Using Aws Identity And Access Management Access Analyzer

Using Aws Identity And Access Management Access Analyzer Pdf Amazon Learn about how aws identity and access management access analyzer analyzes resource based policies to identify unintended access. Using aws identity and access management access analyzer – step by step instructions for configuring and using access analyzer. 9 best practices for using aws access.
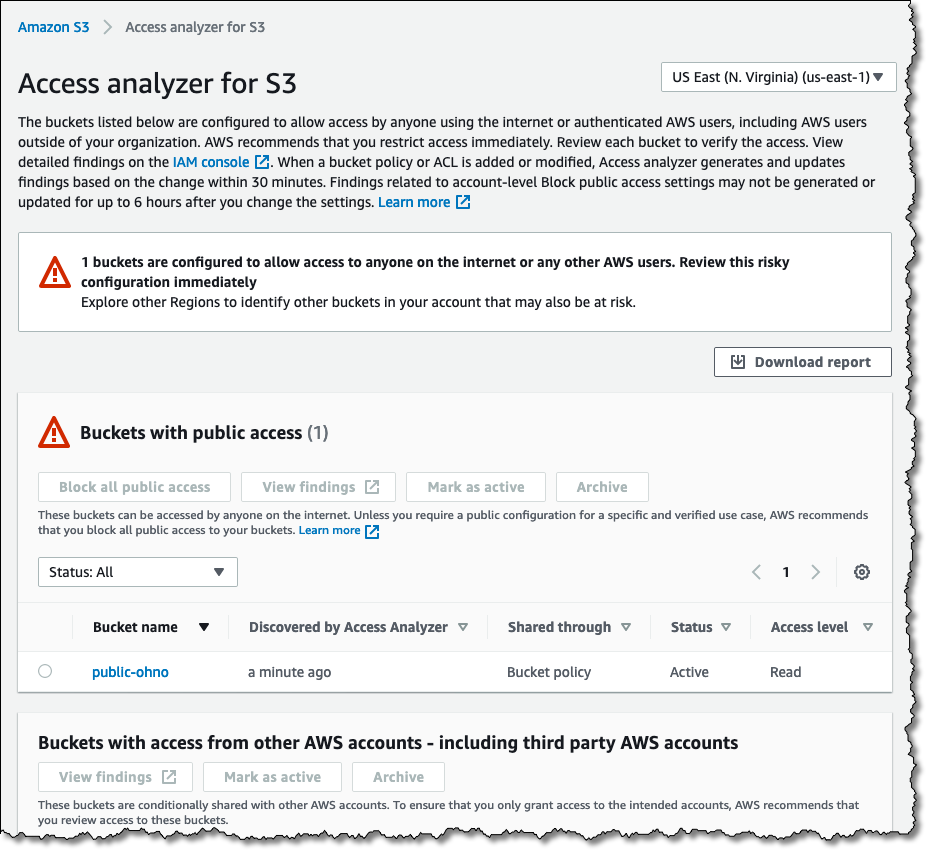
Using Aws Identity And Access Management Access Analyzer In this hands on cloud lab, you’ll use iam access analyzer to identify resources with overly permissive policies that allow access to external entities. using this service, you’ll also generate a fine grained policy for an iam user. This guide describes the iam access analyzer operations that you can call programmatically. for general information about iam access analyzer, see using amazon identity and access management access analyzer in the iam user guide. this document was last published on april 23, 2026. To monitor external access to resources across your organization, use your organization's management account to create external access analyzers in each aws region. This article explores how you can use aws iam access analyzer to check compliance with aws security best practices, what features facilitate this process, and practical steps to enhance your cloud security posture.
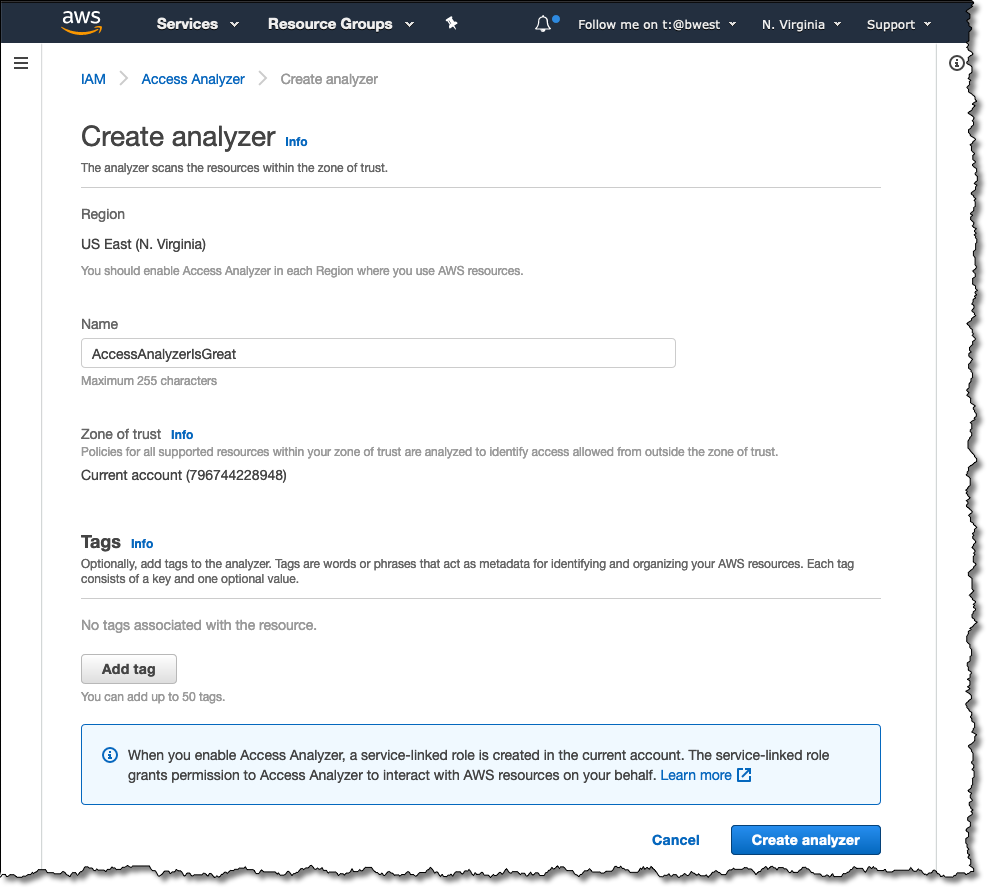
Identify Unintended Resource Access With Aws Identity And Access To monitor external access to resources across your organization, use your organization's management account to create external access analyzers in each aws region. This article explores how you can use aws iam access analyzer to check compliance with aws security best practices, what features facilitate this process, and practical steps to enhance your cloud security posture. In this post, we explored aws iam access analyzer—how it works and why it’s a valuable service. we provided a straightforward guide to creating and using access analyzer, simplifying the process and highlighting its benefits. In this course, you will learn the benefits and technical concepts of iam access analyzer. if you are new to the feature, you will learn how to start using iam access analyzer through a demonstration using the aws management console. In this series you can learn how to apply the best practices and automate the process using iam access analyzer and amazon boto3 sdk to automate the validation process with aws developer tools. You can proactively identify and resolve any overly permissive access policies by leveraging aws access analyzer to protect your sensitive data and help you avoid costly data breaches and compliance violations.
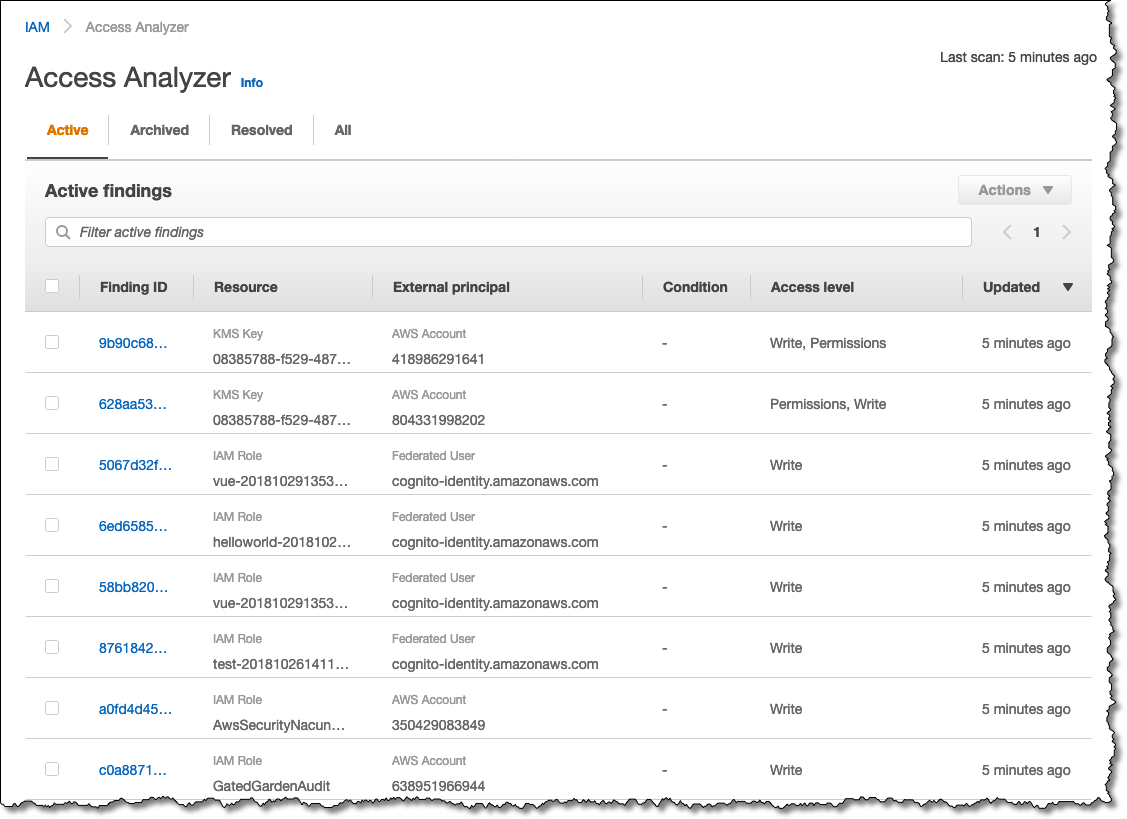
Identify Unintended Resource Access With Aws Identity And Access In this post, we explored aws iam access analyzer—how it works and why it’s a valuable service. we provided a straightforward guide to creating and using access analyzer, simplifying the process and highlighting its benefits. In this course, you will learn the benefits and technical concepts of iam access analyzer. if you are new to the feature, you will learn how to start using iam access analyzer through a demonstration using the aws management console. In this series you can learn how to apply the best practices and automate the process using iam access analyzer and amazon boto3 sdk to automate the validation process with aws developer tools. You can proactively identify and resolve any overly permissive access policies by leveraging aws access analyzer to protect your sensitive data and help you avoid costly data breaches and compliance violations.

Identify Unintended Resource Access With Aws Identity And Access In this series you can learn how to apply the best practices and automate the process using iam access analyzer and amazon boto3 sdk to automate the validation process with aws developer tools. You can proactively identify and resolve any overly permissive access policies by leveraging aws access analyzer to protect your sensitive data and help you avoid costly data breaches and compliance violations.
Identify Unintended Resource Access With Aws Identity And Access
Comments are closed.