Rsa Signature Applied Cryptography Youtube

Rsa Signature Pdf Secrecy Cryptography This video gives an overview of the rsa digital signature. it shows how this scheme is closely related to rsa encryption decryption. Without encryption, every conversation you had online would be visible to anyone. we couldn't have online banking or shopping if we couldn't encrypt our financial information to transmit it safely. rsa stands for rivest shamir adleman, the three people who developed it.
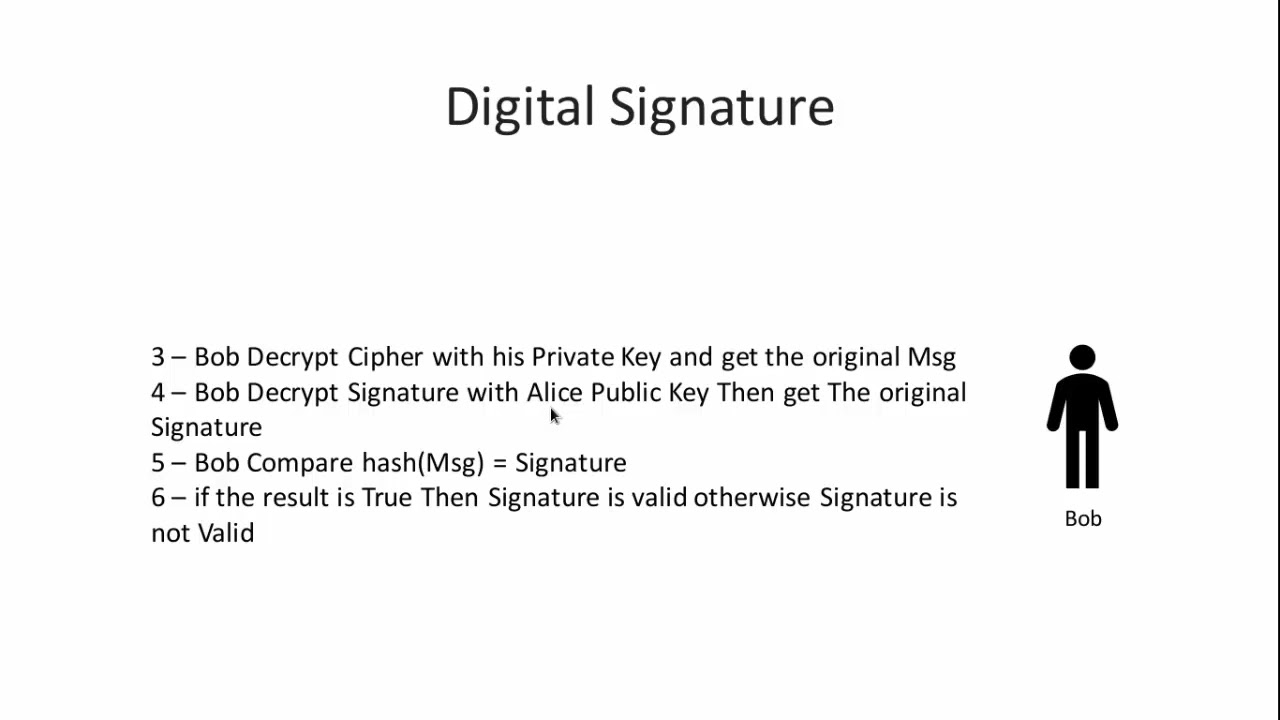
8 Introduction To Cryptography What Is A Digital Signature Rsa In this article, we will learn about the rsa signature scheme, attacks on the rsa digital signature scheme, and the steps of digital signature process creation. Here you can see how to encrypt and decrypt using the rsa procedure step by step. the security of rsa is based on the fact that it is easy to calculate the product n n of two large prime numbers p p and q q. however, it is very difficult to determine the two primes only from the product n n. Rsa signatures can be forged or spoofed in certain scenarios which is shown in the following demonstration: a and b are communicating on an unencrypted channel and attacker e is able to capture their messages $m$. After the keys are generated, we shall compute rsa digital signatures and verify signatures by a simple modular exponentiation (by encrypting and decrypting the message hash).

Rsa Digital Signature Scheme Youtube Rsa signatures can be forged or spoofed in certain scenarios which is shown in the following demonstration: a and b are communicating on an unencrypted channel and attacker e is able to capture their messages $m$. After the keys are generated, we shall compute rsa digital signatures and verify signatures by a simple modular exponentiation (by encrypting and decrypting the message hash). Interestingly, one can run the rsa encryption scheme “backwards” to obtain a signature scheme. that is, we use the decryption algorithm to sign, and the encryption algorithm to verify. Explore the world of rsa digital signatures, their importance in cryptography, and how they ensure data integrity and authenticity. Topics covered: security definition for signature schemes, necessary conditions for the security of the basic rsa signature scheme, insecurity of the basic rsa security scheme, rsa full. This article explains how rsa digital signatures work by describing the principles and intuitions behind them, and breaking down the signature creation and validation steps. the reader can.
Comments are closed.