Smishing Vs Phishing Whats The Difference
Smishing Vs Phishing 5 Examples Of Each Memcyco Discover the key differences between smishing vs phishing, learn to avoid scams, and protect your organization from cyber threats. Phishing, smishing and vishing are all methods of identity fraud that differ in how scammers contact you—by email, text or phone—to steal personal details or financial account information.
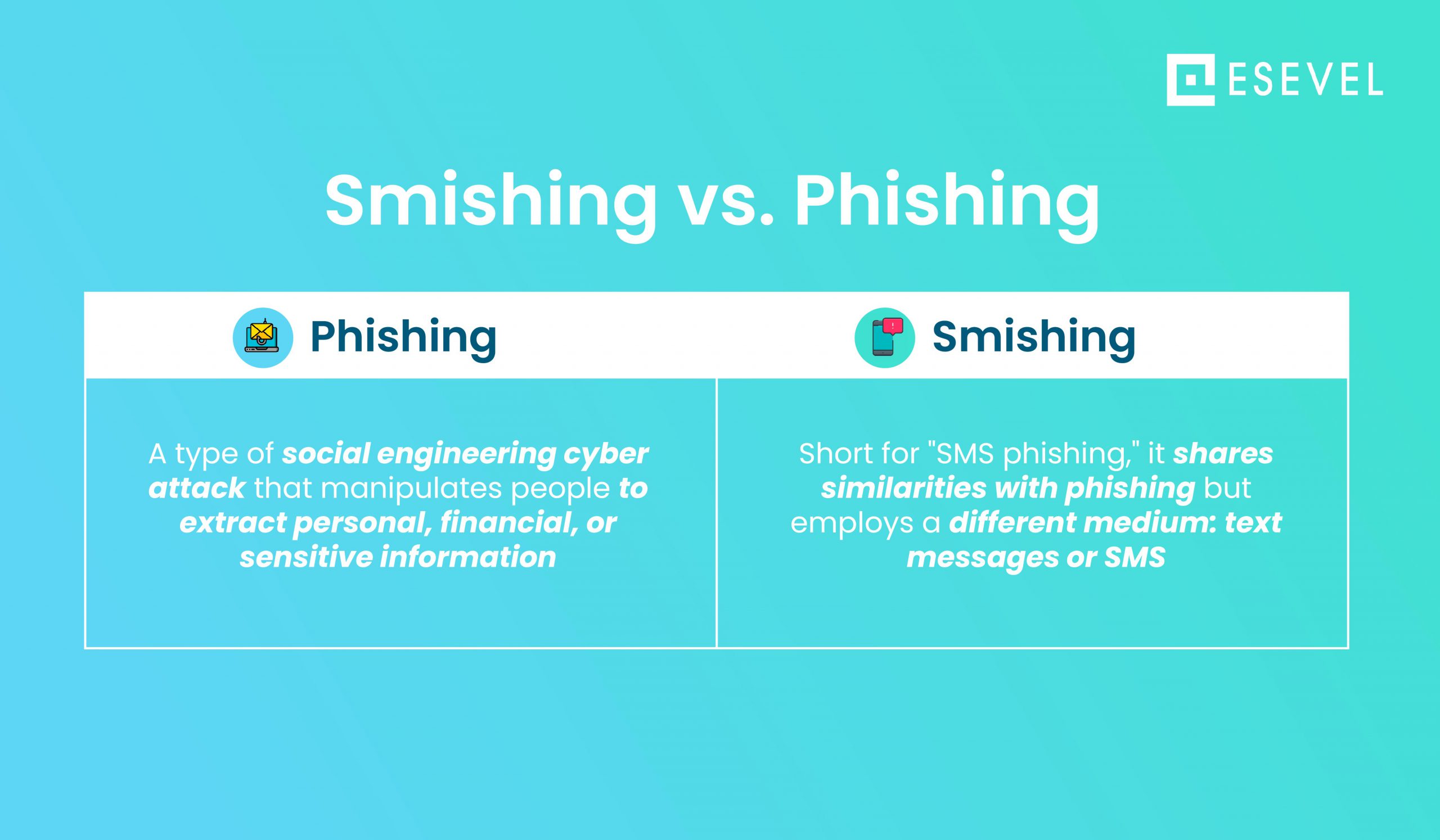
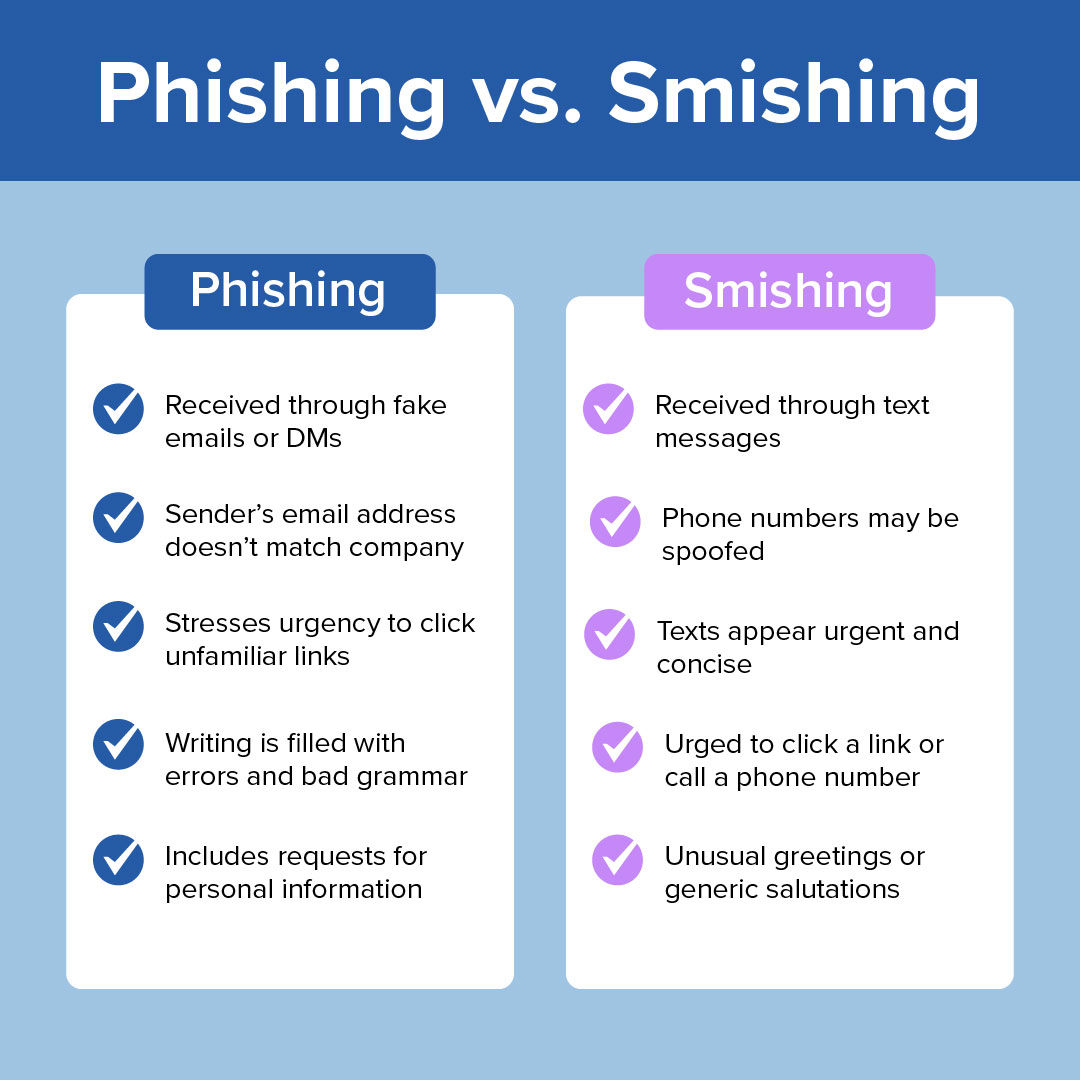
Smishing Vs Phishing Differences Between Two Cyber Threats Esevel While smishing and phishing attacks share these similarities, it’s important to remember that they utilize different attack vectors. smishing attacks use text messages and mobile devices, exploiting their ubiquity and immediacy. phishing attacks primarily occur through email or fraudulent websites. 5 ways to prevent smishing and phishing attacks. Understand the key differences between smishing and phishing. proofpoint explains how each attack vector operates and what makes them dangerous. Phishing, smishing, and vishing are similar types of social engineering threats. the key difference is that smishing attacks occur over text messages, whereas other phishing attacks use different mediums. Learn the differences between smishing and phishing, two cyber threats that are used to to steal sensitive information.
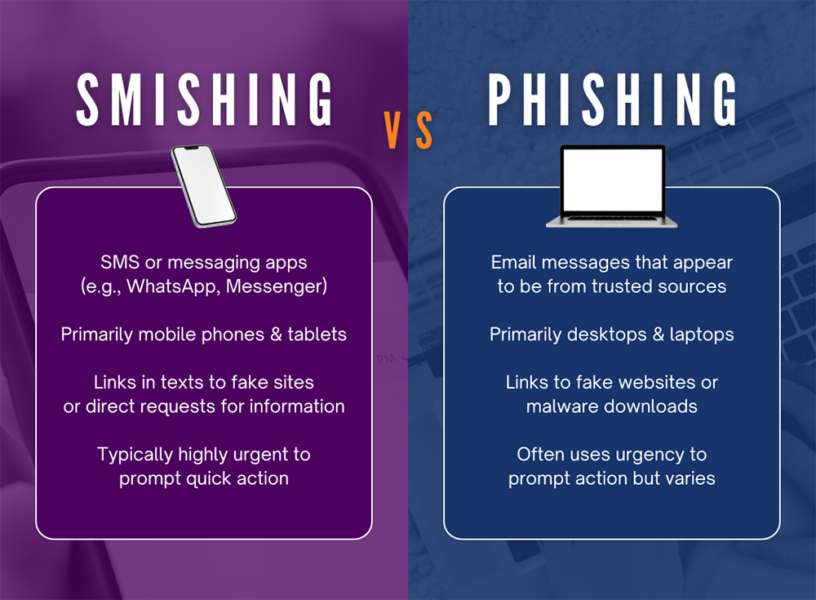
Smishing Vs Phishing What S The Difference Omega Systems Phishing, smishing, and vishing are similar types of social engineering threats. the key difference is that smishing attacks occur over text messages, whereas other phishing attacks use different mediums. Learn the differences between smishing and phishing, two cyber threats that are used to to steal sensitive information. Two common cybersecurity threats are smishing and phishing, but how are they different? and how can you protect yourself against both?. While phishing typically targets individuals through email, smishing uses text messages to deceive victims. understanding the differences between these tactics and employing specific defenses, such as avoiding suspicious links and using security software, is key to protecting your information. Despite their different delivery methods, smishing and phishing attacks have similar objectives and tactics. smishing and phishing attacks heavily rely on social engineering tactics to deceive victims and extract sensitive information. Comparison table: how do smishing and phishing attacks work? to grasp the distinctions between smishing scams and phishing attacks, let’s break down them down step by step.

What Is A Smishing Attack Akamai Two common cybersecurity threats are smishing and phishing, but how are they different? and how can you protect yourself against both?. While phishing typically targets individuals through email, smishing uses text messages to deceive victims. understanding the differences between these tactics and employing specific defenses, such as avoiding suspicious links and using security software, is key to protecting your information. Despite their different delivery methods, smishing and phishing attacks have similar objectives and tactics. smishing and phishing attacks heavily rely on social engineering tactics to deceive victims and extract sensitive information. Comparison table: how do smishing and phishing attacks work? to grasp the distinctions between smishing scams and phishing attacks, let’s break down them down step by step.
Comments are closed.