Social Engineering Attacks Understanding And Mitigating Hum

Methods For Understanding And Reducing Social Engineering Attacks The research examines prevalent social engineering assault forms that combine phishing with pretexting and baiting together with ai powered deepfake scams because of their damaging effect on organizational security operations. Social engineering attacks represent a significant threat, leveraging human vulnerability over technological weaknesses. mitigating these attacks requires a proactive approach combining.

Social Engineering Attacks Understanding And Mitigating Hum Social engineering attacks are a significant threat that exploit human vulnerabilities. by understanding the tactics used and recognizing the signs, we can better protect ourselves and our organizations. Social engineering remains one of the most dangerous cybersecurity threats because it targets people—not systems. this guide breaks down how social engineering works, the most common attack types, and proven strategies to prevent and mitigate these human driven cyber risks. This paper carefully assesses reverse social engineering (rse) and its impact on social engineering attacks, including their categorizations, methods of detection, and strategies for mitigating them. Social engineering, a manipulation technique that exploits human psychology, has emerged as one of the most significant threats to information security. this article aims to provide a.

Understanding And Mitigating Social Engineering Attacks In Ireland This paper carefully assesses reverse social engineering (rse) and its impact on social engineering attacks, including their categorizations, methods of detection, and strategies for mitigating them. Social engineering, a manipulation technique that exploits human psychology, has emerged as one of the most significant threats to information security. this article aims to provide a. Discover the psychological tactics behind social engineering attacks and learn to recognize manipulation before becoming a victim. expert insights included. While prevention is all but impossible, more research and better methods of understanding how and why an organization's representatives are easy targets would go a long way to reduce the success of these penetration efforts. Social engineering attacks manipulate individuals into divulging confidential information or performing actions that compromise security. understanding the threats, vulnerabilities, and mitigations associated with social engineering is essential for building a resilient security posture. In this research paper, the author explores the mechanics, tactics, and psychology behind social engineering, which leads to the fact that human beings are the weakest link in the cybersecurity chain.

Understanding And Mitigating Social Engineering In Cybersecurity Discover the psychological tactics behind social engineering attacks and learn to recognize manipulation before becoming a victim. expert insights included. While prevention is all but impossible, more research and better methods of understanding how and why an organization's representatives are easy targets would go a long way to reduce the success of these penetration efforts. Social engineering attacks manipulate individuals into divulging confidential information or performing actions that compromise security. understanding the threats, vulnerabilities, and mitigations associated with social engineering is essential for building a resilient security posture. In this research paper, the author explores the mechanics, tactics, and psychology behind social engineering, which leads to the fact that human beings are the weakest link in the cybersecurity chain.
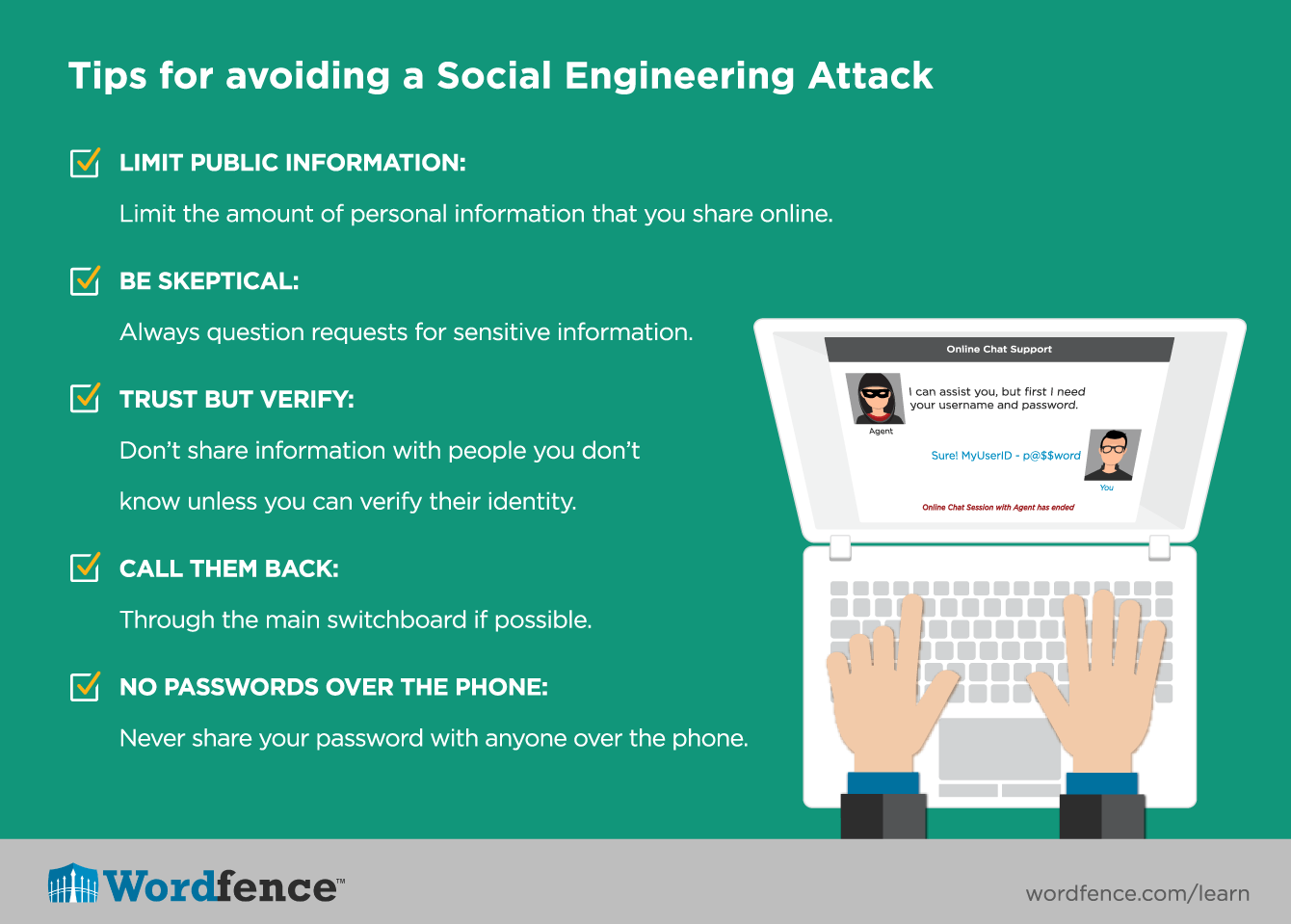
Understanding Social Engineering Techniques Social engineering attacks manipulate individuals into divulging confidential information or performing actions that compromise security. understanding the threats, vulnerabilities, and mitigations associated with social engineering is essential for building a resilient security posture. In this research paper, the author explores the mechanics, tactics, and psychology behind social engineering, which leads to the fact that human beings are the weakest link in the cybersecurity chain.
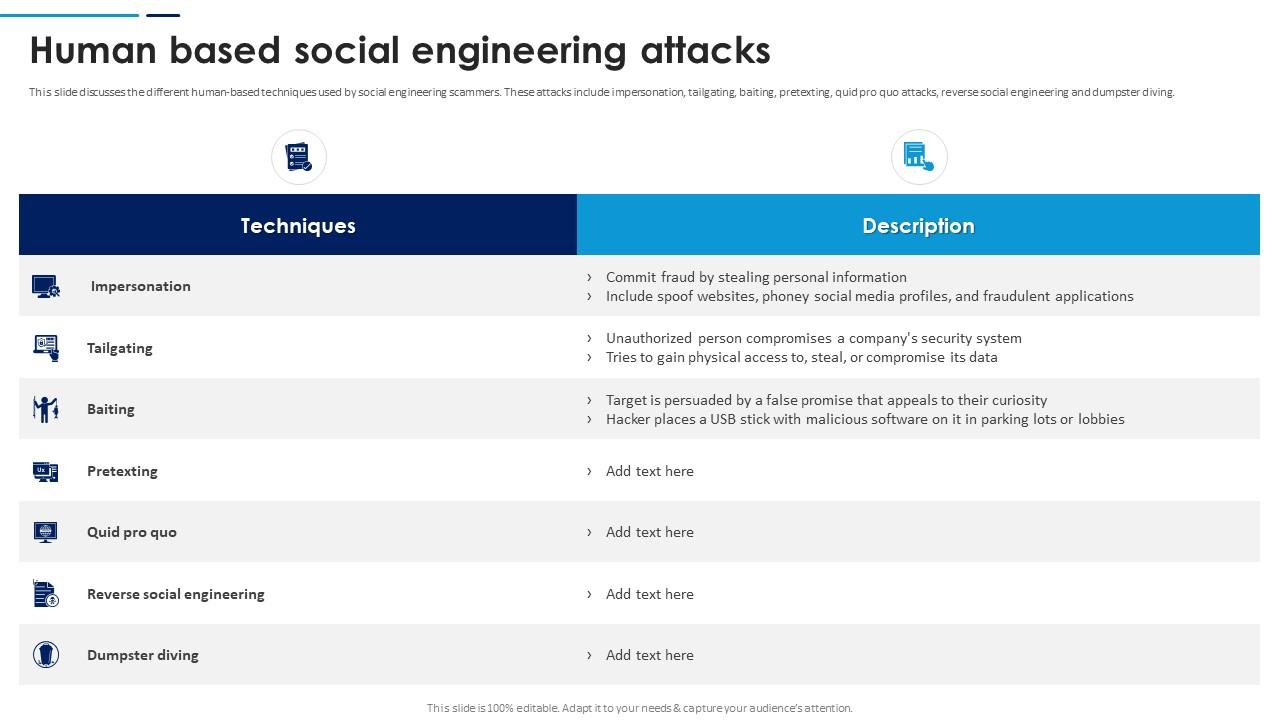
Social Engineering Attacks Prevention Human Based Social Engineering
Comments are closed.