Social Engineering Attacks Prevention Technology Based Social
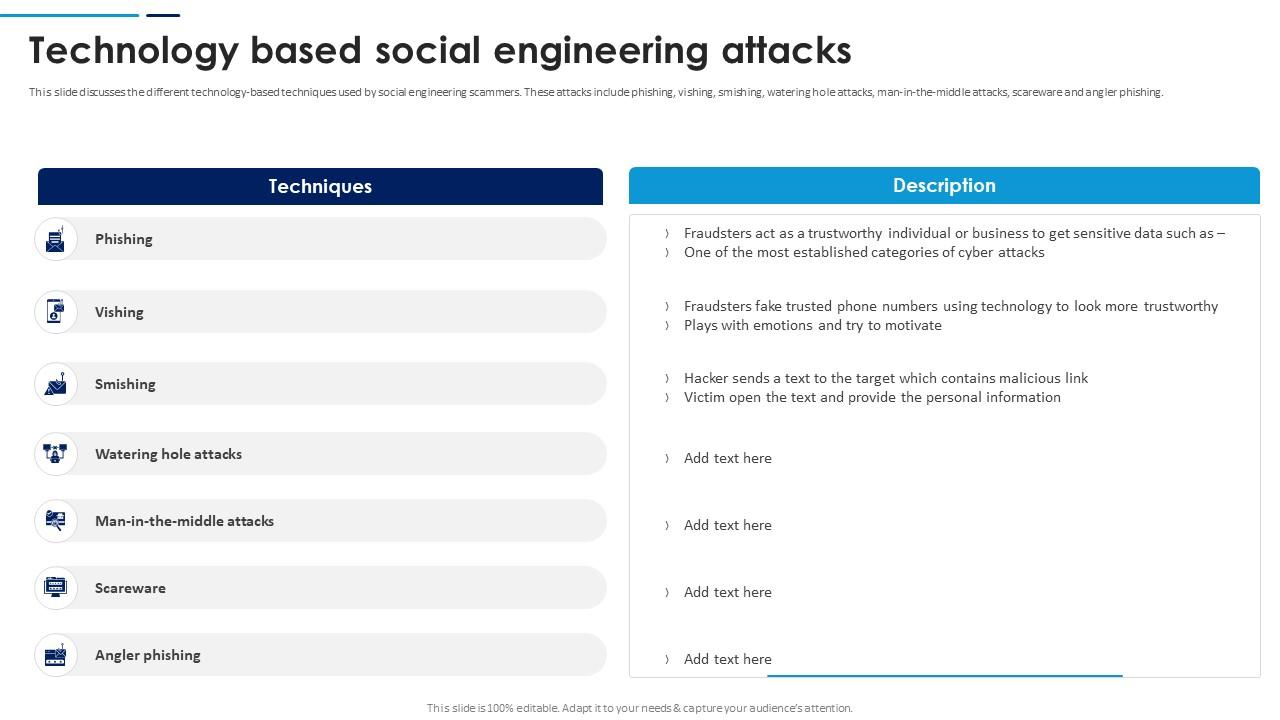
Social Engineering Attacks Prevention Technology Based Social This guide breaks down how social engineering works, the most common attack types, and proven strategies to prevent and mitigate these human driven cyber risks. The proposed survey starts by discovering the rq that motivates the authors to examine different aspects of social engineering attacks, preventive measures, and acknowledging technologies, such as ai and blockchain, in tackling social engineering attacks.
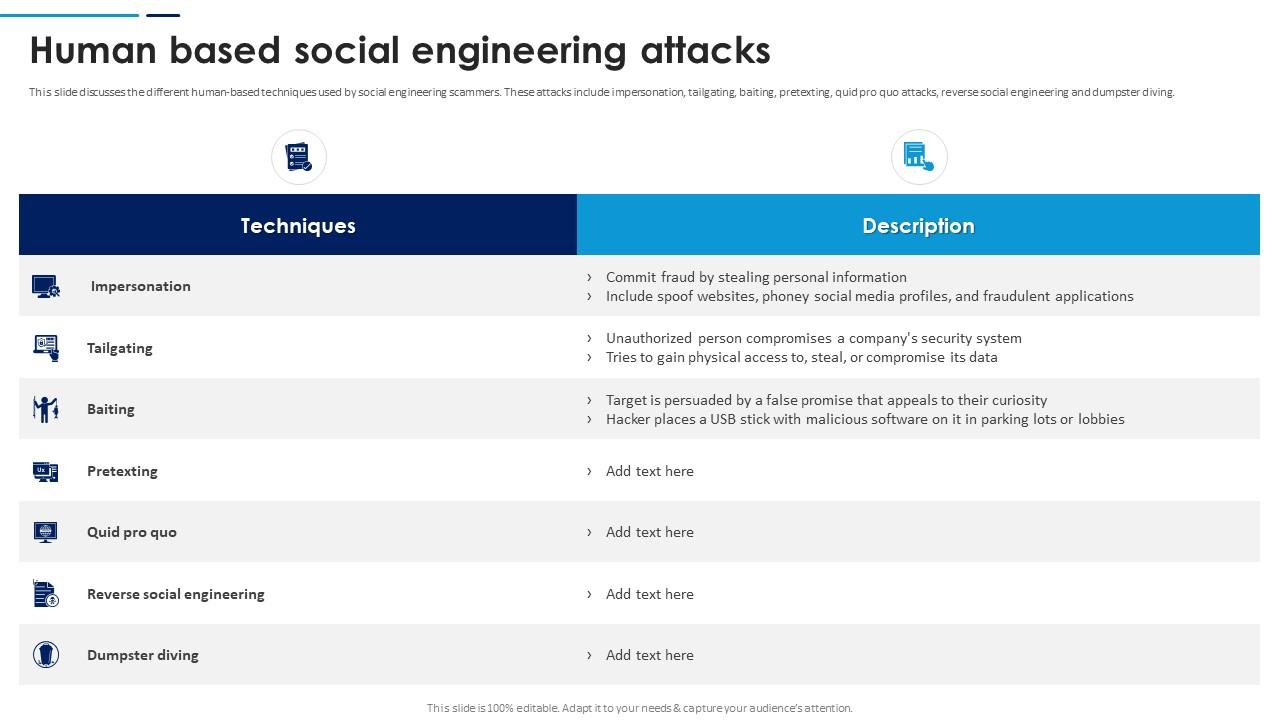
Social Engineering Attacks Prevention Human Based Social Engineering Learning how to prevent social engineering attacks reduces the chances of data breaches. read up on best practices for organizations and employees. Preventing social engineering attacks requires a multi layered approach that combines technological solutions, user education, and organizational policies. these strategies aim to minimize the human and technical vulnerabilities that attackers exploit. This paper provides a comprehensive exploration of social engineering attacks, encompassing their phases, types, and associated tools for simulation and defense across windows and linux. We’ll look specifically at how emerging technologies, such as deepfakes, have amplified social engineering techniques and increased the potential for fraud. we’ll also explore mitigation strategies and tools available for organizations to fight this battle effectively.

Social Engineering Prevention Tips How To Outsmart Human Based Cyber This paper provides a comprehensive exploration of social engineering attacks, encompassing their phases, types, and associated tools for simulation and defense across windows and linux. We’ll look specifically at how emerging technologies, such as deepfakes, have amplified social engineering techniques and increased the potential for fraud. we’ll also explore mitigation strategies and tools available for organizations to fight this battle effectively. Social engineering attacks occur when victims do not recognize methods, models, and frameworks to prevent them. the current research explains user studies, constructs, evaluation, concepts, frameworks, models, and methods to prevent social engineering attacks. The study introduces a taxonomy of social engineering attacks, categorizing them based on the operator, prevention measures, and mitigation techniques. this thorough analysis underscores the current challenges in the domain and suggests potential future trajectories in the field. Learn how to prevent social engineering attacks with effective strategies to protect your organization from these deceptive and harmful threats. Social engineering attacks leverage human interaction and emotions to manipulate the target. learn what social engineering is, its techniques, examples and how to protect against it.
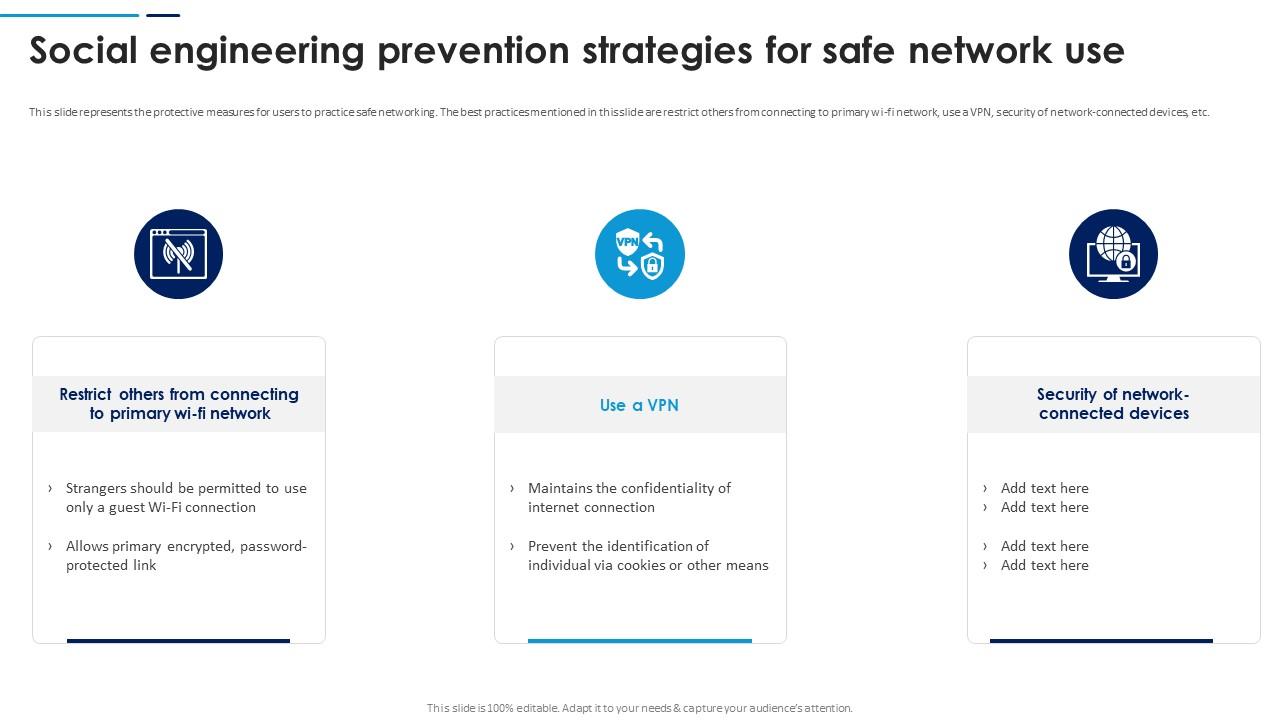
Social Engineering Attacks Prevention Social Engineering Prevention Social engineering attacks occur when victims do not recognize methods, models, and frameworks to prevent them. the current research explains user studies, constructs, evaluation, concepts, frameworks, models, and methods to prevent social engineering attacks. The study introduces a taxonomy of social engineering attacks, categorizing them based on the operator, prevention measures, and mitigation techniques. this thorough analysis underscores the current challenges in the domain and suggests potential future trajectories in the field. Learn how to prevent social engineering attacks with effective strategies to protect your organization from these deceptive and harmful threats. Social engineering attacks leverage human interaction and emotions to manipulate the target. learn what social engineering is, its techniques, examples and how to protect against it.
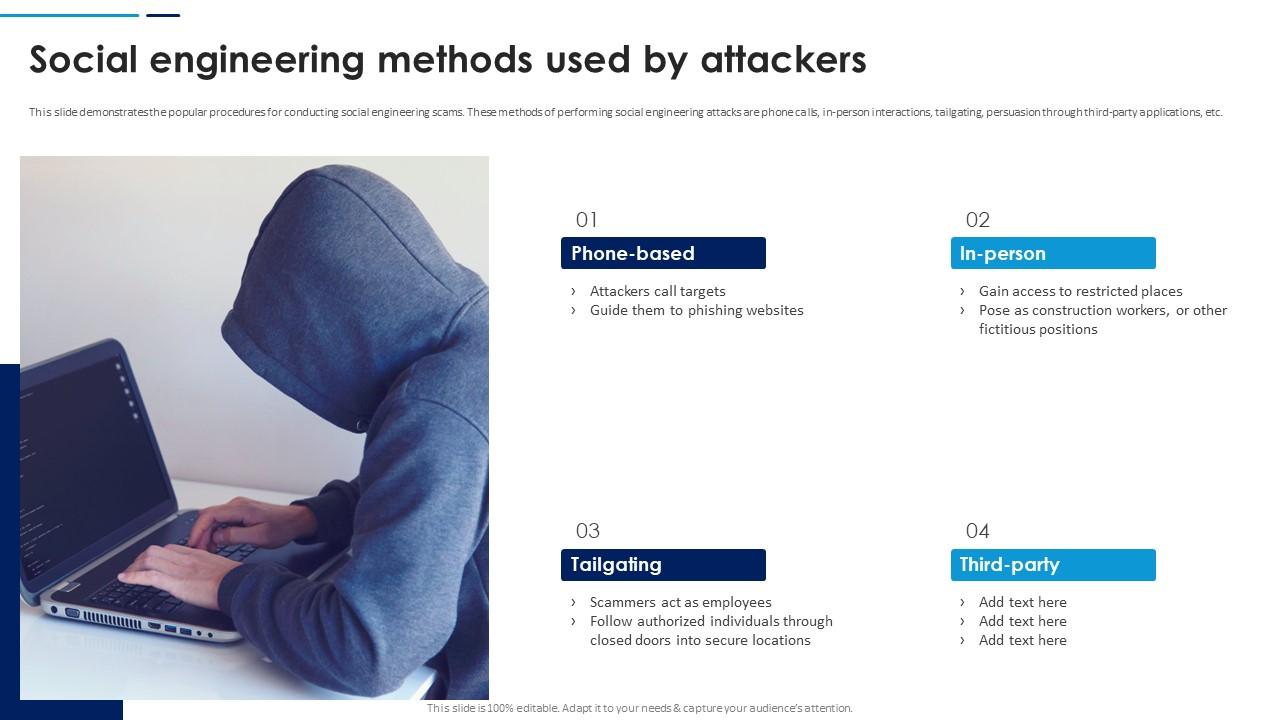
Social Engineering Attacks Prevention Social Engineering Methods Used Learn how to prevent social engineering attacks with effective strategies to protect your organization from these deceptive and harmful threats. Social engineering attacks leverage human interaction and emotions to manipulate the target. learn what social engineering is, its techniques, examples and how to protect against it.
Comments are closed.