Chapter 11 Session Hijacking Quizlet

Chapter 11 Session Hijacking Quizlet Study with quizlet and memorize flashcards containing terms like session hijacking, session hijacking process, network level hijacking and more. Session fixation is an attack that permits an attacker to hijack a valid user session. the attack explores a limitation in the way the web application manages the session id, more specifically the vulnerable web application.

Session Hijacking Concepts Flashcards Quizlet Study module 11: session hijacking flashcards from chris quinn's class online, or in brainscape's iphone or android app. learn faster with spaced repetition. On studocu you find all the lecture notes, summaries and study guides you need to pass your exams with better grades. As a system administrator, you should understand different session hijacking concepts, how attackers perform application and network level session hijacking, and different tools used to perform the attack. This section highlights session hijacking and dangers posed by it, techniques used for session hijacking, spoofing vs. hijacking, the session hijacking process, types of session hijacking, and session hijacking in the osi model.

Session Hijacking Attack Example And Prevention As a system administrator, you should understand different session hijacking concepts, how attackers perform application and network level session hijacking, and different tools used to perform the attack. This section highlights session hijacking and dangers posed by it, techniques used for session hijacking, spoofing vs. hijacking, the session hijacking process, types of session hijacking, and session hijacking in the osi model. As cyber threats evolve, understanding and mitigating session hijacking becomes crucial for safeguarding digital assets. in module 11 of ceh, you will dive into session hijacking attacks—a sneaky cyber attack where attackers exploit web sessions to gain unauthorized access to information. Study with quizlet and memorize flashcards containing terms like session hijacking, spoofing attack, session desynchronization and more. Allows an attacker to hijack a valid user session attacker gets a users to authenticate with a know session id and then hijacks the session with the known session id. Study module 11 session hijacking flashcards from fabs pam's pitagoras class online, or in brainscape's iphone or android app. learn faster with spaced repetition.
What Is Session Hijacking How To Ensure Session Privacy As cyber threats evolve, understanding and mitigating session hijacking becomes crucial for safeguarding digital assets. in module 11 of ceh, you will dive into session hijacking attacks—a sneaky cyber attack where attackers exploit web sessions to gain unauthorized access to information. Study with quizlet and memorize flashcards containing terms like session hijacking, spoofing attack, session desynchronization and more. Allows an attacker to hijack a valid user session attacker gets a users to authenticate with a know session id and then hijacks the session with the known session id. Study module 11 session hijacking flashcards from fabs pam's pitagoras class online, or in brainscape's iphone or android app. learn faster with spaced repetition.
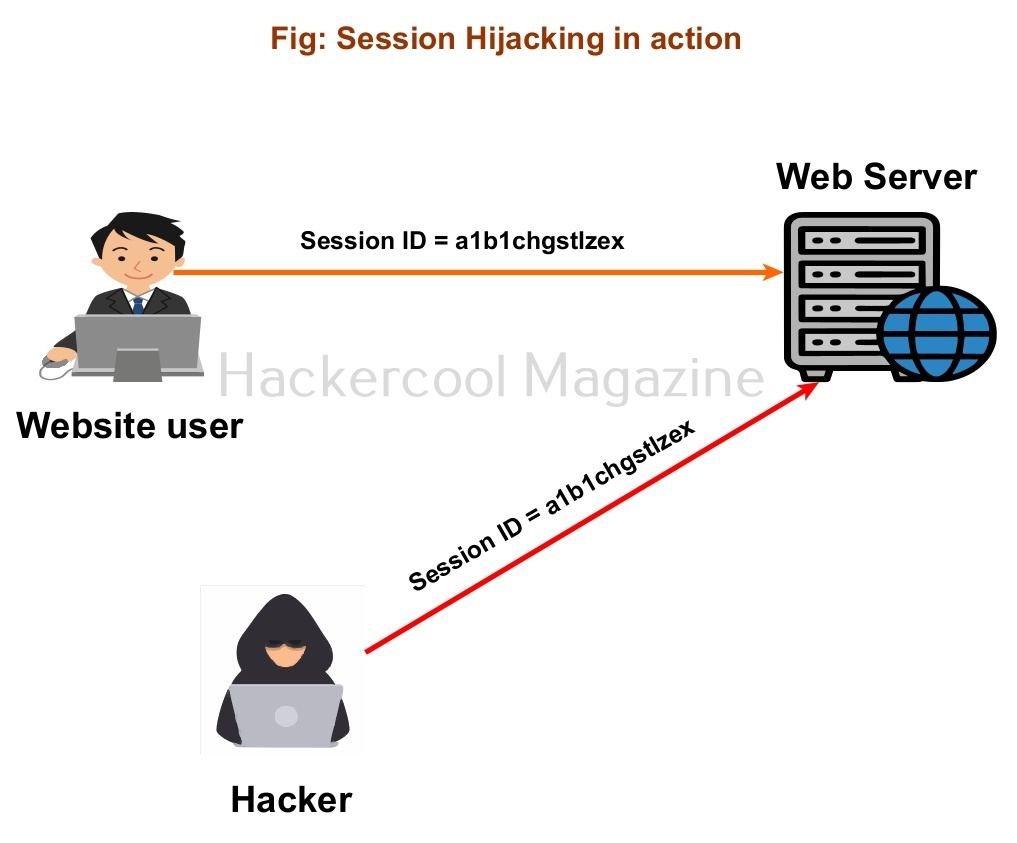
Session Hijacking For Beginners Allows an attacker to hijack a valid user session attacker gets a users to authenticate with a know session id and then hijacks the session with the known session id. Study module 11 session hijacking flashcards from fabs pam's pitagoras class online, or in brainscape's iphone or android app. learn faster with spaced repetition.
Comments are closed.