Secure Remote Access Pdf Computer Network Desktop Virtualization

Network Virtualization Pdf Computer Network Networking The document outlines the importance of secure remote access for protecting sensitive data as remote work increases. it discusses various remote access methods, including vpn, rdp, vdi, and cloud based solutions, along with their benefits and technical details. This publication provides information on security considerations for several types of remote access solutions, and it makes recommendations for securing a variety of telework, remote access, and byod technologies. it also gives advice on creating related security policies.

Remote Access To Lan Softether Vpn Project Pdf Virtual Private Remote working necessitated the use of virtual desktops and remote access securely to continue working and upholding a cybersecurity posture. Exploring desktop virtualization's benefits, drawbacks, various forms, impact on contemporary workplaces, and potential future trends are the main objectives. the advantages of desktop virtualization are emphasized in the report, including increased productivity, cost savings, and improved security. Remote access software provides it ot teams with flexible ways to detect anomalous network or device issues early on and proactively monitor systems. cyber threat actors are increasingly co opting these same tools for easy and broad access to victim systems. All the components of telework and remote access solutions, including client devices, remote access servers, and internal resources accessed through remote access, should be secured against expected threats, as identified through threat models.

Secure Remote Desktop Access For Complex Hybrid Infrastructures Remote access software provides it ot teams with flexible ways to detect anomalous network or device issues early on and proactively monitor systems. cyber threat actors are increasingly co opting these same tools for easy and broad access to victim systems. All the components of telework and remote access solutions, including client devices, remote access servers, and internal resources accessed through remote access, should be secured against expected threats, as identified through threat models. Remote desktop access is built over a secure network communication protocol, like microsoft rdp, designed for remote access to virtual desktops and applications. Soliton supports companies with their security management challenges, including network security and remote access to internal and cloud applications. soliton’s solutions protect the company’s resources from unauthorised access and accidental data leakage. Providing a remote access proxy option combined with sso improves the flexibility, agility and scalability of application access and enables organizations to provide remote access without exposing internal applications directly to the internet, reducing risk of attack. Luckily, inside this exclusive guide, our experts provide key criteria to utilize when evaluating remote desktop access software and explore essential tips on leveraging that software as part of an effective remote access security strategy.

Understanding Virtual Desktop Infrastructure For Remote Access Remote desktop access is built over a secure network communication protocol, like microsoft rdp, designed for remote access to virtual desktops and applications. Soliton supports companies with their security management challenges, including network security and remote access to internal and cloud applications. soliton’s solutions protect the company’s resources from unauthorised access and accidental data leakage. Providing a remote access proxy option combined with sso improves the flexibility, agility and scalability of application access and enables organizations to provide remote access without exposing internal applications directly to the internet, reducing risk of attack. Luckily, inside this exclusive guide, our experts provide key criteria to utilize when evaluating remote desktop access software and explore essential tips on leveraging that software as part of an effective remote access security strategy.
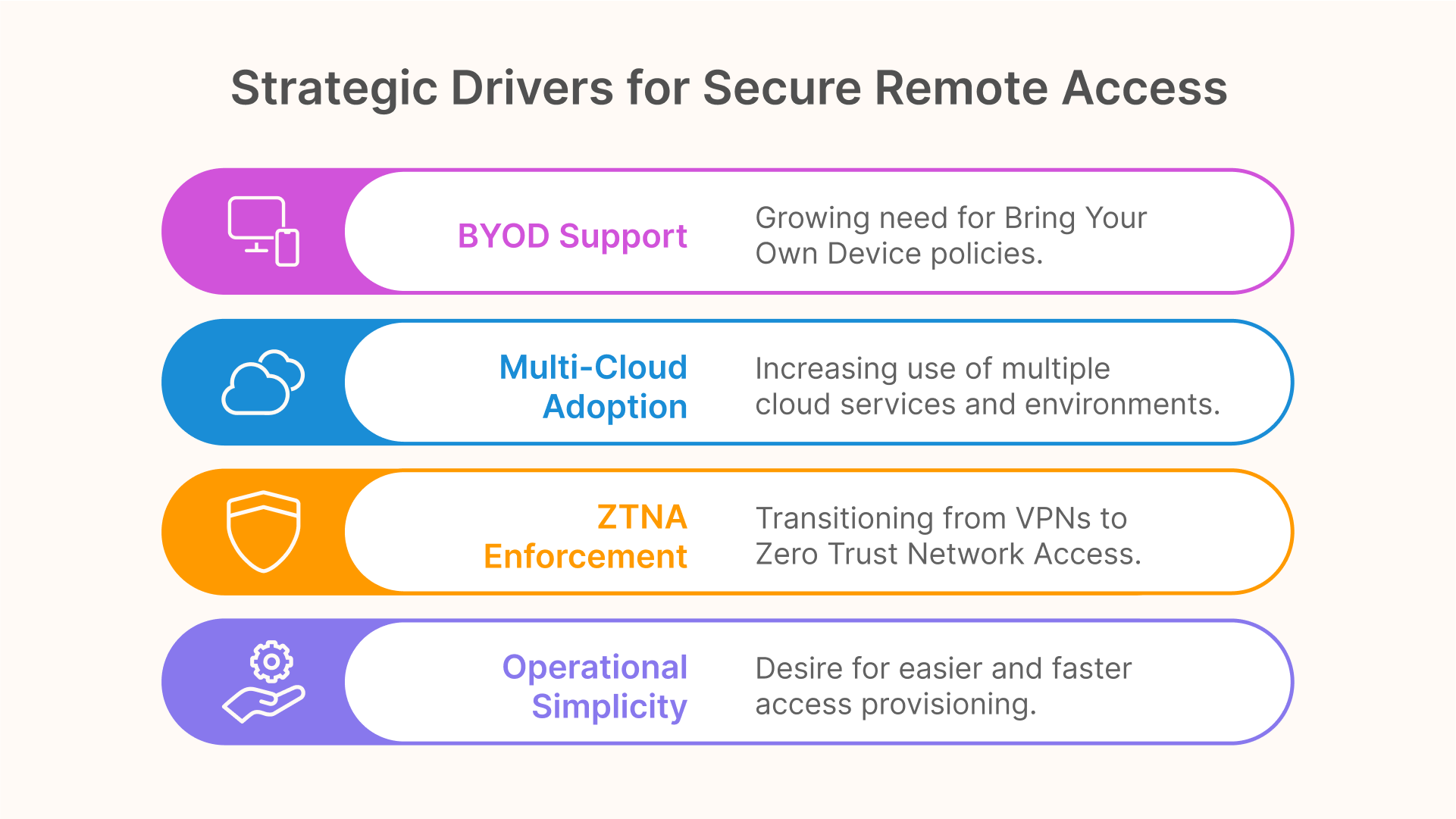
Secure Remote Desktop In 2025 5 Strategic Priorities For Zero Trust Providing a remote access proxy option combined with sso improves the flexibility, agility and scalability of application access and enables organizations to provide remote access without exposing internal applications directly to the internet, reducing risk of attack. Luckily, inside this exclusive guide, our experts provide key criteria to utilize when evaluating remote desktop access software and explore essential tips on leveraging that software as part of an effective remote access security strategy.

Desktop Virtualization Pdf Desktop Virtualization Virtualization
Comments are closed.