Trustless Decentralized Access Control

Decentralized Access Control Mechanism With Temporal Dimension Based On Traditional systems rely on centralized administrators to manage permissions. in contrast, decentralized systems depend on immutable code and trustless execution. because of this, even a small flaw in access control can cause irreversible damage. Interoperability among heterogeneous blockchain platforms remains a significant challenge in decentralized ecosystems, especially with the growing adoption of blockchain across various industries. this research introduces the data standardization module (dsm).

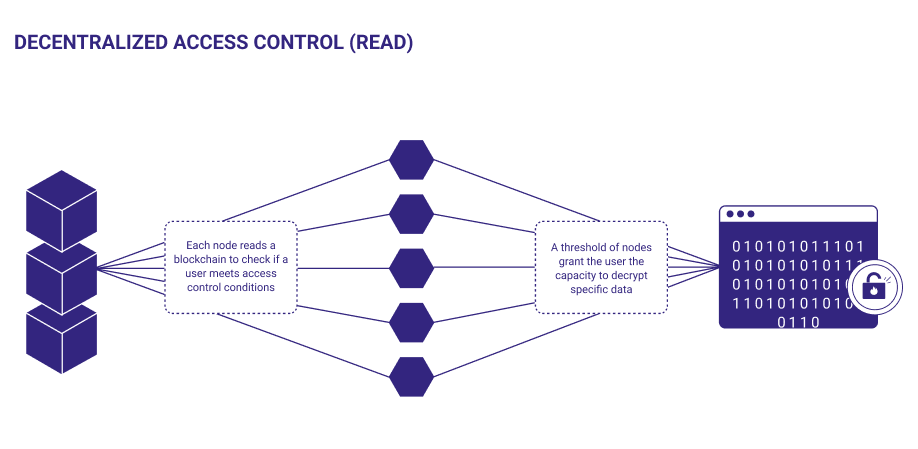
Introduction To Decentralized Access Control Decentralized access control moves permission management from centralized servers to the blockchain, enabling trustless and transparent governance over resources and functions. To this end, our paper proposes a fine grained decentralized autonomous access control scheme based on blockchain, which includes three core stages: formulation, deployment, and execution of access control policies. In this paper, we investigate the authorization process that manages permissions and rights of access to shared services in a federation of enterprises and we propose a solution based on the ethereum blockchain platform and the attribute based access control model (abac) to define this authorization process. We propose a novel solution named chainguard, a fully decentralized authentication and access control mechanism based on smart contracts. chainguard eliminates the need for a central server by leveraging blockchain technology to manage user roles and permissions dynamically.

1 Decentralized Access Control System Download Scientific Diagram In this paper, we investigate the authorization process that manages permissions and rights of access to shared services in a federation of enterprises and we propose a solution based on the ethereum blockchain platform and the attribute based access control model (abac) to define this authorization process. We propose a novel solution named chainguard, a fully decentralized authentication and access control mechanism based on smart contracts. chainguard eliminates the need for a central server by leveraging blockchain technology to manage user roles and permissions dynamically. This article delves into the future of access control in decentralized systems, exploring emerging trends and technologies that promise to redefine how we secure data and manage user access in these environments. Described are systems and techniques for leveraging a virtual distributed trustless database using access enabling codes. the computations use private codes. each computation includes the. Systems and techniques for leveraging a virtual distributed trustless database using access enabling codes. the computations use private codes. each computation includes the information from all previous computations so that a chain of computations is maintained and controlled. a central system insures that dual computations do not occur. Geoblocks: trustless geospatial data sharing with accountability and decentralized access control this repository contains the implementation of geoblocks protocol introduced in the paper geoblocks [brains'24].
Working With Decentralized Access Control This article delves into the future of access control in decentralized systems, exploring emerging trends and technologies that promise to redefine how we secure data and manage user access in these environments. Described are systems and techniques for leveraging a virtual distributed trustless database using access enabling codes. the computations use private codes. each computation includes the. Systems and techniques for leveraging a virtual distributed trustless database using access enabling codes. the computations use private codes. each computation includes the information from all previous computations so that a chain of computations is maintained and controlled. a central system insures that dual computations do not occur. Geoblocks: trustless geospatial data sharing with accountability and decentralized access control this repository contains the implementation of geoblocks protocol introduced in the paper geoblocks [brains'24].
Comments are closed.