Python Basics Tutorial Cryptography Pbkdf2hmac Object Verify Method Data Encryption

Cryptography With Python Tutorial Pdf Cipher Cryptography Cryptography module python, data & more · course 17 videos last updated on jul 8, 2021. Whether you choose the cryptography library for its comprehensive cryptographic features or the hashlib library from the standard library for its simplicity, proper implementation of pbkdf2 is crucial for protecting user passwords and sensitive data.
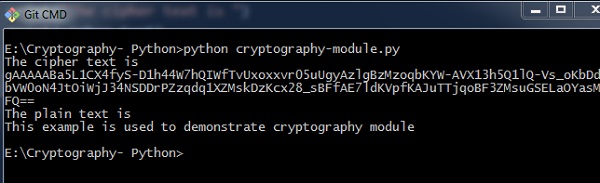
Python Modules Of Cryptography Tutorial You'll learn essential techniques like hashing (sha 256) for verifying file integrity, symmetric encryption (aes), and asymmetric encryption (rsa) using public and private keys. the practical focus of the tutorial involves building a fully functional command line cryptography tool in python. Hmac is quite simple to implement with python. here's gethmac function hard coded to sha256 and an even shorter pbkdf2: as you can see, hmac is just creating a couple padded 64 byte arrays from key and then two nested hash calls. it also makes the pbkdf2() quite easy to read compared to hmac library!. Pbkdf2 is a simple cryptographic key derivation function, which is resistant to dictionary attacks and rainbow table attacks. it is based on iteratively deriving hmac many times with some padding. the pbkdf2 algorithm is described in the internet standard rfc 2898 (pkcs #5). Explore advanced cryptographic operations including rsa encryption, aes encryption, sha 256 hashing, pbkdf2 key derivation, and hmac generation in python.

Python And Cryptography Basics Python Lore Pbkdf2 is a simple cryptographic key derivation function, which is resistant to dictionary attacks and rainbow table attacks. it is based on iteratively deriving hmac many times with some padding. the pbkdf2 algorithm is described in the internet standard rfc 2898 (pkcs #5). Explore advanced cryptographic operations including rsa encryption, aes encryption, sha 256 hashing, pbkdf2 key derivation, and hmac generation in python. This guide will walk you through implementing pbkdf2 in python using the hashlib module. you'll learn how to properly generate secure password hashes and verify them, ensuring your application's user data stays protected. This project demonstrates the practical application of various cryptography techniques using python. the techniques covered include aes cbc encryption, rsa encryption, hybrid encryption, manual rsa implementation, and steganography. python cryptography techniques task1 aes cbc.py at master · dameerpramanik python cryptography techniques. Learn how to implement secure string encryption in python using pbkdf2, with code examples and performance benchmarks to help you balance security and computational cost. Since python 3.4 you can use the built in to generate check pbkdf2 hashes. here is an example using pbkdf2 with hmac (sha1):.
Comments are closed.