Remote Access Security Best Practices Instasafe

Remote Access Security Best Practices Pdf Cloud Computing Password Ensuring a secure work from home environment: remote access security best practices. instasafe acts like a natural extension to our network infrastructure. with its clientless functionality, it works seamlessly in the background, and causes no latency issues whatsoever during usage. Ensure remote access security with instasafe’s cloud based ztaa solution. with the increase in security breaches, a standard vpn is no longer sufficient.

Securing Remote Work Common Risks And Best Practices Instasafe Eliminate the need for vpns and obsolete security tools. simplify deployment and maintenance with a hyperscalable saas solution that doesn't need complex firewalls. by enabling the least privilege access model, grants access to users and devices following continuous verification. With features like seamless integration with identity providers, multi factor authentication, single sign on, adaptive access policies, and unified endpoint controls, enterprises can secure access to on premise and cloud applications for remote employees. Here are 6 essential steps to protect your company:🚀 1️⃣ opt for secure software: invest in enterprise grade solutions for robust network security. 2️⃣ formalize cybersecurity policies. Setting up and managing vpns and letting every resource access request pass through the vpn is the best remote security practice. vpns act as a thin layer of defense for remote access networks. they are beneficial in diverting certain kinds of attacks such as data sniffing.

What Is Cloud Application Security Instasafe Here are 6 essential steps to protect your company:🚀 1️⃣ opt for secure software: invest in enterprise grade solutions for robust network security. 2️⃣ formalize cybersecurity policies. Setting up and managing vpns and letting every resource access request pass through the vpn is the best remote security practice. vpns act as a thin layer of defense for remote access networks. they are beneficial in diverting certain kinds of attacks such as data sniffing. We have managed to easily extend always on connectivity and secure access to our cloud and erp applications with instasafe zero trust access. it is much faster than a vpn and much easier to manage. Explore instasafe's zero trust solutions with our comprehensive resource center. download brochures, whitepapers, and guides for secure remote access and more. Ensuring a secure work from home environment: remote access security best practices. instasafe acts like a natural extension to our network infrastructure. with its clientless functionality, it works seamlessly in the background, and causes no latency issues whatsoever during usage. This document provides an overview, technical details, and guidance for deploying and using instasafe secure access, a zero trust based secure access solution designed for modern enterprises.
Secure Remote Access Remote Access Solution Security Instasafe We have managed to easily extend always on connectivity and secure access to our cloud and erp applications with instasafe zero trust access. it is much faster than a vpn and much easier to manage. Explore instasafe's zero trust solutions with our comprehensive resource center. download brochures, whitepapers, and guides for secure remote access and more. Ensuring a secure work from home environment: remote access security best practices. instasafe acts like a natural extension to our network infrastructure. with its clientless functionality, it works seamlessly in the background, and causes no latency issues whatsoever during usage. This document provides an overview, technical details, and guidance for deploying and using instasafe secure access, a zero trust based secure access solution designed for modern enterprises.
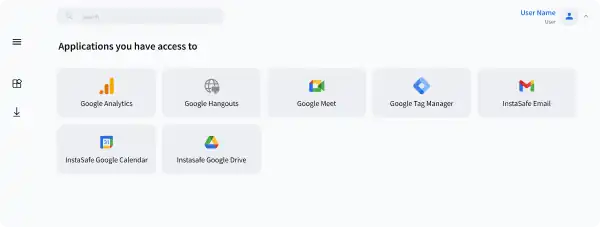
Secure Remote Access Remote Access Solution Security Instasafe Ensuring a secure work from home environment: remote access security best practices. instasafe acts like a natural extension to our network infrastructure. with its clientless functionality, it works seamlessly in the background, and causes no latency issues whatsoever during usage. This document provides an overview, technical details, and guidance for deploying and using instasafe secure access, a zero trust based secure access solution designed for modern enterprises.
Comments are closed.