Playbook For Phishing

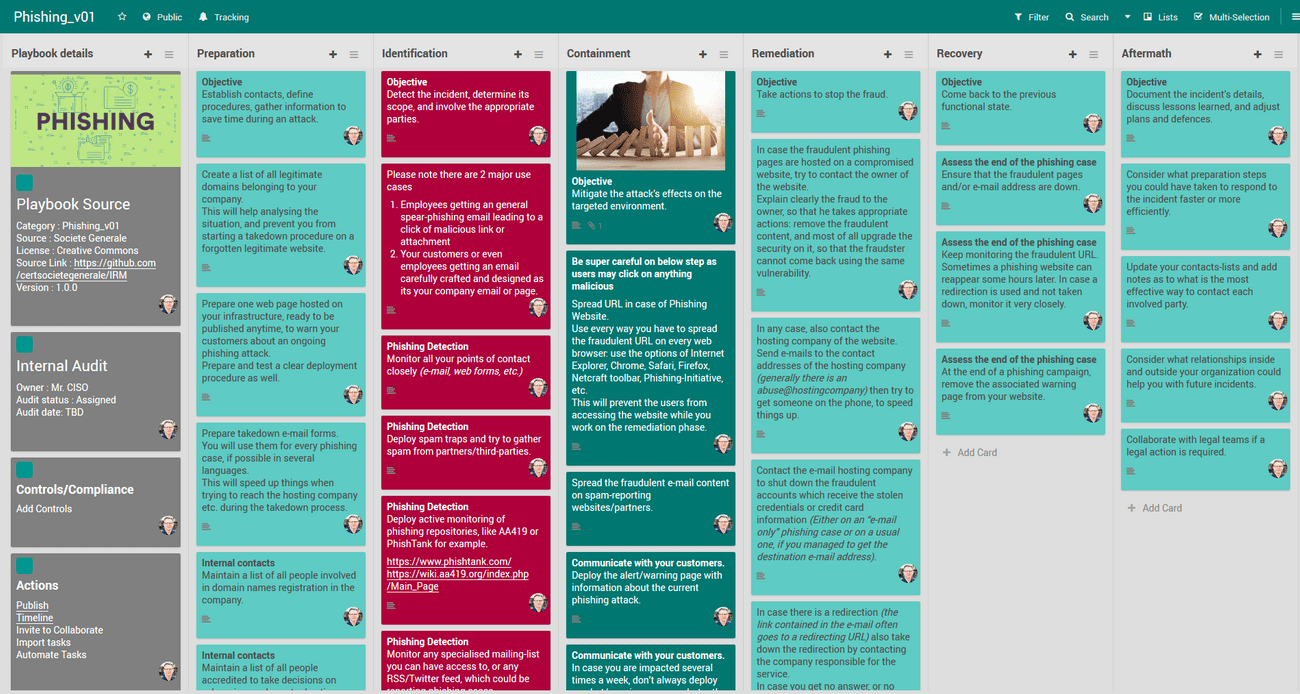
Phishing Playbook Pdf The phishing incident response playbook contains all 7 steps defined by the nist incident response process. Flexibleir provides you with different flavors of best practice playbooks for the same threat. this will help to get multiple perspectives to handle today’s complex targeted attacks.

Playbook Phishing From Github Pdf Phishing Security Playbook: phishing investigate, remediate (contain, eradicate), and communicate in parallel! assign steps to individuals or teams to work concurrently, when possible; this playbook is not purely sequential. use your best judgment. This playbook provides a structured approach to managing phishing incidents, ensuring that organizations are prepared, able to detect and respond to threats, and continuously improve their. Conclusions overall, this playbook has reviewed the necessary steps that you need to take in case your business or corporation is impacted by a phishing attack. What is a phishing playbook? the phishing playbook is a structured, strategic document or protocol that defines how an organisation prepares for, detects, responds to, and recovers from phishing attempts.

Akr76ildqist3no2mbacla Activity Use A Playbook To Respond To A Conclusions overall, this playbook has reviewed the necessary steps that you need to take in case your business or corporation is impacted by a phishing attack. What is a phishing playbook? the phishing playbook is a structured, strategic document or protocol that defines how an organisation prepares for, detects, responds to, and recovers from phishing attempts. At underdefense, we handle hundreds of phishing emails each month, many bypassing traditional security measures. our automated phishing playbook lets us quickly triage and mitigate these threats, minimizing potential damage and enhancing our overall security posture. Playbook phishing from github free download as word doc (.doc .docx), pdf file (.pdf), text file (.txt) or read online for free. this document provides a playbook for investigating, remediating, and communicating about phishing incidents. Phishing campaigns can be particularly dangerous, as they are coordinated and persistent attempts to exploit individuals over a period of time. the purpose of this playbook is to provide. Monitor for recurring phishing attempts. implementing a structured incident response playbook for phishing emails enables organizations to detect, contain, and mitigate security incidents effectively.
Playbook For Phishing At underdefense, we handle hundreds of phishing emails each month, many bypassing traditional security measures. our automated phishing playbook lets us quickly triage and mitigate these threats, minimizing potential damage and enhancing our overall security posture. Playbook phishing from github free download as word doc (.doc .docx), pdf file (.pdf), text file (.txt) or read online for free. this document provides a playbook for investigating, remediating, and communicating about phishing incidents. Phishing campaigns can be particularly dangerous, as they are coordinated and persistent attempts to exploit individuals over a period of time. the purpose of this playbook is to provide. Monitor for recurring phishing attempts. implementing a structured incident response playbook for phishing emails enables organizations to detect, contain, and mitigate security incidents effectively.
Comments are closed.