Decentralized Access Control With Anonymous

Decentralized Access Control Mechanism With Temporal Dimension Based On Abstract: in this paper, a new decentralized access control scheme for secure data storage in clouds that supports anonymous authentication is proposed. in the proposed scheme, the cloud verifies the authenticity of the series without knowing the user’s identity before storing data. We propose a new decentralized access control scheme for secure data storage in clouds that supports anonymous authentication. in the proposed scheme, the cloud verifies the authenticity of the series without knowing the user's identity before storing data.

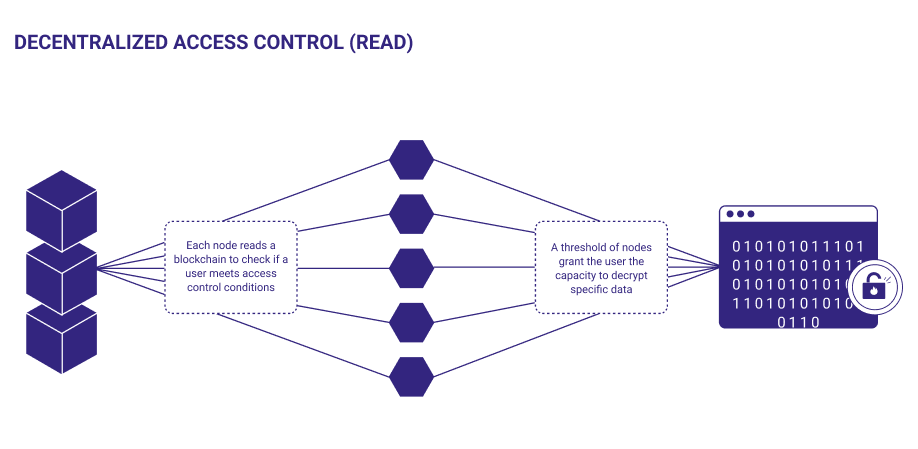
Introduction To Decentralized Access Control Abstract ts while ensuring anonymous authentication. unlike traditional centralized systems, the proposed model allows the cloud to verify user authenticity without reveal ng the user's identity before storing data. although the system leverages symmetric key encryption, particularly aes 256, it ensures that only authorized users ca. To address these issues, this paper proposes an identity authentication mechanism leveraging dual blockchain and decentralized identifier (did) technology. in the proposed mechanism, we develop a lightweight authentication scheme for devices. A decentralized access control method with anonymous authentication, user revocation, and replay protection has been described. the cloud just verifies the user's credentials and doesn't know who stores the data. We propose a new decentralized access control scheme for secure data storage in clouds that supports anonymous authentication. in the proposed scheme, the cloud verifies the authenticity of.

1 Decentralized Access Control System Download Scientific Diagram A decentralized access control method with anonymous authentication, user revocation, and replay protection has been described. the cloud just verifies the user's credentials and doesn't know who stores the data. We propose a new decentralized access control scheme for secure data storage in clouds that supports anonymous authentication. in the proposed scheme, the cloud verifies the authenticity of. We propose a new decentralized access control scheme for secure data storage in clouds that supports anonymous authentication. Abstract—we propose a new decentralized access control scheme for secure data storage in clouds, that supports anonymous authenti cation. in the proposed scheme, the cloud verifies the authenticity of the ser without knowing the user’s identity before storing data. In particular, this means that access to customer data is under its control and is only granted to parties it trusts. in a public cloud the infrastructure is owned and managed by a cloud service provider. In this paper, we present an anonymous and decentralized attribute based access control with untrusted authorities in the standard security model where the users may collude with the untrusted authorities.

Decentralized Access Control With Anonymous We propose a new decentralized access control scheme for secure data storage in clouds that supports anonymous authentication. Abstract—we propose a new decentralized access control scheme for secure data storage in clouds, that supports anonymous authenti cation. in the proposed scheme, the cloud verifies the authenticity of the ser without knowing the user’s identity before storing data. In particular, this means that access to customer data is under its control and is only granted to parties it trusts. in a public cloud the infrastructure is owned and managed by a cloud service provider. In this paper, we present an anonymous and decentralized attribute based access control with untrusted authorities in the standard security model where the users may collude with the untrusted authorities.
Working With Decentralized Access Control In particular, this means that access to customer data is under its control and is only granted to parties it trusts. in a public cloud the infrastructure is owned and managed by a cloud service provider. In this paper, we present an anonymous and decentralized attribute based access control with untrusted authorities in the standard security model where the users may collude with the untrusted authorities.

Web3 Decentralized Access Control For Better Security
Comments are closed.