Smishing Vs Phishing Understanding The Differences Cloudmark En
Smishing Vs Phishing Understanding The Differences Cloudmark En In this blog post we’re going to look at smishing vs. phishing and what smishing offenders have learned from their email counterparts, as well as some significant differences that remain between the two threats. Discover the key differences between smishing vs phishing, learn to avoid scams, and protect your organization from cyber threats.

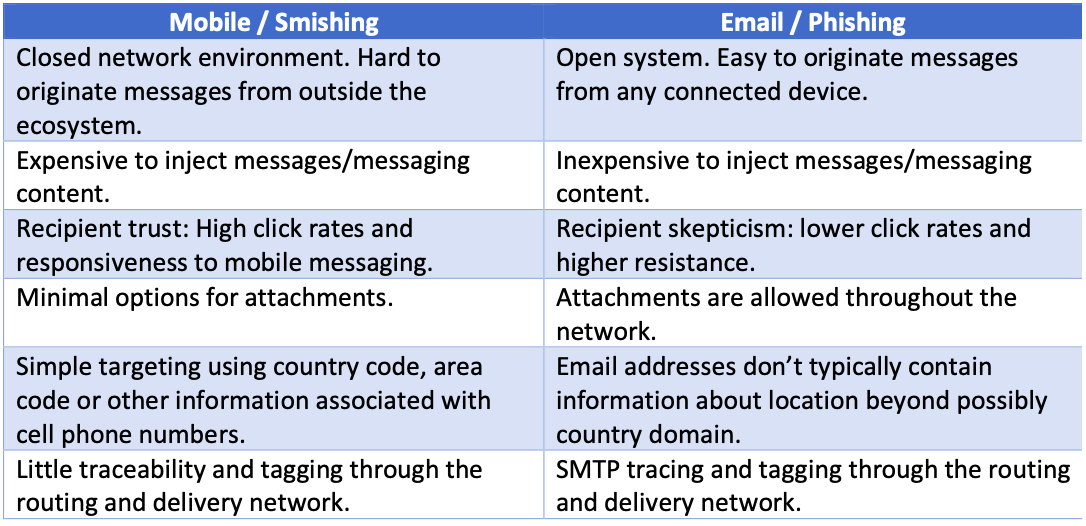
Smishing Vs Phishing Understanding The Differences Cloudmark En While smishing operations have to work with character limits, location constraints and increased overheads, it is clear that lessons learned from email phishing are helping to maximise their returns. Phishing uses deceptive emails, smishing employs fraudulent text messages, and vishing relies on misleading phone calls. understanding these key differences is crucial for recognising evolving scams. In this blog post we’re going to look at smishing vs. phishing and what smishing offenders have learned from their email counterparts, as well as some significant differences that remain between the two threats. Understand spoofing vs phishing, how attackers combine these tactics, and practical steps to protect your organization from advanced social engineering threats.

Smishing Vs Phishing Key Differences In Cyber Threats Sybaweb In this blog post we’re going to look at smishing vs. phishing and what smishing offenders have learned from their email counterparts, as well as some significant differences that remain between the two threats. Understand spoofing vs phishing, how attackers combine these tactics, and practical steps to protect your organization from advanced social engineering threats. Phishing, smishing and vishing are all methods of identity fraud that differ in how scammers contact you—by email, text or phone—to steal personal details or financial account information. Here's what businesses should know about how phishing and smashing work, how they're similar (and different), and what users can do to reduce the risk of getting caught. This in depth assessment of the smishing vs. phishing threat landscape spotlights key contrasts on attack vectors, effectiveness metrics, targeted data, and user vulnerabilities. While smishing and phishing attacks share these similarities, it’s important to remember that they utilize different attack vectors. smishing attacks use text messages and mobile devices, exploiting their ubiquity and immediacy. phishing attacks primarily occur through email or fraudulent websites. 5 ways to prevent smishing and phishing attacks.

Phishing Vs Smishing Vs Whaling Common Cyber Attacks Aeko Technologies Phishing, smishing and vishing are all methods of identity fraud that differ in how scammers contact you—by email, text or phone—to steal personal details or financial account information. Here's what businesses should know about how phishing and smashing work, how they're similar (and different), and what users can do to reduce the risk of getting caught. This in depth assessment of the smishing vs. phishing threat landscape spotlights key contrasts on attack vectors, effectiveness metrics, targeted data, and user vulnerabilities. While smishing and phishing attacks share these similarities, it’s important to remember that they utilize different attack vectors. smishing attacks use text messages and mobile devices, exploiting their ubiquity and immediacy. phishing attacks primarily occur through email or fraudulent websites. 5 ways to prevent smishing and phishing attacks.
Comments are closed.