Aws Iam Access Analyzer Tutorial Internal Access Analysis Demo
Using Aws Identity And Access Management Access Analyzer It uses automated reasoning across scps, rcps, and identity based policies to surface internal access findings in a clean, unified dashboard. You must create an internal access analyzer in each region in which you want to monitor access to your resources. iam access analyzer charges for internal access analysis based on the number of resources monitored per analyzer per month.
Aws Iam Access Analyzer Tutorial Internal Access Analysis It uses automated reasoning across scps, rcps, and identity based policies to surface internal access findings in a clean, unified dashboard. if you’re serious about least privilege and audit readiness, this is a must try. Aws iam access analyzer helps you identify the resources in your organization and accounts, such as amazon s3 buckets or iam roles, that are shared with an external entity. To start using iam access analyzer to identify external, internal, or unused access, you first need to create an analyzer. external access analyzers help you identify potential risks of accessing resources by enabling you to identify any resource policies that grant access to an external principal. Access analyzer helps security teams identify and mitigate risks by analyzing resource based and iam policies to detect unintended public or cross account access.
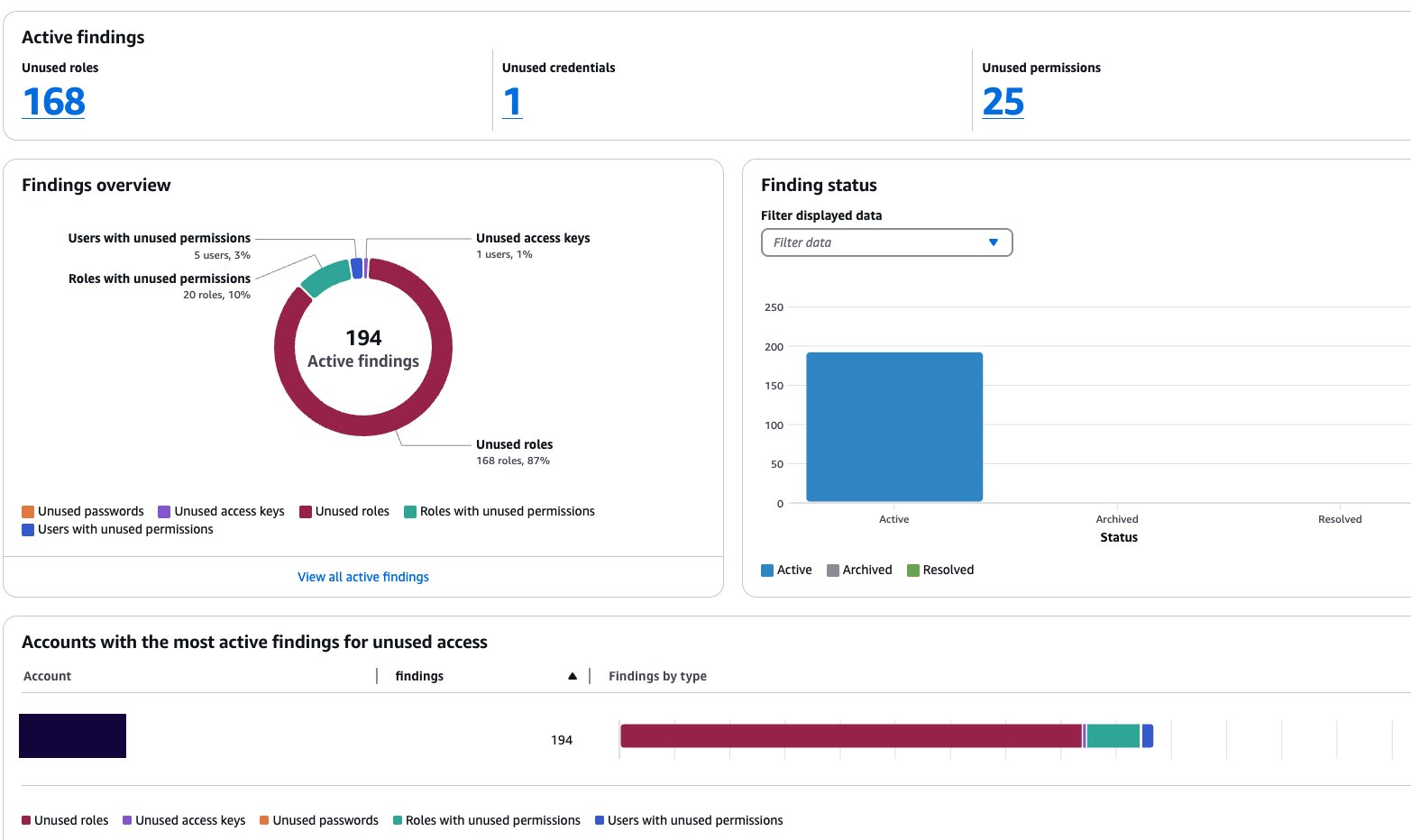
Customize The Scope Of Iam Access Analyzer Unused Access Analysis Aws To start using iam access analyzer to identify external, internal, or unused access, you first need to create an analyzer. external access analyzers help you identify potential risks of accessing resources by enabling you to identify any resource policies that grant access to an external principal. Access analyzer helps security teams identify and mitigate risks by analyzing resource based and iam policies to detect unintended public or cross account access. After the new internal access analyzer is enabled in the iam console, the analyzer monitors your selected resources daily, and surfaces findings in a unified dashboard. In this hands on guide, i’ll show you exactly how to set up and use iam access analyzer to catch security misconfigurations before they become headlines. Important: to successfully complete this example, you must first deploy the module by following module workspace example. follow the steps below to attach the run task created from the module into a new hcp terraform workspace. the new workspace will attempt to create multiple invalid iam resources. Aws identity and access management (iam) access analyzer is a powerful tool designed to help administrators identify unintended resource access by analysing policies attached to aws resources.
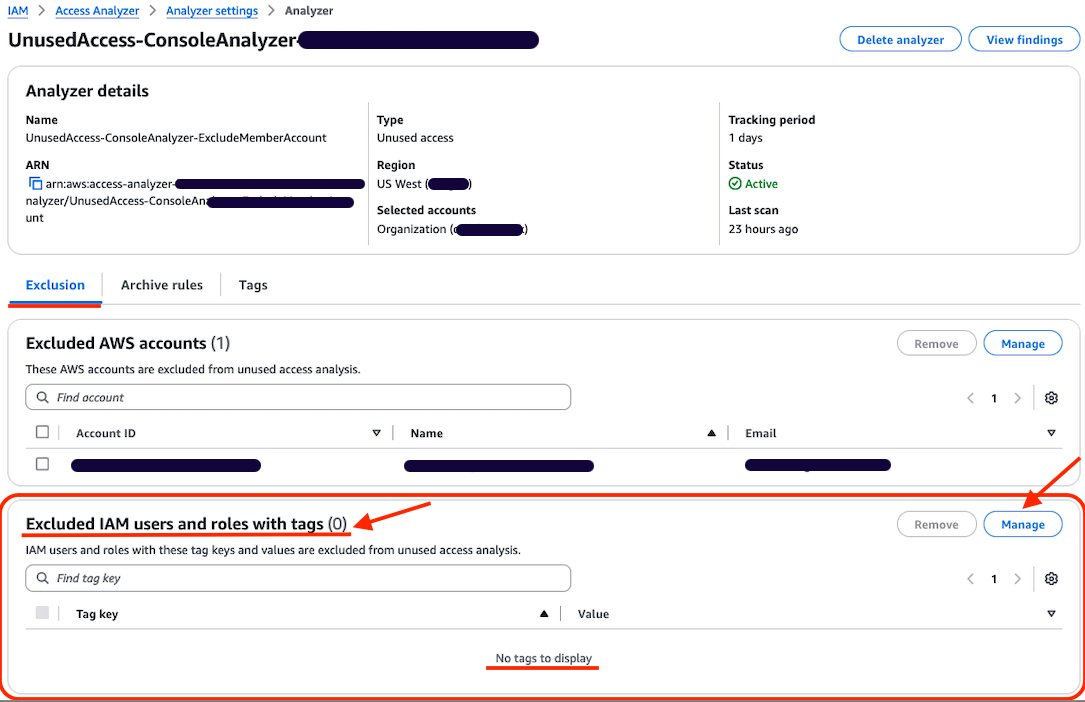
Customize The Scope Of Iam Access Analyzer Unused Access Analysis Aws After the new internal access analyzer is enabled in the iam console, the analyzer monitors your selected resources daily, and surfaces findings in a unified dashboard. In this hands on guide, i’ll show you exactly how to set up and use iam access analyzer to catch security misconfigurations before they become headlines. Important: to successfully complete this example, you must first deploy the module by following module workspace example. follow the steps below to attach the run task created from the module into a new hcp terraform workspace. the new workspace will attempt to create multiple invalid iam resources. Aws identity and access management (iam) access analyzer is a powerful tool designed to help administrators identify unintended resource access by analysing policies attached to aws resources.
Customize The Scope Of Iam Access Analyzer Unused Access Analysis Aws Important: to successfully complete this example, you must first deploy the module by following module workspace example. follow the steps below to attach the run task created from the module into a new hcp terraform workspace. the new workspace will attempt to create multiple invalid iam resources. Aws identity and access management (iam) access analyzer is a powerful tool designed to help administrators identify unintended resource access by analysing policies attached to aws resources.
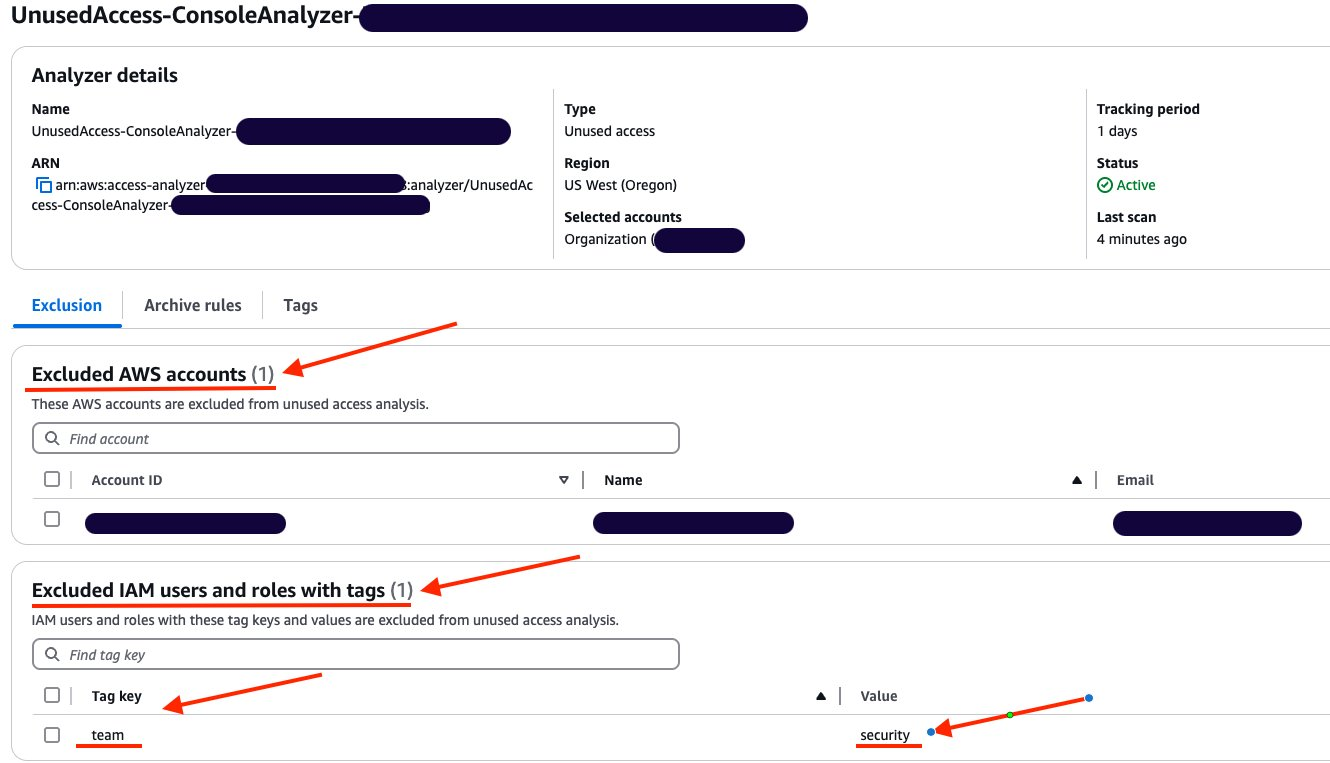
Customize The Scope Of Iam Access Analyzer Unused Access Analysis Aws
Comments are closed.