session hijacking attack happens when an assailant assumes command over a client's session. at the point when you sign into a help, for example, your financial application, a session starts and closures when you log out. Tcp session hijacking is a type of network attack that exploits a vulnerability in the tcp ip protocol to take over an established connection between two devices. by impersonating one of the. Session hijacking – sometimes called cookie hijacking, cookie side jacking, or tcp session hijacking – occurs when an attacker takes over your internet session. this might happen when you’re shopping online, paying a bill, or checking your bank balance. An attacker can add the desynchronizing stage to the hijack sequence to deceive the target host. without desynchronizing, the attacker injects data into the server while keeping his or her identity by spoofing an ip address.

Chapter 11 Session Hijacking Quizlet Session hijacking – sometimes called cookie hijacking, cookie side jacking, or tcp session hijacking – occurs when an attacker takes over your internet session. this might happen when you’re shopping online, paying a bill, or checking your bank balance. An attacker can add the desynchronizing stage to the hijack sequence to deceive the target host. without desynchronizing, the attacker injects data into the server while keeping his or her identity by spoofing an ip address. Also called tcp session hijacking or cookie hijacking, session hijacking lets attackers impersonate real users without needing their original login information by taking advantage of active user sessions that are already authenticated. Transmission control protocol internet protocol (tcp ip) session hijacking involves an attacker predicting or guessing the sequence number of tcp segments exchanged between two nodes during the three way handshake. this allows the attacker to hijack the session before it is fully established. Session hijacking (tcp hijacking) occurs when attackers take control of a legitimate user’s active web session by capturing the session’s unique id. In this chapter, you will learn about session hijacking, including the steps involved, the different types, and the countermeasures that can be used to protect against this type of attack.
Comments are closed.