Understanding Social Engineering Techniques

Understanding Social Engineering Techniques Pliable It Services Phishing is one specific technique within social engineering that uses electronic communication (typically email) to deceive victims. other social engineering techniques include pretexting, baiting, physical impersonation, and phone based attacks (vishing). What is social engineering? social engineering is the art of exploiting human psychology, rather than technical hacking techniques, to gain access to buildings, systems, or data.

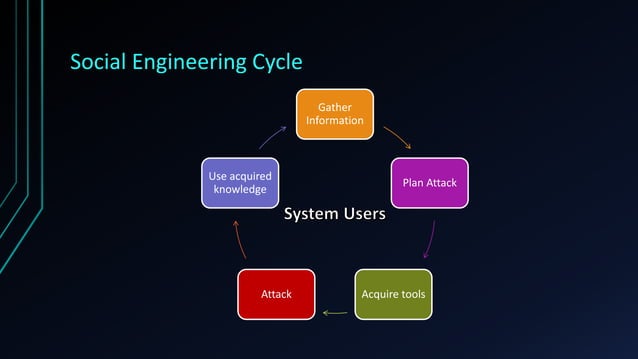
Social Engineering Techniques Understanding Performing And Defending This introductory article in our “dangers of social engineering” series offers a high level overview of what social engineering is and how it is used – equipping you with the knowledge you need to avoid becoming its next victim. Social engineering is a type of cyber attack where hackers trick people into sharing sensitive information like passwords, bank details, or personal data. instead of breaking into systems, attackers manipulate human emotions such as trust, fear, or curiosity to gain access. Learn the four phases of social engineering attacks and how understanding them helps organizations defend against human based cyber threats. Learn about the latest types of social engineering threats and best practices to defend against them. this is part of a series of articles about cyber security threats.
Introduction To Social Engineering Techniques Of Social Engineering Ppt Learn the four phases of social engineering attacks and how understanding them helps organizations defend against human based cyber threats. Learn about the latest types of social engineering threats and best practices to defend against them. this is part of a series of articles about cyber security threats. Here are the most common types of social engineering attacks currently in use with real world examples. Get the ultimate guide to social engineering attacks—learn tactics, psychology, real examples, and prevention to secure your organization. Understand social engineering attacks and learn how to prevent and mitigate risks using training, email security, mfa, verification protocols, and response strategies. Discover what social engineering means in cybersecurity, how attacks are executed, common types, real world examples, and best practices to protect against human targeted cyber threats.
Introduction To Social Engineering Techniques Of Social Engineering Ppt Here are the most common types of social engineering attacks currently in use with real world examples. Get the ultimate guide to social engineering attacks—learn tactics, psychology, real examples, and prevention to secure your organization. Understand social engineering attacks and learn how to prevent and mitigate risks using training, email security, mfa, verification protocols, and response strategies. Discover what social engineering means in cybersecurity, how attacks are executed, common types, real world examples, and best practices to protect against human targeted cyber threats.
Introduction To Social Engineering Techniques Of Social Engineering Ppt Understand social engineering attacks and learn how to prevent and mitigate risks using training, email security, mfa, verification protocols, and response strategies. Discover what social engineering means in cybersecurity, how attacks are executed, common types, real world examples, and best practices to protect against human targeted cyber threats.

Understanding Social Engineering Techniques And Why They Are So
Comments are closed.