Pdf Side Channel Attacks

Side Channel Attacks Mdpi Books In this lecture, we will explore the history, examples, and countermeasures of side channel attacks. in 1945, at the end of world war ii, the soviet union gave a great seal as a gift to a us ambassador. this seal was placed in the ambassador's residence, and it contained a passive listening device. Side channel attacks remain a technique that can break the security protection via exploiting non functional behaviors. this study focused on various parametric attacks, like time analysis.

Side Channel Attacks Explained All You Need To Know Rambus The 13 papers in this special issue can be classified into the following four research themes: power analysis attacks and countermeasures, cache based timing attacks, system level countermeasures and their weaknesses, and recent technologies in the field of side channel attacks. Outline what are side channel attacks (scas)? which adversary models are suitable for scas? which types of attacks exists? how do these attacks work precisely?. Abstract side channel attacks are easy to implement whilst powerful attacks against cryptographic implementations, and their targets range from primitives, protocols, modules, and devices to even systems. these attacks pose a serious threat to the security of cryptographic modules. In this presentation, we o er a comprehensive overview of side channel analyses, and describe their power in ariousv real world scenarios. we introduce usual protections, and show their limits, both by discussing the most powerful attack or by showing evaluation methods.
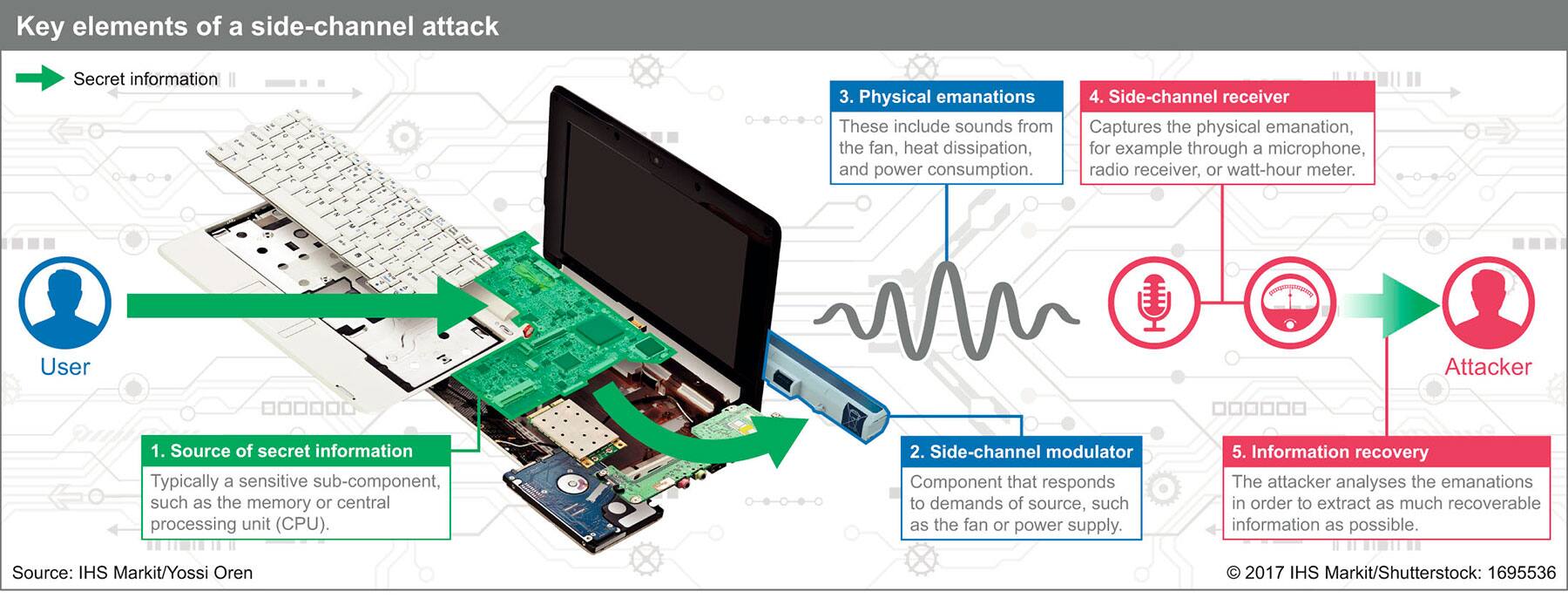
Side Channel Attacks Pose Growing Threat To Security Abstract side channel attacks are easy to implement whilst powerful attacks against cryptographic implementations, and their targets range from primitives, protocols, modules, and devices to even systems. these attacks pose a serious threat to the security of cryptographic modules. In this presentation, we o er a comprehensive overview of side channel analyses, and describe their power in ariousv real world scenarios. we introduce usual protections, and show their limits, both by discussing the most powerful attack or by showing evaluation methods. Spectre and meltdown carry out cache attacks against speculatively loaded data so that an unprivileged attacker process can read kernel memory, break aslr, etc. Abstract: latest side channel attacks are very easy to execute powerful attacks against crypto graphic implementations, and their targets range from primitives, protocols, modules, devices to even systems. these attacks harm a serious threat to the security of cryptographic modules. We show in this chapter the main modern concepts about side channel attacks (simple and differential power analysis) and how they can be deployed on fpga architecture. we give also a set of details on platform and equipment needed to conduct such type of experiments. Side channel attacks (scas) exploit physical implementation flaws in cryptographic devices, posing critical security threats. scas are categorized into passive and active, invasive, semi invasive, and non invasive types based on attack parameters.

Basic Thoughts And Terms On Side Channel Attacks On Ics Leuze Verlag Spectre and meltdown carry out cache attacks against speculatively loaded data so that an unprivileged attacker process can read kernel memory, break aslr, etc. Abstract: latest side channel attacks are very easy to execute powerful attacks against crypto graphic implementations, and their targets range from primitives, protocols, modules, devices to even systems. these attacks harm a serious threat to the security of cryptographic modules. We show in this chapter the main modern concepts about side channel attacks (simple and differential power analysis) and how they can be deployed on fpga architecture. we give also a set of details on platform and equipment needed to conduct such type of experiments. Side channel attacks (scas) exploit physical implementation flaws in cryptographic devices, posing critical security threats. scas are categorized into passive and active, invasive, semi invasive, and non invasive types based on attack parameters.
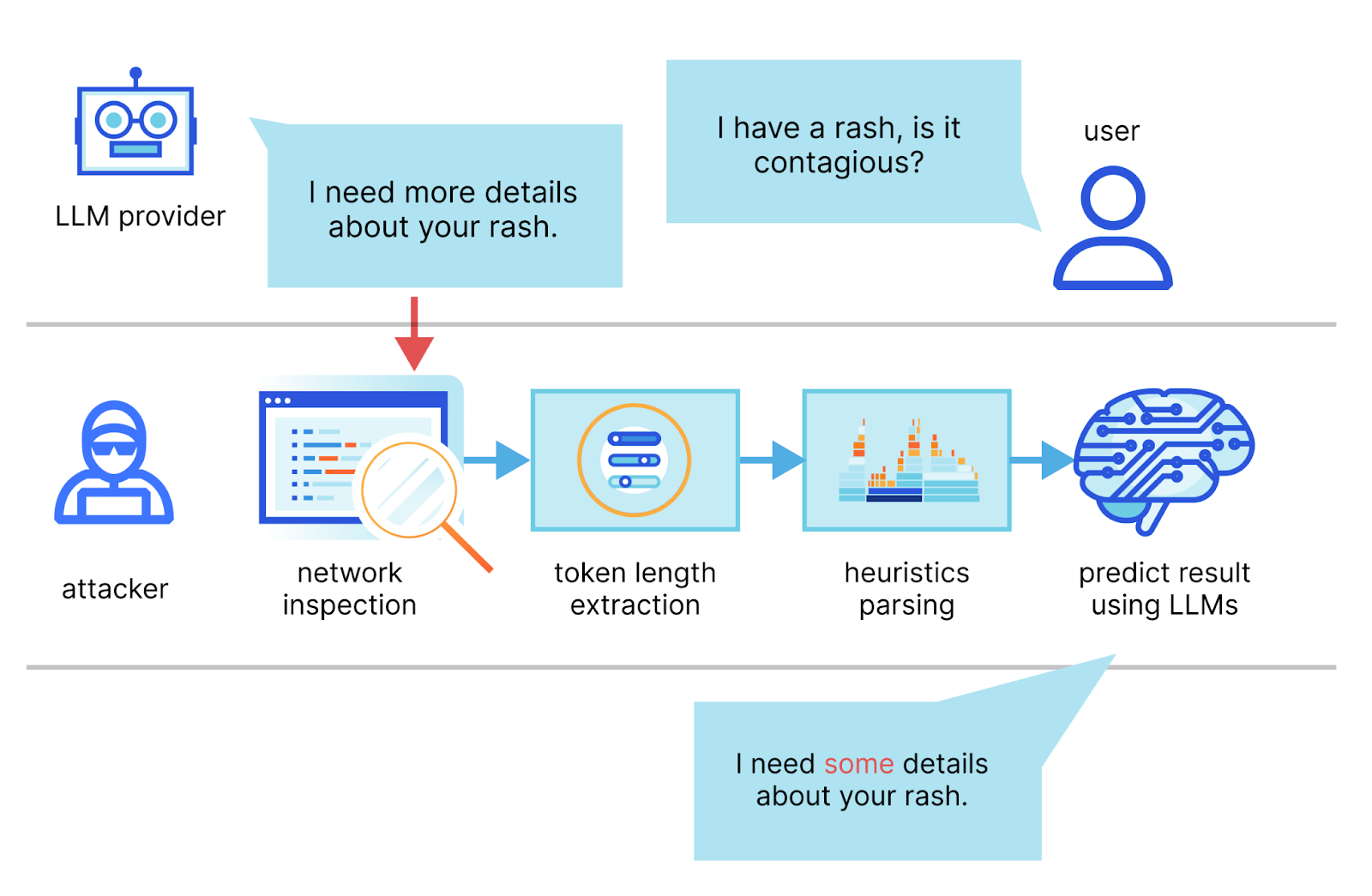
Mitigating A Token Length Side Channel Attack In Our Ai Products We show in this chapter the main modern concepts about side channel attacks (simple and differential power analysis) and how they can be deployed on fpga architecture. we give also a set of details on platform and equipment needed to conduct such type of experiments. Side channel attacks (scas) exploit physical implementation flaws in cryptographic devices, posing critical security threats. scas are categorized into passive and active, invasive, semi invasive, and non invasive types based on attack parameters.

A Quantitative Analysis Of Non Profiled Side Channel Attacks Based On
Comments are closed.