Understanding Identity In Zero Trust 192 Intel Business
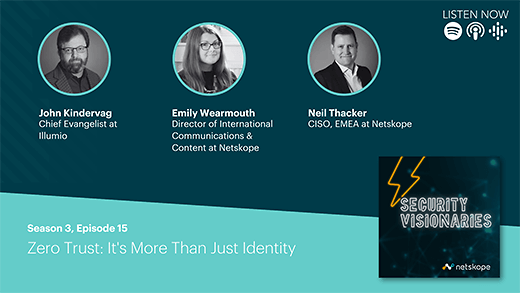
Podcast Exploring Misconceptions Of Identity Zero Trust Netskope In this episode, darren interviews jeff reich, executive director of the identity defined security alliance, about the role identity plays in zero trust architectures and in our digital. Catch this episode of the embracing digital transformation podcast, hosted by darren pulsipher, as jeff reich digs into the complexities of identity in technology, including software, emerging.

Zero Trust Identity And Security Identities, representing people, services, or devices, are the common denominator across today’s many networks, endpoints, and applications. in the zero trust security model, they function as a powerful, flexible, and granular way to control access to data. Zero trust cloud security requires a dynamic approach to identity and access management (iam). the right users or devices must be given access to the right resources. conversely, unauthorized users and devices must be blocked. In this post, we’ll review what zero trust is, explain the types of identities that are at the heart of it, and review the steps and best practices for building an effective zero trust identity strategy. Zero trust is a security paradigm that replaces access based on implicit trust with access based on continuously updated identity and context. this facilitates securely connecting end users or other entities to resources.

The Path To Zero Trust Starts With Identity In this post, we’ll review what zero trust is, explain the types of identities that are at the heart of it, and review the steps and best practices for building an effective zero trust identity strategy. Zero trust is a security paradigm that replaces access based on implicit trust with access based on continuously updated identity and context. this facilitates securely connecting end users or other entities to resources. In the cisa zero trust model, the identity pillar is introduced first (and rightly so). identity is core to zero trust, as it triggers the entire transaction flow of an entity acting on data; nothing happens from an event perspective until an identity requests to act on data. This article is your comprehensive guide to understanding the role of identity within zta, its benefits, and how leveraging netfoundry can accelerate the journey toward zero trust maturity. This document contains an abstract definition of zero trust architecture (zta) and gives general deployment models and use cases where zero trust could improve an enterprise’s overall information technology security posture. In contrast to the perimeter based security model that considers anything from inside the corporate network to be secure and trustworthy, zero trust assumes that no user or device can be inherently trusted.

Business Zero Trust Authentication Authtake In the cisa zero trust model, the identity pillar is introduced first (and rightly so). identity is core to zero trust, as it triggers the entire transaction flow of an entity acting on data; nothing happens from an event perspective until an identity requests to act on data. This article is your comprehensive guide to understanding the role of identity within zta, its benefits, and how leveraging netfoundry can accelerate the journey toward zero trust maturity. This document contains an abstract definition of zero trust architecture (zta) and gives general deployment models and use cases where zero trust could improve an enterprise’s overall information technology security posture. In contrast to the perimeter based security model that considers anything from inside the corporate network to be secure and trustworthy, zero trust assumes that no user or device can be inherently trusted.

Intel Business On Linkedin Full Confidence In Zero Trust This document contains an abstract definition of zero trust architecture (zta) and gives general deployment models and use cases where zero trust could improve an enterprise’s overall information technology security posture. In contrast to the perimeter based security model that considers anything from inside the corporate network to be secure and trustworthy, zero trust assumes that no user or device can be inherently trusted.
Comments are closed.