Web Inject Php Code To Image File
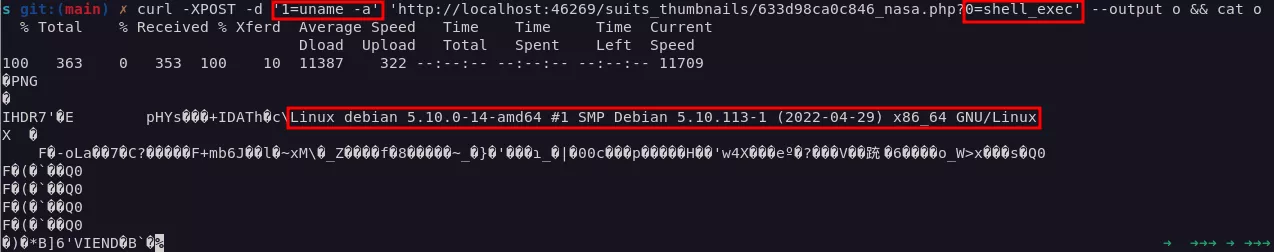
Inject Php Code Within Jpeg Files Hack Server By Polyglots Image This first part will describe the most simple and basic case of php payload injection in a png image, leading to arbitrary php code execution. to illustrate this, we will use the first part route. It supports two techniques: inline payload: appends php code directly to the image exif metadata injection: embeds the payload in the image's comment field using exiftool. by default, the payload uses the get based execution mode (?cmd=your command) unless a fixed command is specified.

Github Jenderal92 Inject Php To Jpg Using Jhead I recently came across a web application with two methods for adding images to its media library: local file upload and remote file upload from a stock photo website. I remember seeing an exploit for an image uploading function, which consisted of hiding malicious php code inside a tiff image. i'm making my own image uploading script, and i assume i'll have to protect myself from this possibility. Php jpeg injector injects php payloads into jpeg images. proof of concept to exploit the flaw in the php gd built in function. In this scenario, attacker generates a webshell (or a dropper), uses this article as a guide, and sneaks php into a png file. the file is tested by the server, it's found to be a valid image file, and the attacker get the url for the uploaded image.
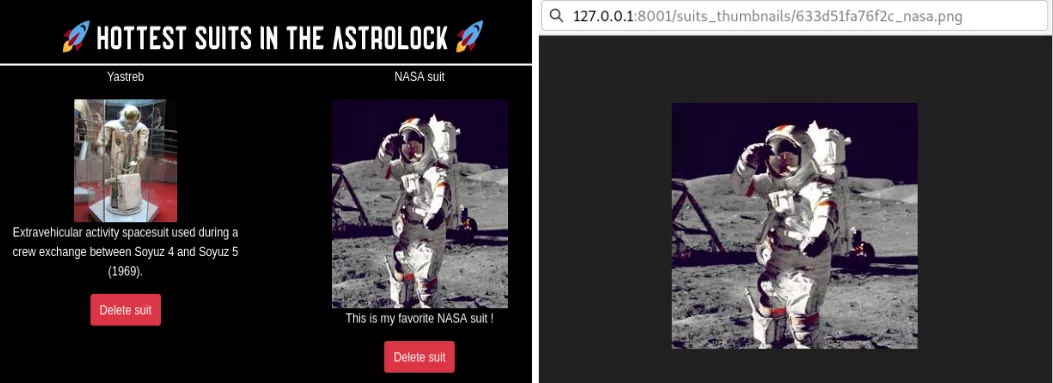
Persistent Php Payloads In Pngs How To Inject Php Code In An Image Php jpeg injector injects php payloads into jpeg images. proof of concept to exploit the flaw in the php gd built in function. In this scenario, attacker generates a webshell (or a dropper), uses this article as a guide, and sneaks php into a png file. the file is tested by the server, it's found to be a valid image file, and the attacker get the url for the uploaded image. Many times, uploading a malicious file (such as a reverse shell) to the victim machine, and making it work, is not so obvious. the victim’s web administrator may have set filters to help determine the types of files that can be uploaded to their server. This known vulnerability walks us through (via the link mentioned above) on how to get the to interpret the php code via the newsletter template. the crucial thing is once you’ve updated your template, make sure you save it. Upload the file and visit the image’s url. the image will display and the php code will also execute. Attach imagenote: image must be jpeg format for exif. warning: due to the exif library used, payloads will be utf16 encoded which may lead to additional null bytes. set extension to (with .): make my payload! disclaimer: this tool is only to be used for legal uses such as ctf challenges.
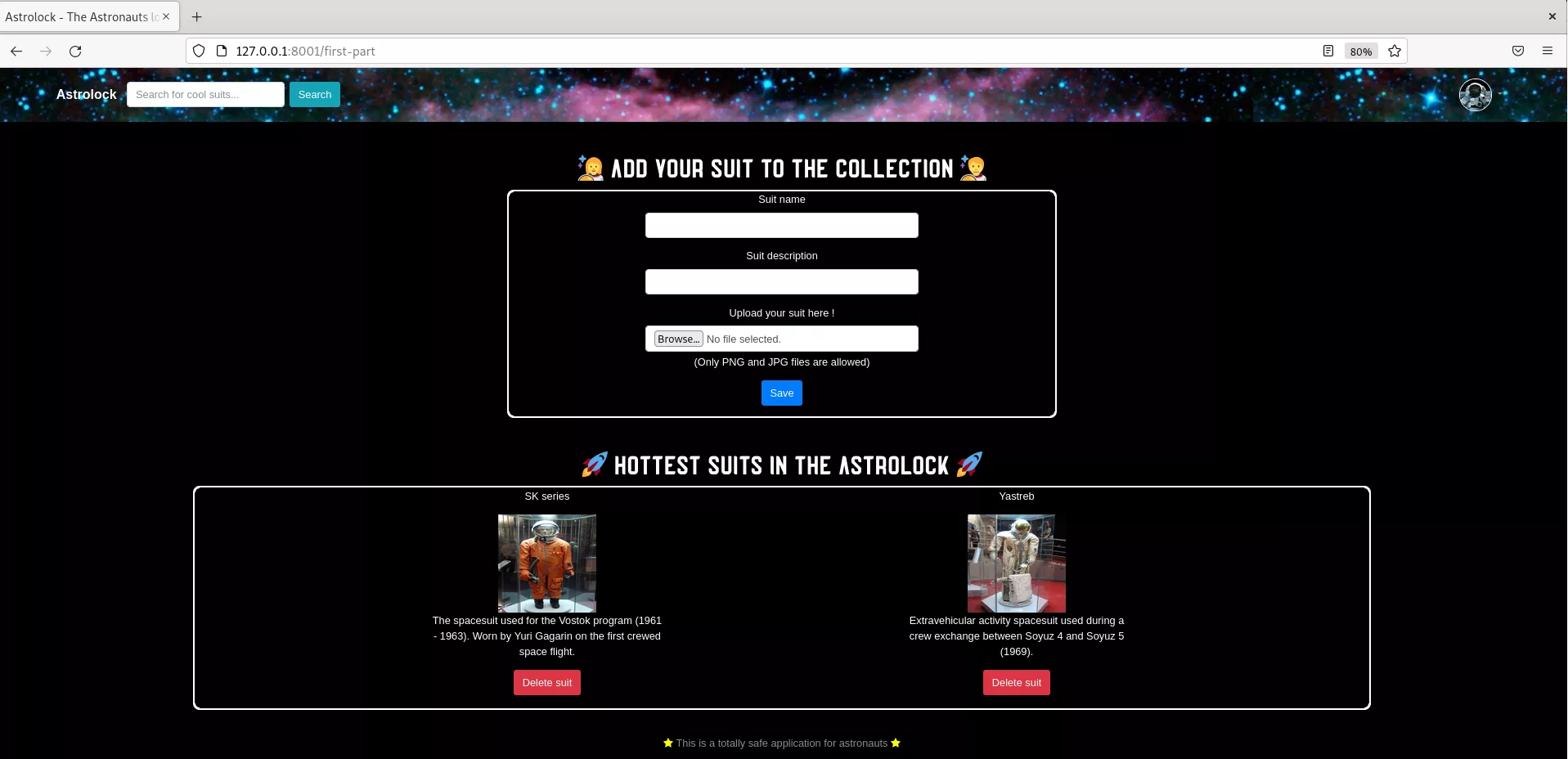
Persistent Php Payloads In Pngs How To Inject Php Code In An Image Many times, uploading a malicious file (such as a reverse shell) to the victim machine, and making it work, is not so obvious. the victim’s web administrator may have set filters to help determine the types of files that can be uploaded to their server. This known vulnerability walks us through (via the link mentioned above) on how to get the to interpret the php code via the newsletter template. the crucial thing is once you’ve updated your template, make sure you save it. Upload the file and visit the image’s url. the image will display and the php code will also execute. Attach imagenote: image must be jpeg format for exif. warning: due to the exif library used, payloads will be utf16 encoded which may lead to additional null bytes. set extension to (with .): make my payload! disclaimer: this tool is only to be used for legal uses such as ctf challenges.
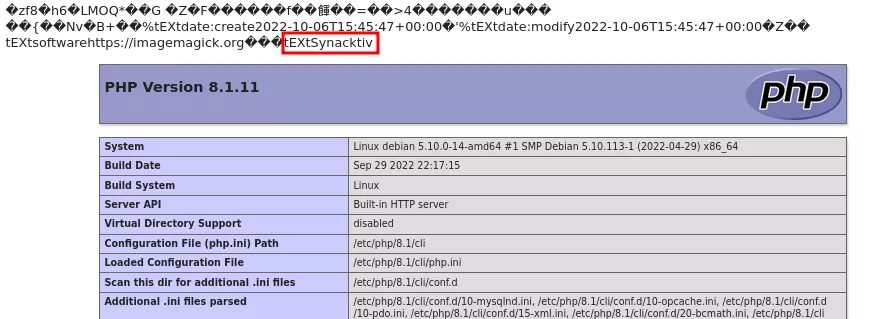
Persistent Php Payloads In Pngs How To Inject Php Code In An Image Upload the file and visit the image’s url. the image will display and the php code will also execute. Attach imagenote: image must be jpeg format for exif. warning: due to the exif library used, payloads will be utf16 encoded which may lead to additional null bytes. set extension to (with .): make my payload! disclaimer: this tool is only to be used for legal uses such as ctf challenges.
Persistent Php Payloads In Pngs How To Inject Php Code In An Image
Comments are closed.