Python Basics Tutorial Cryptography Pbkdf2hmac Algorithm Salt Argument Data Encryption
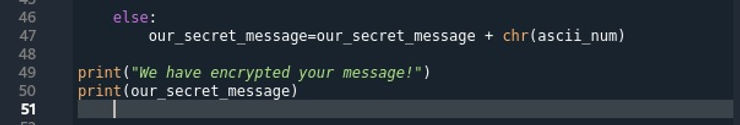
Cryptography Basics For Hackers Part 04 Building A Simple Encryption Here, we use the pbkdf2 hmac function from hashlib. the function takes the hash algorithm name ('sha256'), the password, the salt, the number of iterations, and the desired key length (dklen = 32). Pbkdf2 is a simple cryptographic key derivation function, which is resistant to dictionary attacks and rainbow table attacks. it is based on iteratively deriving hmac many times with some padding. the pbkdf2 algorithm is described in the internet standard rfc 2898 (pkcs #5).
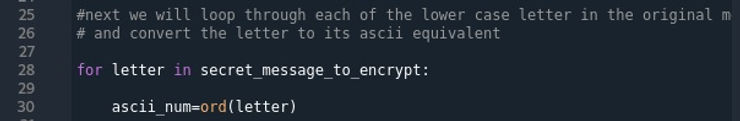
Cryptography Basics For Hackers Part 04 Building A Simple Encryption Pbkdf2 is a simple cryptographic key derivation function, which is resistant to dictionary attacks and rainbow table attacks. it is based on iteratively deriving hmac many times with some padding. the pbkdf2 algorithm is described in the internet standard rfc 2898 (pkcs #5). Learn about the salt argument for vector initialization used in cryptography for python programming patreon: more. Learn how to implement secure string encryption in python using pbkdf2, with code examples and performance benchmarks to help you balance security and computational cost. Pbkdf2 (password based key derivation function 2) provides a robust solution by adding a salt and iterating the hashing process, making brute force attacks significantly harder. this guide will walk you through implementing pbkdf2 in python using the hashlib module.
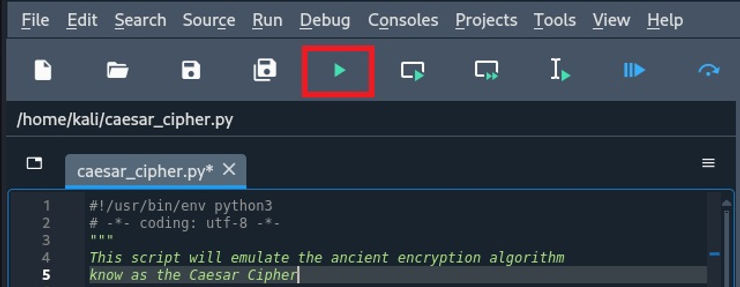
Cryptography Basics For Hackers Part 04 Building A Simple Encryption Learn how to implement secure string encryption in python using pbkdf2, with code examples and performance benchmarks to help you balance security and computational cost. Pbkdf2 (password based key derivation function 2) provides a robust solution by adding a salt and iterating the hashing process, making brute force attacks significantly harder. this guide will walk you through implementing pbkdf2 in python using the hashlib module. In this article, we'll walk you through the fundamentals of pbkdf2, how to implement it using python libraries, and best practices for enhancing security in your applications. Below you can find the extended example of how to use pbkdf2hmac key derivation function in python. Features file encryption: encrypts a file using a password to generate a unique key. file decryption: decrypts the encrypted file using the correct password. password based security: passwords are used to derive a cryptographic key via pbkdf2 hmac. Pbkdf2 is the most widespread algorithm for deriving keys from a password, originally defined in version 2.0 of the pkcs#5 standard or in rfc2898. it is computationally expensive (a property that can be tuned via the count parameter) so as to thwart dictionary and rainbow tables attacks.

Cryptography Basics For Hackers Part 04 Building A Simple Encryption In this article, we'll walk you through the fundamentals of pbkdf2, how to implement it using python libraries, and best practices for enhancing security in your applications. Below you can find the extended example of how to use pbkdf2hmac key derivation function in python. Features file encryption: encrypts a file using a password to generate a unique key. file decryption: decrypts the encrypted file using the correct password. password based security: passwords are used to derive a cryptographic key via pbkdf2 hmac. Pbkdf2 is the most widespread algorithm for deriving keys from a password, originally defined in version 2.0 of the pkcs#5 standard or in rfc2898. it is computationally expensive (a property that can be tuned via the count parameter) so as to thwart dictionary and rainbow tables attacks.
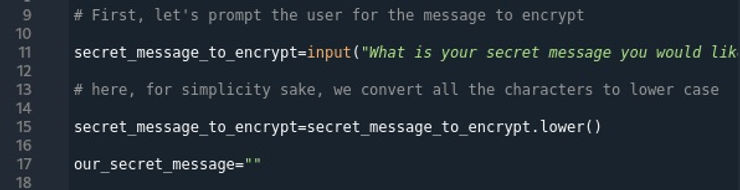
Cryptography Basics For Hackers Part 04 Building A Simple Encryption Features file encryption: encrypts a file using a password to generate a unique key. file decryption: decrypts the encrypted file using the correct password. password based security: passwords are used to derive a cryptographic key via pbkdf2 hmac. Pbkdf2 is the most widespread algorithm for deriving keys from a password, originally defined in version 2.0 of the pkcs#5 standard or in rfc2898. it is computationally expensive (a property that can be tuned via the count parameter) so as to thwart dictionary and rainbow tables attacks.
Cryptography Basics For Hackers Part 04 Building A Simple Encryption
Comments are closed.