Side Channel Attacks Exploiting The Unseen In Cybersecurity

Side Channel Attacks Exploiting The Unseen In Cybersecurity Uncover the hidden world of side channel attacks: learn how hackers exploit system vulnerabilities, real world examples, and cutting edge defense strategies. Welcome to the world of side channel attacks (scas)—a class of exploits that harvest data not by attacking the logic of a program but by observing physical implementation leaks.

What Is A Side Channel Attack How Hackers Crack Security Without In computer security, a side channel attack is a type of security exploit that uses information inadvertently leaked by a system—such as timing, power consumption, or electromagnetic or acoustic emissions—to gain unauthorized access to sensitive information. Learn what a side channel attack is, how it works and how bad actors can implement different types of attacks. examine how to prevent side channel attacks. Side channel attacks present a sophisticated and often overlooked threat in the field of cybersecurity. unlike conventional cyberattacks that exploit software vulnerabilities or network misconfigurations, side channel attacks exploit indirect data leaks from the physical operation of a system. Side channel attacks (scas) exploit indirect information leaked by a system during its execution, such as power consumption, electromagnetic emissions, or timing variations. these attacks.

Understanding Side Channel Attacks Power Timing Analysis Cyber Snowden Side channel attacks present a sophisticated and often overlooked threat in the field of cybersecurity. unlike conventional cyberattacks that exploit software vulnerabilities or network misconfigurations, side channel attacks exploit indirect data leaks from the physical operation of a system. Side channel attacks (scas) exploit indirect information leaked by a system during its execution, such as power consumption, electromagnetic emissions, or timing variations. these attacks. A side channel attack is defined as a method of stealing information indirectly by exploiting unintended information leakage, such as side channel signals generated during computation. Explore how side channel attacks secretly exploit hardware signals to steal data and key cybersecurity defenses explained. In computer security, a side channel attack is any attack that exploits additional information available due to the implementation of cryptographic algorithms. this information is considered an unintentional “leakage” due to the physical behavior of digital circuits. Side channel attacks represent a unique and highly potent class of cyberattacks that exploit the unintended physical emissions of a system during normal operation.

Side Channel Attacks Explained All You Need To Know Rambus A side channel attack is defined as a method of stealing information indirectly by exploiting unintended information leakage, such as side channel signals generated during computation. Explore how side channel attacks secretly exploit hardware signals to steal data and key cybersecurity defenses explained. In computer security, a side channel attack is any attack that exploits additional information available due to the implementation of cryptographic algorithms. this information is considered an unintentional “leakage” due to the physical behavior of digital circuits. Side channel attacks represent a unique and highly potent class of cyberattacks that exploit the unintended physical emissions of a system during normal operation.
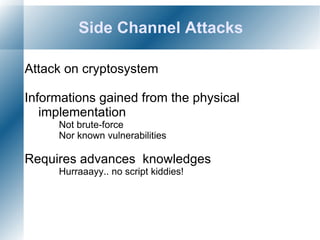
Side Channel Attacks Odp In computer security, a side channel attack is any attack that exploits additional information available due to the implementation of cryptographic algorithms. this information is considered an unintentional “leakage” due to the physical behavior of digital circuits. Side channel attacks represent a unique and highly potent class of cyberattacks that exploit the unintended physical emissions of a system during normal operation.
Comments are closed.