Side Channel Attacks The Cyber Security Attack You Ve Probably Never

What Is A Side Channel Attack How Hackers Crack Security Without In computer security, a side channel attack is a type of security exploit that uses information inadvertently leaked by a system—such as timing, power consumption, or electromagnetic or acoustic emissions—to gain unauthorized access to sensitive information. Learn what a side channel attack is, how it works and how bad actors can implement different types of attacks. examine how to prevent side channel attacks.

Side Channel Attacks The Cyber Security Attack You Ve Probably Never Uncover the hidden world of side channel attacks: learn how hackers exploit system vulnerabilities, real world examples, and cutting edge defense strategies. In the realm of cybersecurity, most defenses focus on protecting algorithms, encryptions, and access controls. but what if an attacker doesn't break the algorithm—but listens to the whispers. Side channel attacks don't target cryptographic systems, but their implementations instead. find out how they can compromise secure algorithms. you can have the best cryptographic systems in the world in place, but your setup may still be vulnerable to side channel attacks. A side channel attack is defined as a method of stealing information indirectly by exploiting unintended information leakage, such as side channel signals generated during computation.
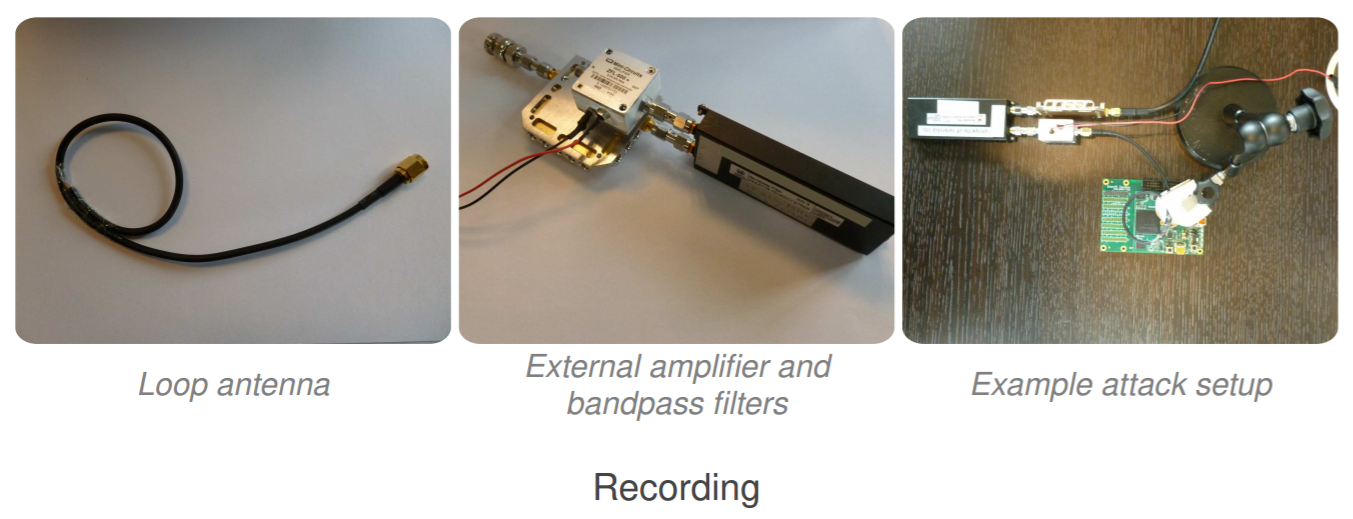
Side Channel Attack Archives Security Affairs Side channel attacks don't target cryptographic systems, but their implementations instead. find out how they can compromise secure algorithms. you can have the best cryptographic systems in the world in place, but your setup may still be vulnerable to side channel attacks. A side channel attack is defined as a method of stealing information indirectly by exploiting unintended information leakage, such as side channel signals generated during computation. But what if an attacker could steal sensitive information without ever breaking into your system? this is precisely what side channel attacks (scas) do—they exploit unintended information leaks from a device’s physical operations rather than breaking through traditional software vulnerabilities. Explore how side channel attacks secretly exploit hardware signals to steal data and key cybersecurity defenses explained. In this blog post, we'll define what side channel attacks are, explore their various types, discuss defense strategies, and offer an outlook on their evolving role in cybersecurity. That is the unsettling premise of side channel attacks. they don’t break cryptography in the usual sense. instead, they sidestep it, extracting secrets from the physical traces of.

What Is A Side Channel Attack In Cybersecurity Bestcybersecuritynews But what if an attacker could steal sensitive information without ever breaking into your system? this is precisely what side channel attacks (scas) do—they exploit unintended information leaks from a device’s physical operations rather than breaking through traditional software vulnerabilities. Explore how side channel attacks secretly exploit hardware signals to steal data and key cybersecurity defenses explained. In this blog post, we'll define what side channel attacks are, explore their various types, discuss defense strategies, and offer an outlook on their evolving role in cybersecurity. That is the unsettling premise of side channel attacks. they don’t break cryptography in the usual sense. instead, they sidestep it, extracting secrets from the physical traces of.
What Are Side Channel Attacks In Cybersecurity Bestcybersecuritynews In this blog post, we'll define what side channel attacks are, explore their various types, discuss defense strategies, and offer an outlook on their evolving role in cybersecurity. That is the unsettling premise of side channel attacks. they don’t break cryptography in the usual sense. instead, they sidestep it, extracting secrets from the physical traces of.
Comments are closed.