Instasafe Stick Access Using Usb
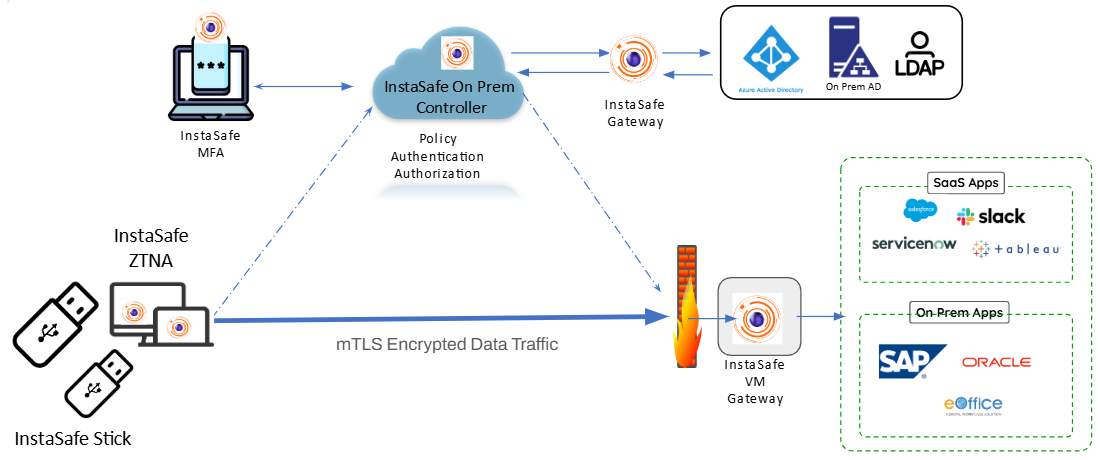
Instasafe Stick Access Using Usb Users need to just plug in the usb drive into their system, reboot and the system is now ready to access predefined corporate applications securely using instasafe zero trust access solution along with multi factor authentication. This section provides a step by step technical guide for creating a bootable instasafe usb stick used for secure access to enterprise applications via a hardened os environment.
Instasafe Stick Instasafe Documentation Hub Resources on cyber security and how the internet works from instasafe 1 article what's new in ztaa. Securing access for icewarp email in the rapidly evolving digital landscape, email remains a critical. In some cases, the admins might silently deploy and install the isa app on the end points using gpos or an sccm. in such a scenario, users might only be required to configure the isa app with their credentials on their respective devices. however, that is out of scope for this guide. Instasafe provides comprehensive zero trust solution along with identity and access management (iam) and privileged access management (pam) solution.
Instasafe Stick Instasafe Documentation Hub In some cases, the admins might silently deploy and install the isa app on the end points using gpos or an sccm. in such a scenario, users might only be required to configure the isa app with their credentials on their respective devices. however, that is out of scope for this guide. Instasafe provides comprehensive zero trust solution along with identity and access management (iam) and privileged access management (pam) solution. Instasafe ztaa is a secure access control management solution that helps enterprises to protect its on premises as well as cloud based digital assets. ztaa uses application specific tunnelling and software defined perimeters (encryption) to separate access control and data planes. Instasafe stick only allows access to corporate applications and blocks the internet from browsing any external sites. with instasafe zta and mfa, users can still experience secure and seamless access to their applications. With the isa app connected, you should now be able to access your organization's internal applications as per the access policies defined. the resources that can be accessed by the user can be viewed in the routing table. here is an example of the windows routing table. The dlp software helps in blacklisting or whitelisting devices, managing access policies and blocking usb ports to control usage effectively. companies can monitor their usb usage and can physically block any device if required.

Signin Myinstasafe Instasafe ztaa is a secure access control management solution that helps enterprises to protect its on premises as well as cloud based digital assets. ztaa uses application specific tunnelling and software defined perimeters (encryption) to separate access control and data planes. Instasafe stick only allows access to corporate applications and blocks the internet from browsing any external sites. with instasafe zta and mfa, users can still experience secure and seamless access to their applications. With the isa app connected, you should now be able to access your organization's internal applications as per the access policies defined. the resources that can be accessed by the user can be viewed in the routing table. here is an example of the windows routing table. The dlp software helps in blacklisting or whitelisting devices, managing access policies and blocking usb ports to control usage effectively. companies can monitor their usb usage and can physically block any device if required.
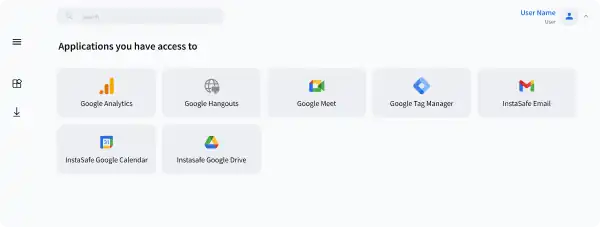
Zero Trust Security Zero Trust Model For Enterprises Instasafe With the isa app connected, you should now be able to access your organization's internal applications as per the access policies defined. the resources that can be accessed by the user can be viewed in the routing table. here is an example of the windows routing table. The dlp software helps in blacklisting or whitelisting devices, managing access policies and blocking usb ports to control usage effectively. companies can monitor their usb usage and can physically block any device if required.
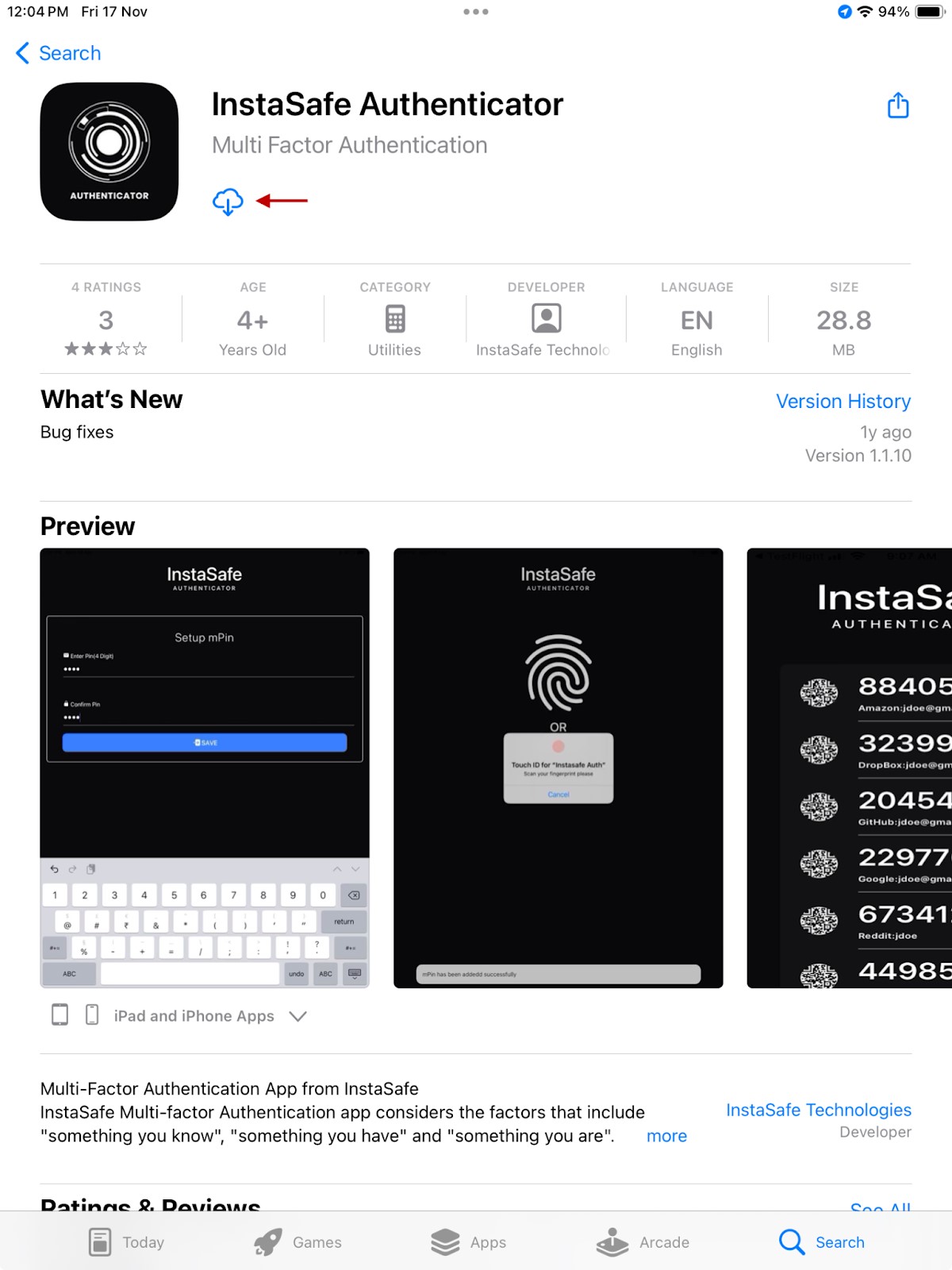
Instasafe Authenticator Instasafe Documentation Hub
Comments are closed.