Rsa Blind Signatures Applied Cryptography Youtube
Applied Cryptography Rsa Cryptosystem Part 1 Youtube This video is part of an online course, applied cryptography. check out the course here: udacity course cs387. This video is part of an online course, applied cryptography. check out the course here: udacity course cs387.

Digital Signatures Rsa Youtube Simple introduction of david chaum's blind signatures utilizing rsa encryption. there are inverse mod calculators online for computing the inverse of (r)to. Video lectures for alfred menezes's introductory course on the fundamental building blocks used in cryptography. more. Blind signatures are a form of digital signature in which the content of the message is hidden (blinded) before it is signed by any of the authorities involved in the process. In rsa based cryptography, a user's private key —which can be used to sign messages, or decrypt messages sent to that user—is a pair of large prime numbers chosen at random and kept secret.
Digital Signature Using Rsa Algorithm Youtube Blind signatures are a form of digital signature in which the content of the message is hidden (blinded) before it is signed by any of the authorities involved in the process. In rsa based cryptography, a user's private key —which can be used to sign messages, or decrypt messages sent to that user—is a pair of large prime numbers chosen at random and kept secret. To address this, the development of quantum resistant cryptographic protocols is essential for maintaining the security of digital transactions and data. aligning with the same goal, this work aims to thoroughly review the background of lattice based blind signatures. Chaum observed that a user could ‘blind’ an rsa message for a bank to sign, by first selecting a random r (in the range 1 through n 1, such that r has an inverse mod n) and giving the bank the blinded value (m * r^e) mod n. Rsa (rivest–shamir–adleman) is one of the first public key cryptosystems and is widely used for secure data transmission. in this blog post i will try to explain the rsa cryptosystem using simple mathematical principles. The most famous example of public key cryptography is the rsa encryption scheme, invented by ron rivest, adi shamir, and len adleman. rsa is based on the idea that factoring large numbers is hard, even though multiplication is easy.

Rsa And Blind Signatures Example Youtube To address this, the development of quantum resistant cryptographic protocols is essential for maintaining the security of digital transactions and data. aligning with the same goal, this work aims to thoroughly review the background of lattice based blind signatures. Chaum observed that a user could ‘blind’ an rsa message for a bank to sign, by first selecting a random r (in the range 1 through n 1, such that r has an inverse mod n) and giving the bank the blinded value (m * r^e) mod n. Rsa (rivest–shamir–adleman) is one of the first public key cryptosystems and is widely used for secure data transmission. in this blog post i will try to explain the rsa cryptosystem using simple mathematical principles. The most famous example of public key cryptography is the rsa encryption scheme, invented by ron rivest, adi shamir, and len adleman. rsa is based on the idea that factoring large numbers is hard, even though multiplication is easy.
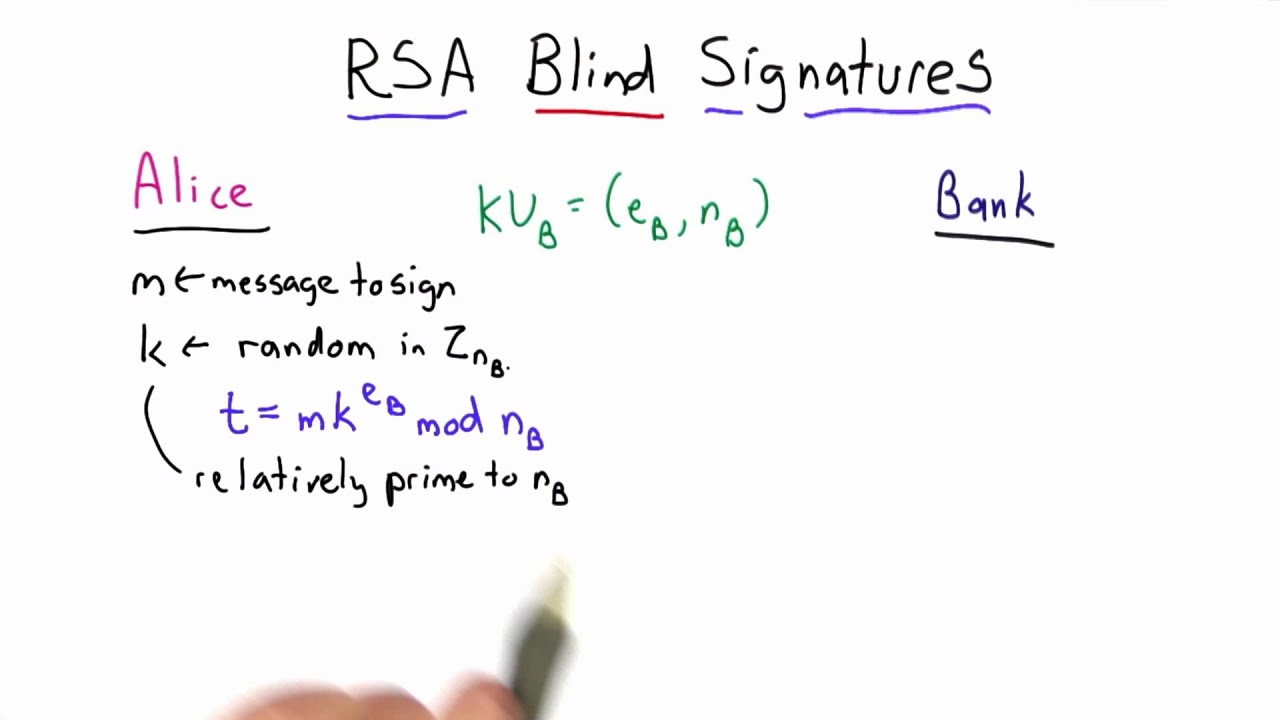
Rsa Blind Signatures Applied Cryptography Youtube Rsa (rivest–shamir–adleman) is one of the first public key cryptosystems and is widely used for secure data transmission. in this blog post i will try to explain the rsa cryptosystem using simple mathematical principles. The most famous example of public key cryptography is the rsa encryption scheme, invented by ron rivest, adi shamir, and len adleman. rsa is based on the idea that factoring large numbers is hard, even though multiplication is easy.
Comments are closed.