Reverse Engineering Mac Malware Part 3 Macsecurity

Reverse Engineering Malware Pdf Ransomware Malware The issues described and analyzed in this part are all about dynamic analysis of mac apps, including virtualization, application tracing and applicable tools. Very&useful&for&reverse&engineering!& dtrace n 'syscall::open*:entry { printf("%s %s",execname,copyinstr(arg0)); }! fs usage! fs usage –f pathname! 08:05:21.631155 getattrlist applications messages.app 0.000011 dock.513976! !.

Guide To Malware Reverse Engineering And Incident Response Pdf New lazarus apt campaign: “mach o man” macos malware kit hits businesses editor’s note: the research is authored by mauro eldritch, offensive security expert and a founder of bca ltd, a company dedicated to threat intelligence and hunting. you can find mauro on x. In this series of posts, we’ve learned how to set up a safe environment to test macos malware and how to use static analysis and dynamic analysis to reverse engineer a mach o binary. What tools attackers are using: a new macos malware kit, mach o man, built as native binaries to target macos environments. what attackers are after: credentials and active sessions that allow immediate access to business systems. how data is exfiltrated: sensitive data is sent via telegram, blending into normal communication traffic. Attacks on the macos platform are on the rise, but there's a lack of material for those who want to learn macos reverse engineering and malware analysis techniques. in this ebook, you'll learn: how to set up a safe environment and acquire the tools and samples you need how to take a sample file,.
Reverse Engineering Mac Malware Part 1 Macsecurity What tools attackers are using: a new macos malware kit, mach o man, built as native binaries to target macos environments. what attackers are after: credentials and active sessions that allow immediate access to business systems. how data is exfiltrated: sensitive data is sent via telegram, blending into normal communication traffic. Attacks on the macos platform are on the rise, but there's a lack of material for those who want to learn macos reverse engineering and malware analysis techniques. in this ebook, you'll learn: how to set up a safe environment and acquire the tools and samples you need how to take a sample file,. The goal of this book is to accommodate the reader with radare2, which is quickly becoming a bread & butter tool for any reverse engineer, malware analyst or biweekly ctf player. In this series of posts, we’ve learned how to set up a safe environment to test macos malware and how to use static analysis and dynamic analysis to reverse engineer a mach o binary. In the following pages, you will find practical tips with examples on how to use r2 to deal with macos malware that deploys anti analysis techniques, how to decrypt encrypted strings, how to compare and diff binaries, and how to write and iterate your yara hunting rules. The next layer of defense is to help ensure that if malware appears on any mac, it’s quickly identified and blocked, both to halt spread and to remediate the mac systems it’s already gained a foothold on.
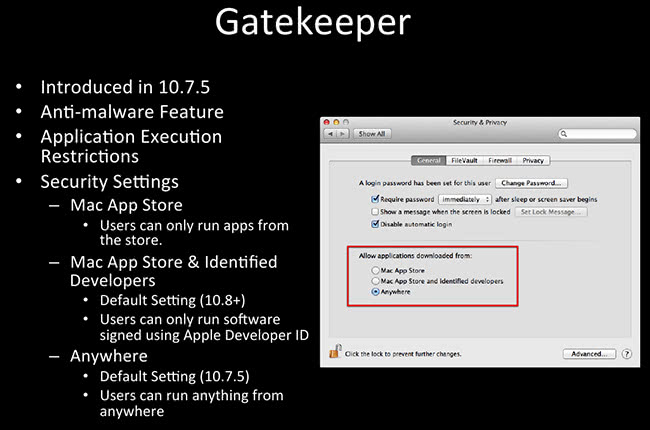
Reverse Engineering Mac Malware Part 3 Macsecurity The goal of this book is to accommodate the reader with radare2, which is quickly becoming a bread & butter tool for any reverse engineer, malware analyst or biweekly ctf player. In this series of posts, we’ve learned how to set up a safe environment to test macos malware and how to use static analysis and dynamic analysis to reverse engineer a mach o binary. In the following pages, you will find practical tips with examples on how to use r2 to deal with macos malware that deploys anti analysis techniques, how to decrypt encrypted strings, how to compare and diff binaries, and how to write and iterate your yara hunting rules. The next layer of defense is to help ensure that if malware appears on any mac, it’s quickly identified and blocked, both to halt spread and to remediate the mac systems it’s already gained a foothold on.
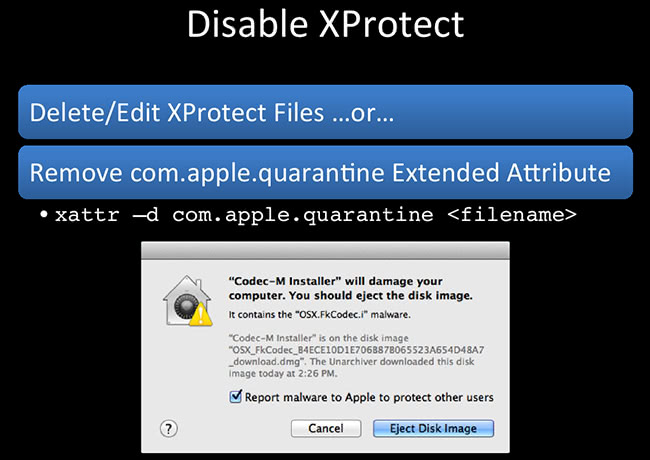
Reverse Engineering Mac Malware Part 3 Macsecurity In the following pages, you will find practical tips with examples on how to use r2 to deal with macos malware that deploys anti analysis techniques, how to decrypt encrypted strings, how to compare and diff binaries, and how to write and iterate your yara hunting rules. The next layer of defense is to help ensure that if malware appears on any mac, it’s quickly identified and blocked, both to halt spread and to remediate the mac systems it’s already gained a foothold on.
Comments are closed.