Shellcode Loader Poc
Github Kanbaraakihito Shellcode Loader 各种加载器 It's able to fully bypass many edr injection detections, including defender atp. bypasses simple thread centric scanners like get injectedthread. persisting within a process is another story, and this is up to the payload author. First things first — we’ll need a shellcode loader for the pocs. as i mentioned before, we need a program that will load the shellcode into memory and hand control over to windbg so we can run the poc manually.
Github Avienma Shellcode Loader 一款shellcode免杀工具 免杀测试对象火绒 联想等其他杀软 Today we’re going to understand how some (simple) malware development techniques work and how they can help us in red team operations, where the idea is to create a loader in c that executes a. This post is heavily similar to my previous post located here around designing a custom shellcode loader which will pull shellcode from a server and execute it into a process. This guide aims to provide a step by step tutorial on creating a minimal shellcode loader using the c programming language. by understanding the concepts presented here, you'll gain insights into low level system interactions and enhance your skills in offensive and defensive security practices. This content is intended to help you deepen your understanding of (in)direct syscalls, improve your indirect syscall shellcode loader, and implement the hell's gate and halos gate techniques step by step.

Github Avienma Shellcode Loader 一款shellcode免杀工具 免杀测试对象火绒 联想等其他杀软 This guide aims to provide a step by step tutorial on creating a minimal shellcode loader using the c programming language. by understanding the concepts presented here, you'll gain insights into low level system interactions and enhance your skills in offensive and defensive security practices. This content is intended to help you deepen your understanding of (in)direct syscalls, improve your indirect syscall shellcode loader, and implement the hell's gate and halos gate techniques step by step. The shellcode loader driploader (poc) has provided valuable insights into how attackers can bypass the very tools we rely on. i hope you find this blog both informative and a meaningful addition to your growing knowledge toolkit. Every single step of the classic “write to disk → execute” workflow is monitored. a loader is the bridge between your raw capability (shellcode, dll, assembly) and execution in the target environment. Explore a proof of concept demonstration of a shellcode loader in this informative video. Threadstackspoofer is a poc implementation for an advanced in memory evasion technique that spoofs thread call stack. this technique allows to bypass thread based memory examination rules and better hide shellcodes while in process memory.
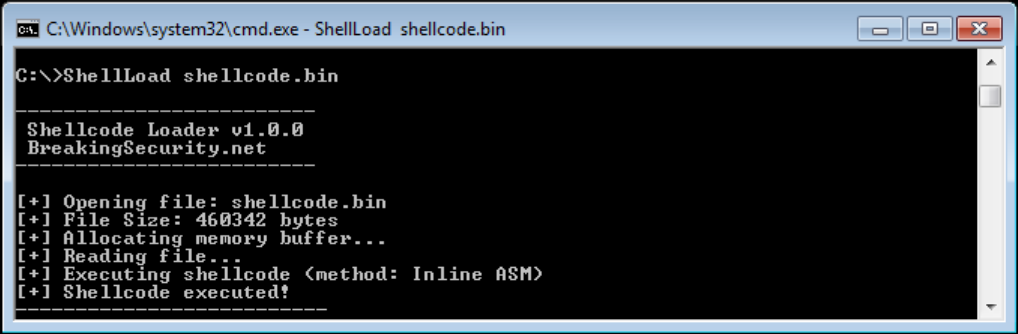
Shellcode Loader Breakingsecurity Net The shellcode loader driploader (poc) has provided valuable insights into how attackers can bypass the very tools we rely on. i hope you find this blog both informative and a meaningful addition to your growing knowledge toolkit. Every single step of the classic “write to disk → execute” workflow is monitored. a loader is the bridge between your raw capability (shellcode, dll, assembly) and execution in the target environment. Explore a proof of concept demonstration of a shellcode loader in this informative video. Threadstackspoofer is a poc implementation for an advanced in memory evasion technique that spoofs thread call stack. this technique allows to bypass thread based memory examination rules and better hide shellcodes while in process memory.

Github Secnn Shellcode Loader Shellcode Loader Msf Cobaltstrike免杀 Explore a proof of concept demonstration of a shellcode loader in this informative video. Threadstackspoofer is a poc implementation for an advanced in memory evasion technique that spoofs thread call stack. this technique allows to bypass thread based memory examination rules and better hide shellcodes while in process memory.
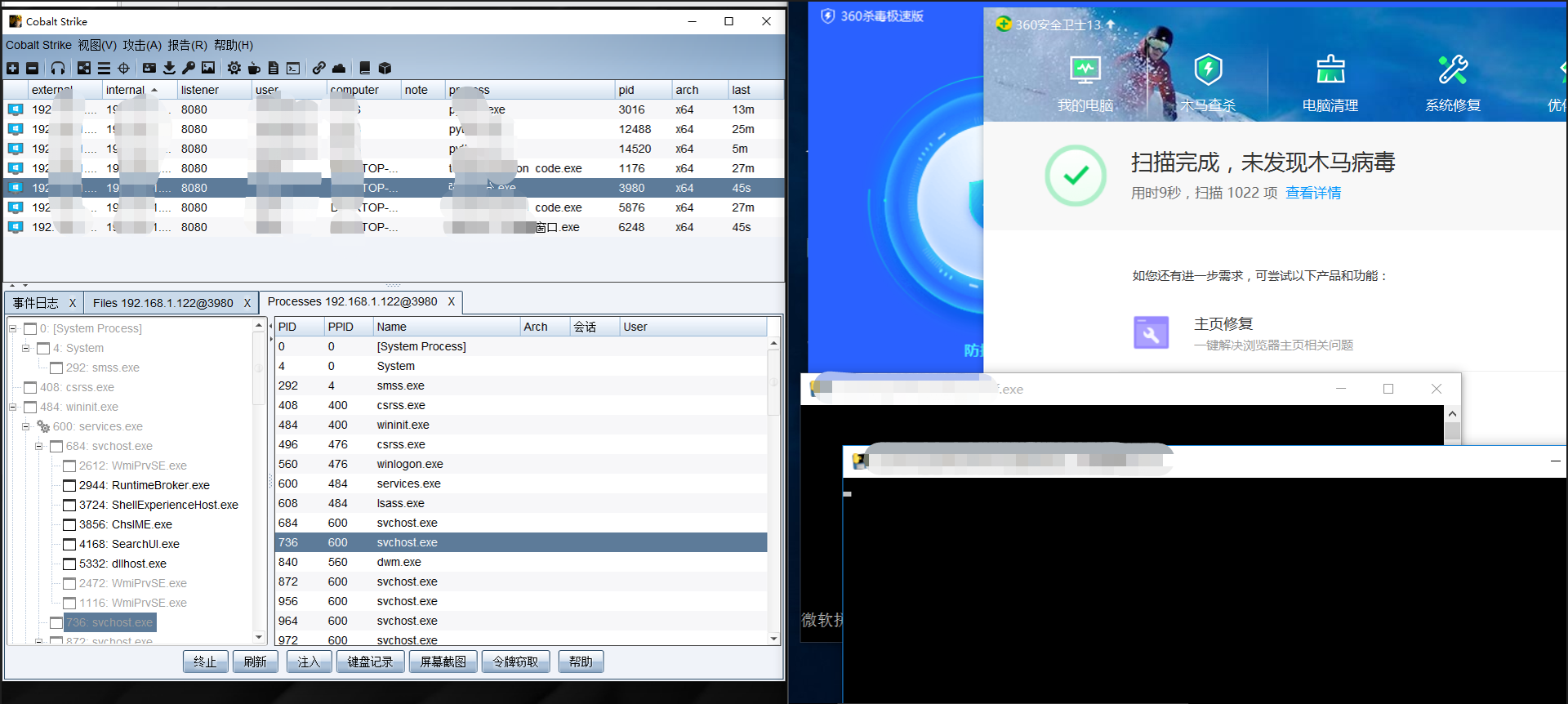
Github Secnn Shellcode Loader Shellcode Loader Msf Cobaltstrike免杀
Comments are closed.