Vulnerability Management Feature And Workflow Walkthrough

Key Features Your Vulnerability Management Platform Must Have The guide provides in depth coverage of the full vulnerability management lifecycle including the preparation phase, the vulnerability identification scanning phase, the reporting phase, and remediation phase. In this guide, we describe the process of vulnerability management in cybersecurity and outline its five stages. we also point out the features of the vulnerability management process, which make it an essential element in today’s security strategies.
Vulnerability Management Process Flow Chart Pdf Vulnerability Learn what vulnerability management is, what steps are involved in the process, and how you can implement a robust vulnerability management program that leverages automation. This walkthrough will show off some of gitlab's vulnerability management features. you will see how both a developer and security team member can use them in their workflows while. This article serves as a comprehensive guide to understanding, implementing, and optimizing vulnerability management workflows, offering actionable insights and proven strategies for success. Master the vulnerability management lifecycle in 6 steps and learn how automation reduces risk and response time.
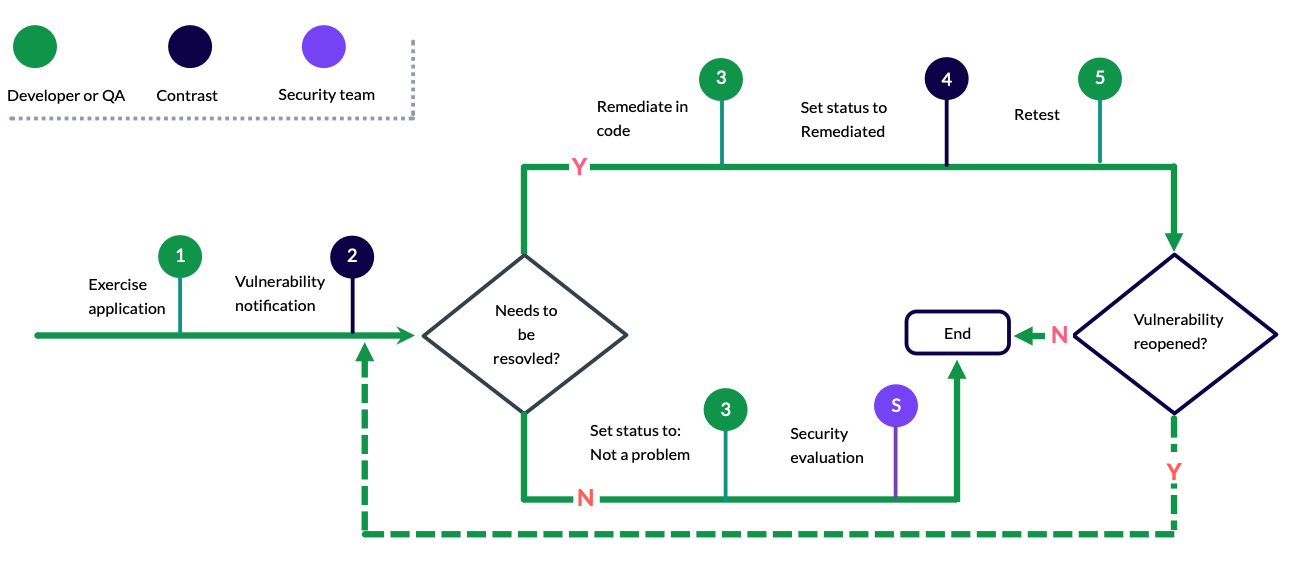
Vulnerability Management Workflow This article serves as a comprehensive guide to understanding, implementing, and optimizing vulnerability management workflows, offering actionable insights and proven strategies for success. Master the vulnerability management lifecycle in 6 steps and learn how automation reduces risk and response time. Learn the steps in vulnerability management, how to assess and prioritize risks, the best tools, and tips for a strong vulnerability management lifecycle. Learn about optimizing vulnerability management workflow in identifying, assessing, and mitigating vulnerabilities to strengthen your organization's security defenses. Vulnerability management is more than scanning and patching. it is a structured, repeatable process designed to help organizations reduce cyber risk across their environments. A vulnerability management workflow is a step by step process of identifying, assessing, prioritizing, and mitigating vulnerabilities in your systems. think of it as a roadmap that guides you through the entire lifecycle of vulnerability management.

Vulnerability Management Workflow Seemplicity Learn the steps in vulnerability management, how to assess and prioritize risks, the best tools, and tips for a strong vulnerability management lifecycle. Learn about optimizing vulnerability management workflow in identifying, assessing, and mitigating vulnerabilities to strengthen your organization's security defenses. Vulnerability management is more than scanning and patching. it is a structured, repeatable process designed to help organizations reduce cyber risk across their environments. A vulnerability management workflow is a step by step process of identifying, assessing, prioritizing, and mitigating vulnerabilities in your systems. think of it as a roadmap that guides you through the entire lifecycle of vulnerability management.

Vulnerability Management Workflow Seemplicity Vulnerability management is more than scanning and patching. it is a structured, repeatable process designed to help organizations reduce cyber risk across their environments. A vulnerability management workflow is a step by step process of identifying, assessing, prioritizing, and mitigating vulnerabilities in your systems. think of it as a roadmap that guides you through the entire lifecycle of vulnerability management.
Comments are closed.