Vulnerability Management Process Flow Chart Pdf Vulnerability
Vulnerability Management Process Flow Chart Pdf Vulnerability Vulnerability management process flow chart free download as word doc (.doc .docx), pdf file (.pdf), text file (.txt) or read online for free. The cyclical nature of vulnerability management implies continuous process improvement, and it is crucial to understand how a single process feeds into other processes and how all tasks are interconnected across three domains.

Vulnerability Management Process Pdf Security Computer Security This procedure aims to define detailed step by step cybersecurity requirements to asses vulnerabilities and protect

Vulnerability Analysis And Management Process Flow Introduction Pdf Explore cyberix’s vulnerability management process flow chart to identify, assess, and remediate security risks effectively for cyber resilience. In the design of the vulnerability management process, it’s important for assessment and prioritisation, as well as the enrichment of environment specific parameters of detected vulnerabilities, to take place in one process step. Here, a vulnerability management process flow chart is helpful. this blog introduces the top 7 vulnerability management process flow chart templates that you can use right after you hit the download button. The purpose of this procedure is to delineate the steps involved in it vulnerability management in accordance with the usg vulnerability management policy found in the usg it handbook. This resource guide was developed to help locate resources to help you gain a working knowledge of the vulnerability management process as well as identify best practices for incorporating them into your own program. The intent of this procedure is to establish a clear and efficient process for managing system vulnerabilities, ensuring the security and resilience of james cook university’s (jcu; the university) digital technology assets.
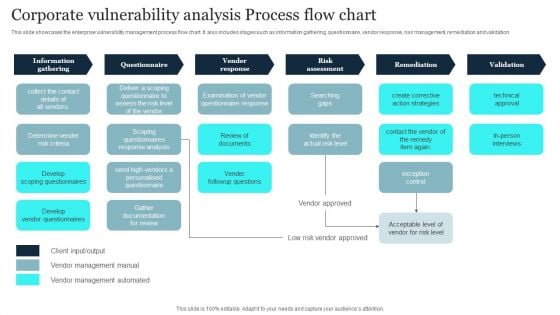
Corporate Vulnerability Analysis Process Flow Chart Summary Pdf Here, a vulnerability management process flow chart is helpful. this blog introduces the top 7 vulnerability management process flow chart templates that you can use right after you hit the download button. The purpose of this procedure is to delineate the steps involved in it vulnerability management in accordance with the usg vulnerability management policy found in the usg it handbook. This resource guide was developed to help locate resources to help you gain a working knowledge of the vulnerability management process as well as identify best practices for incorporating them into your own program. The intent of this procedure is to establish a clear and efficient process for managing system vulnerabilities, ensuring the security and resilience of james cook university’s (jcu; the university) digital technology assets.
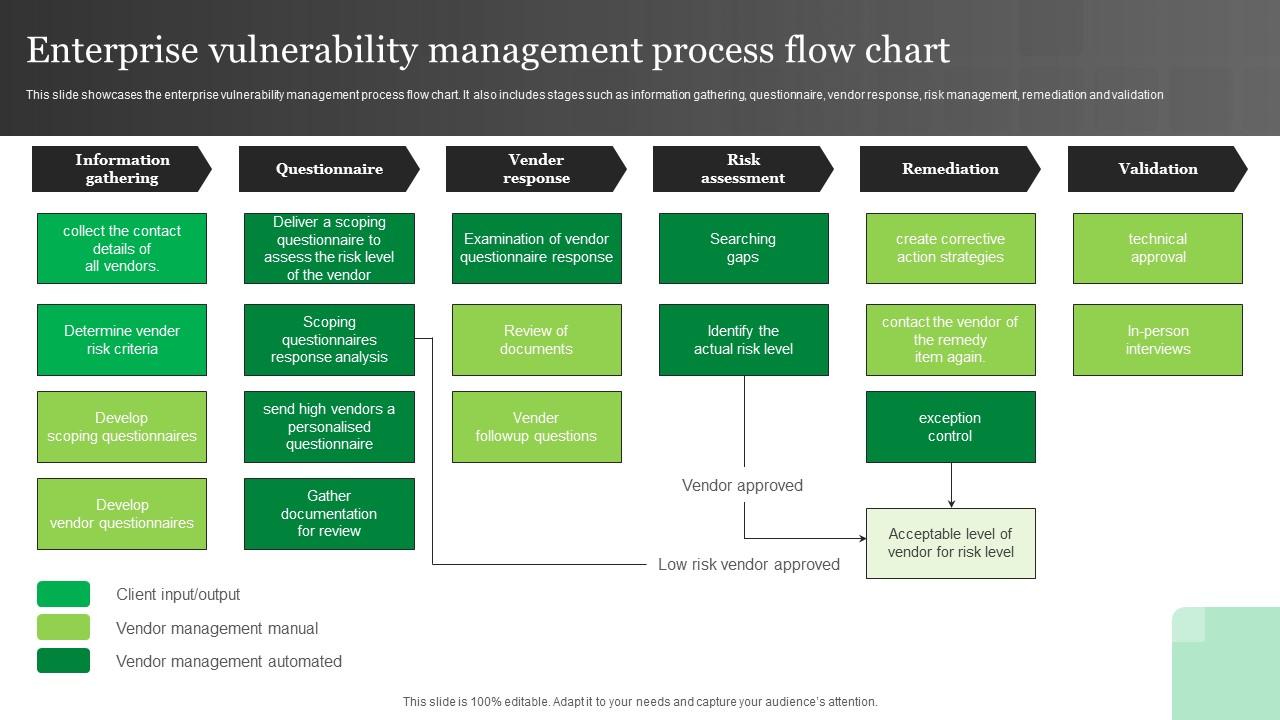
Enterprise Vulnerability Management Process Flow Chart Ppt Example This resource guide was developed to help locate resources to help you gain a working knowledge of the vulnerability management process as well as identify best practices for incorporating them into your own program. The intent of this procedure is to establish a clear and efficient process for managing system vulnerabilities, ensuring the security and resilience of james cook university’s (jcu; the university) digital technology assets.

Process Flow For Vulnerability Management In Startup Business Background Pd
Comments are closed.