Ultimate Guide To Secure Remote Access

Secure Remote Access Pdf Computer Network Desktop Virtualization This comprehensive secure remote access guide outlines the strategies, tools and best practices to provide anywhere access while protecting data, systems and users. So, it’s time to explore why secure remote access is the future of any digitized business and prepare you to adopt it the right way. that’s why we’ll also discuss its key components, including virtual private network, mfa, and endpoint security.
Secure Remote Access Technical Solution Guide Enabling Application Ip Practical guide to remote access security covering vpn, ssh, and rdp hardening; zero trust implementation; and session monitoring to stop credential based attacks. Secure remote access refers to the methods, technologies, and policies used to protect data and resources when accessing a network or system from a remote location. it ensures that only authorized users can connect and that their data is protected from unauthorized access or interception. A comprehensive guide for admins on what secure remote access is, how it can keep your critical systems secure, and the recommended best practices to design and build a robust remote access strategy. Cyber threat actors use remote access software for initial access, maintaining persistence, deploying additional software and tools, lateral movement, and data exfiltration.

Remote Access Portal User Guide Pdf Ios Desktop Virtualization A comprehensive guide for admins on what secure remote access is, how it can keep your critical systems secure, and the recommended best practices to design and build a robust remote access strategy. Cyber threat actors use remote access software for initial access, maintaining persistence, deploying additional software and tools, lateral movement, and data exfiltration. Secure remote access best practices fall into several broad categories: authentication and access controls, device and network security, data protection and monitoring, user training and audits. In this comprehensive rdp security guide, you’ll discover the most effective ways to secure your rdp sessions, prevent unauthorized access, and reduce rdp vulnerabilities—whether you’re working from the cloud, on premises, or a hybrid environment. Remote access security with strong authentication, zero trust, and encryption. learn best practices to protect users, devices, and data from cyber threats. This guide provides a foundational understanding of remote access solutions, helping you to make informed decisions and implement effective strategies for your organization.

The Essential Guide To Securing Remote Access Secure remote access best practices fall into several broad categories: authentication and access controls, device and network security, data protection and monitoring, user training and audits. In this comprehensive rdp security guide, you’ll discover the most effective ways to secure your rdp sessions, prevent unauthorized access, and reduce rdp vulnerabilities—whether you’re working from the cloud, on premises, or a hybrid environment. Remote access security with strong authentication, zero trust, and encryption. learn best practices to protect users, devices, and data from cyber threats. This guide provides a foundational understanding of remote access solutions, helping you to make informed decisions and implement effective strategies for your organization.
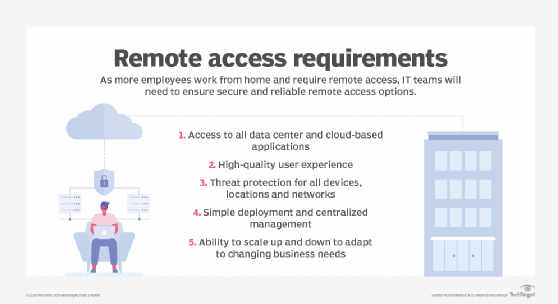
Ultimate Guide To Secure Remote Access Remote access security with strong authentication, zero trust, and encryption. learn best practices to protect users, devices, and data from cyber threats. This guide provides a foundational understanding of remote access solutions, helping you to make informed decisions and implement effective strategies for your organization.
Comments are closed.