Reverse Engineering Mac Malware Sarah Edwards

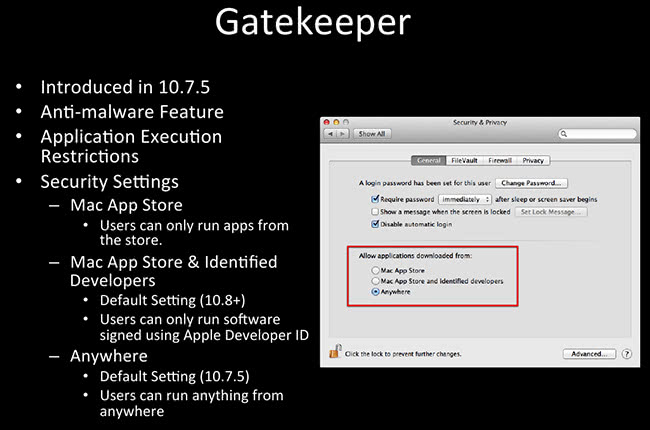
Reverse Engineering Malware Pdf Ransomware Malware Very&useful&for&reverse&engineering!& dtrace n 'syscall::open*:entry { printf("%s %s",execname,copyinstr(arg0)); }! fs usage! fs usage –f pathname! 08:05:21.631155 getattrlist applications messages.app 0.000011 dock.513976! !. Digital forensic analyst sarah edwards presents an extensive review of tools and approaches applicable for reverse engineering mac malware at b sides event.
Reverse Engineering Mac Malware Part 1 Macsecurity Applicagon tracing “trace” program execugon, file system events, network communicagons for use in troubleshoogng. low ‐level logging verbose very useful for reverse engineering! tools: dtrace, fs usage, xcode instruments. Dynamic malware reverse engineering helps forensic analysts and reverse engineers gather quick data points such as callout domains, file download urls or ip. Presentations reverse engineering mac malware reverse engineering mac malware.pdf. This presentation is intended for those familiar with dynamic analysis (with a touch of static thrown in) or for those reverse engineering masters of the windows executable to get a introductory idea of how to start analyzing mac malware.
Reverse Engineering Mac Malware Part 4 Presentations reverse engineering mac malware reverse engineering mac malware.pdf. This presentation is intended for those familiar with dynamic analysis (with a touch of static thrown in) or for those reverse engineering masters of the windows executable to get a introductory idea of how to start analyzing mac malware. A self described mac nerd, sarah edwards is a forensic analyst, author, speaker, and both author and instructor of sans for518: mac and ios forensic analysis and incident response. Edwards' presentation on reverse engineering mac malware features a deep dive into the complex world of mac malware detection, analysis, and mitigation. she explores the growing threat landscape of macos and presents her unique approach to studying and mitigating these threats. While i didn’t find anything particularly groundbreaking, there are some forensic artifacts that could be useful! the presentations is available here on my github. i’ve uploaded my presentation that i gave at the lovely sikkerhetsfestivalen 2024 in lillehammer, norway. Sarah edwards is an instructor with sans and the author instructor of sans for518: mac forensic analysis. a devote user of apple devices for many years, sarah has worked specifically in mac.
Reverse Engineering Mac Malware Part 3 Macsecurity A self described mac nerd, sarah edwards is a forensic analyst, author, speaker, and both author and instructor of sans for518: mac and ios forensic analysis and incident response. Edwards' presentation on reverse engineering mac malware features a deep dive into the complex world of mac malware detection, analysis, and mitigation. she explores the growing threat landscape of macos and presents her unique approach to studying and mitigating these threats. While i didn’t find anything particularly groundbreaking, there are some forensic artifacts that could be useful! the presentations is available here on my github. i’ve uploaded my presentation that i gave at the lovely sikkerhetsfestivalen 2024 in lillehammer, norway. Sarah edwards is an instructor with sans and the author instructor of sans for518: mac forensic analysis. a devote user of apple devices for many years, sarah has worked specifically in mac.
Comments are closed.