Social Engineering Cyber Attacks And Prevention Mechanism Pdf

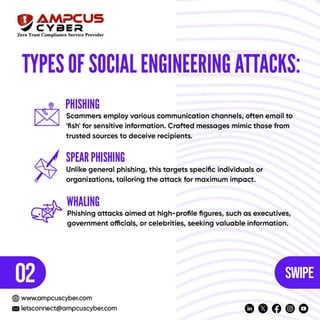
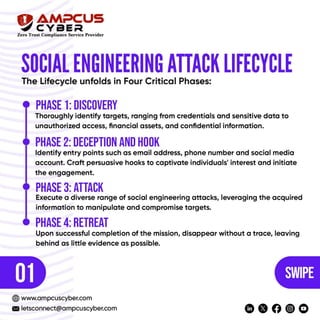
Introduction To Social Engineering Attacks Pdf This study explores the different forms of social engineering attacks, analyzes real world cases, and investigates the strategies attackers employ. Detection. through a combination of case studies, theoretical frameworks, and practical recommendations, this paper explores the potential of precision framing to revolutionize social engineering tactics and mitigate the cyber threats facing organizations and individuals alike.
Social Engineering Cyber Attacks And Prevention Mechanism Pdf This paper intends to critically and rigorously review prior literature on the prevention methods, models, and frameworks of social engineering attacks. we conducted a systematic literature review based on bryman & bell’s literature review method. Social engineering attacks pose a persistent and growing threat in the cybersecurity landscape, exploiting human psychology and trust to bypass technological defenses. Social engineers prey on the psy chological weaknesses of humans with sophisticated attacks, which pose serious cybersecurity threats to digital infrastructure. This paper intends to critically and rigorously review prior literature on the prevention methods, models, and frameworks of social engineering attacks. we conducted a systematic literature review based on bryman & bell's literature review method.

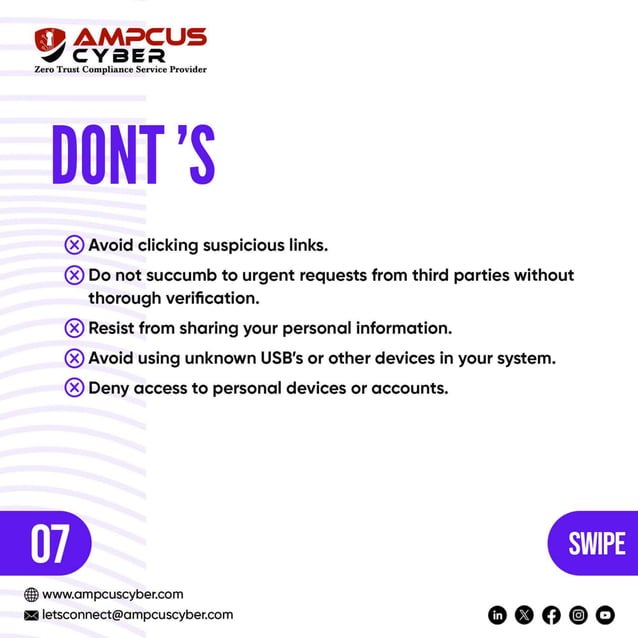
Social Engineering Cyber Attacks And Prevention Mechanism Pdf Social engineers prey on the psy chological weaknesses of humans with sophisticated attacks, which pose serious cybersecurity threats to digital infrastructure. This paper intends to critically and rigorously review prior literature on the prevention methods, models, and frameworks of social engineering attacks. we conducted a systematic literature review based on bryman & bell's literature review method. The modern cyber security system has been built better but people continue to be the fundamental vulnerability. this research investigates social engineering attacks and the pivotal role of human centric defense mechanisms in corporate networks. In this guide, we’ll explore how social engineering attacks work, the techniques most commonly used by attackers, and the practical steps you and your team can take to stay protected against these fast evolving threats. A comprehensive analysis of social engineering attacks from phishing to prevention tools techniques and strategies free download as pdf file (.pdf), text file (.txt) or read online for free. Though humans are one of the weakest links in the cyber security domain, various social engineering techniques were discussed through which one can prevent themselves from falling prey to such traps.
Social Engineering Cyber Attacks And Prevention Mechanism Pdf The modern cyber security system has been built better but people continue to be the fundamental vulnerability. this research investigates social engineering attacks and the pivotal role of human centric defense mechanisms in corporate networks. In this guide, we’ll explore how social engineering attacks work, the techniques most commonly used by attackers, and the practical steps you and your team can take to stay protected against these fast evolving threats. A comprehensive analysis of social engineering attacks from phishing to prevention tools techniques and strategies free download as pdf file (.pdf), text file (.txt) or read online for free. Though humans are one of the weakest links in the cyber security domain, various social engineering techniques were discussed through which one can prevent themselves from falling prey to such traps.
Social Engineering Cyber Attacks And Prevention Mechanism Pdf A comprehensive analysis of social engineering attacks from phishing to prevention tools techniques and strategies free download as pdf file (.pdf), text file (.txt) or read online for free. Though humans are one of the weakest links in the cyber security domain, various social engineering techniques were discussed through which one can prevent themselves from falling prey to such traps.
Comments are closed.