Phishing Playbook Pdf

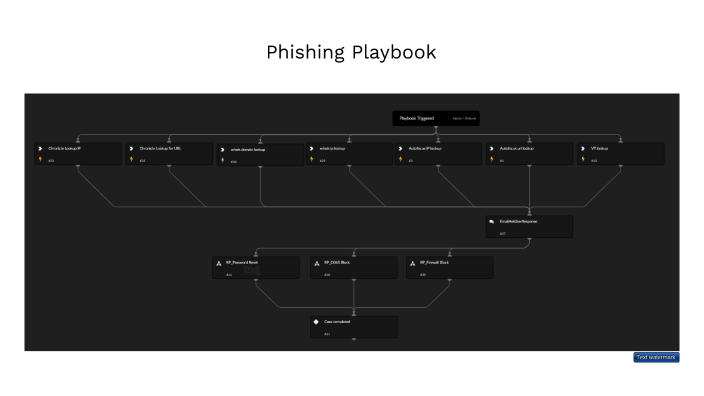
Phishing Playbook Pdf The phishing incident response playbook contains all 7 steps defined by the nist incident response process. A comprehensive, actionable security operations center (soc) playbook designed to detect, analyze, and respond to phishing attacks effectively. this repository contains the full playbook in pdf and latex formats, along with a custom python script for automated email analysis.

Phishing Playbook Summary Pdf Phishing Cybercrime This document provides a phishing incident response playbook with guidance on preparing for and responding to a phishing attack. the preparation phase involves reviewing incident response plans and procedures, threat intelligence, and ensuring access to necessary documentation. At underdefense, we handle hundreds of phishing emails each month, many bypassing traditional security measures. our automated phishing playbook lets us quickly triage and mitigate these threats, minimizing potential damage and enhancing our overall security posture. Monitor for recurring phishing attempts. implementing a structured incident response playbook for phishing emails enables organizations to detect, contain, and mitigate security incidents effectively. Analysts need a phishing response that is fast, handles large volumes, standardized to deal with repeated attacks, and still customizable to deal with unique attacks. demisto provides an out of the box phishing response playbook that helps analysts contain phishing attacks at every step of the kill chain.

Playbook Phishing From Github Pdf Phishing Security Monitor for recurring phishing attempts. implementing a structured incident response playbook for phishing emails enables organizations to detect, contain, and mitigate security incidents effectively. Analysts need a phishing response that is fast, handles large volumes, standardized to deal with repeated attacks, and still customizable to deal with unique attacks. demisto provides an out of the box phishing response playbook that helps analysts contain phishing attacks at every step of the kill chain. Shing: highlypersonalised messages. whaling: targetingexecut. In this playbook, we detail how machine learning, outsourced response service providers, and automated case workflows can accelerate threat resolution and close the “window of vulnerability”. You’ve selected the “phishing” playbook. on the pages that follow, you will find your incident response playbook details broken down by the nist incident handling categories. Use a playbook to respond to a potential phishing attempt at your company. phishing incident response phishing incident response playbook.pdf at main · sjarancio phishing incident response.

Akr76ildqist3no2mbacla Activity Use A Playbook To Respond To A Shing: highlypersonalised messages. whaling: targetingexecut. In this playbook, we detail how machine learning, outsourced response service providers, and automated case workflows can accelerate threat resolution and close the “window of vulnerability”. You’ve selected the “phishing” playbook. on the pages that follow, you will find your incident response playbook details broken down by the nist incident handling categories. Use a playbook to respond to a potential phishing attempt at your company. phishing incident response phishing incident response playbook.pdf at main · sjarancio phishing incident response.
Phishing Playbook By Chuck Owens On Prezi You’ve selected the “phishing” playbook. on the pages that follow, you will find your incident response playbook details broken down by the nist incident handling categories. Use a playbook to respond to a potential phishing attempt at your company. phishing incident response phishing incident response playbook.pdf at main · sjarancio phishing incident response.
Comments are closed.