Tag Side Channel Attacks Ars Technica

Tag Side Channel Attacks Ars Technica Hackers can clone google titan 2fa keys using a side channel in nxp chips yubico and feitian keys that use the same chip are likely susceptible, too. All non google chat gpts affected by side channel that leaks responses sent to users. a previously unknown compression side channel in gpus can expose images thought to be private .
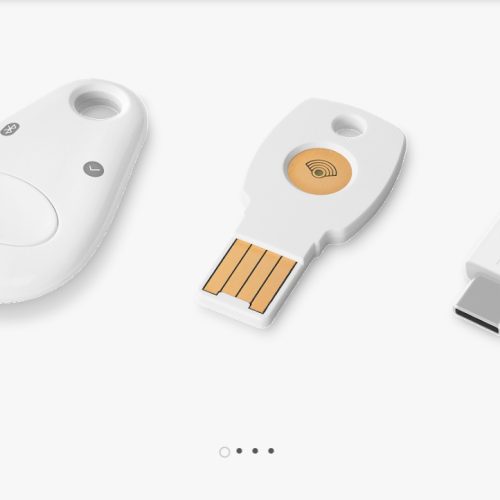
Tag Side Channel Attacks Ars Technica To uncover the side channel, the researchers reverse engineered the infineon cryptographic library, a heavily fortified collection of code that the manufacturer takes great pains to keep. Keeping track of physical tokens has been a thing for users of physical tokens for decades now, for a multitude of reasons, not the least of which is control. the newsworthiness part is the new. Side channel vulnerabilities are unfortunately common. and this isn't even the first time yubico has been affected by an infineon vulnerability look up the roca vulnerability for an earlier. This study exposes a critical vulnerability in ai assistants like openai’s chatgpt 4 and microsoft’s copilot through a novel token length side channel attack, achieving significant success in reconstructing and inferring encrypted responses.

Understanding Side Channel Attacks Power Timing Analysis Cyber Snowden Side channel vulnerabilities are unfortunately common. and this isn't even the first time yubico has been affected by an infineon vulnerability look up the roca vulnerability for an earlier. This study exposes a critical vulnerability in ai assistants like openai’s chatgpt 4 and microsoft’s copilot through a novel token length side channel attack, achieving significant success in reconstructing and inferring encrypted responses. In this paper, we provide a comprehensive survey of power side channel attacks and their countermeasures in different application domains. specifically, this survey aims to classify recent power side channel attacks and provide a comprehensive comparison based on application specific considerations. In computer security, a side channel attack is a type of security exploit that uses information inadvertently leaked by a system—such as timing, power consumption, or electromagnetic or acoustic emissions—to gain unauthorized access to sensitive information. In this paper, we introduce controlled channel attacks, a new type of side channel attack that allows an untrusted operating system to extract large amounts of sensitive information from protected applications on systems like overshadow, ink tag or haven. The side channel protection was based on a threshold masking scheme (3 shares, should offer security against standard differential attacks, evaluated by tvla, which we’ll cover in part 2).

Tag Side Channel Attack Ars Technica In this paper, we provide a comprehensive survey of power side channel attacks and their countermeasures in different application domains. specifically, this survey aims to classify recent power side channel attacks and provide a comprehensive comparison based on application specific considerations. In computer security, a side channel attack is a type of security exploit that uses information inadvertently leaked by a system—such as timing, power consumption, or electromagnetic or acoustic emissions—to gain unauthorized access to sensitive information. In this paper, we introduce controlled channel attacks, a new type of side channel attack that allows an untrusted operating system to extract large amounts of sensitive information from protected applications on systems like overshadow, ink tag or haven. The side channel protection was based on a threshold masking scheme (3 shares, should offer security against standard differential attacks, evaluated by tvla, which we’ll cover in part 2).

Tag Side Channel Attack Ars Technica In this paper, we introduce controlled channel attacks, a new type of side channel attack that allows an untrusted operating system to extract large amounts of sensitive information from protected applications on systems like overshadow, ink tag or haven. The side channel protection was based on a threshold masking scheme (3 shares, should offer security against standard differential attacks, evaluated by tvla, which we’ll cover in part 2).
Comments are closed.