Pdf Rational Authentication Protocols

Introduction To Authentication Protocols Pdf Authentication We have introduced the use of ideas from game theory to redesign two families of authentication protocols, namely password based authentication and manual authentication protocols, to make them resilient against a powerful and rational intruder. An analytical survey of authentication protocols of this type, which will discover that their security is underlined by the idea of commitment before knowledge, which is refined by two protocol design principles introduced in this survey.

Pdf Rational Authentication Protocols Abstract we use ideas from game theory to improve two families of authentication protocols, namely password based and manual authentication schemes. the protocols will be transformed so that even if an intruder attacks different protocol runs between honest nodes, its expected payoff will still be lower than when it does not attack. Theorem 1: suppose that an intruder can only attack up to a single run of an authentication protocol and succeed with probability , then to discourage the intruder from attacking this protocol, this inequality must hold:. Current methods for authentication based on public key cryptography are vulnerable to quantum computing. we propose a novel approach to authentication in which communicating parties are viewed. Depending on the additional requirements, the authentication can be based either on the symmetric encryption or on the asymmetric cryptographic protocols (asymmetric encryption or electronic signature).

Remote User Authentication Pdf Authentication Virtual Private Network Current methods for authentication based on public key cryptography are vulnerable to quantum computing. we propose a novel approach to authentication in which communicating parties are viewed. Depending on the additional requirements, the authentication can be based either on the symmetric encryption or on the asymmetric cryptographic protocols (asymmetric encryption or electronic signature). We have used ideas from game theory to transform two families of au thentication protocols, namely password based authentication and man ual authentication protocols, to make them resilient against a powerful and rational intruder. This paper proposes an asymptotically optimal protocol family for data authentication that uses short manually authenticated out of band messages and provides security proofs for these protocols and proposes practically secure and efficient sub primitives for applications. Statistics pdf researchr is a web site for finding, collecting, sharing, and reviewing scientific publications, for researchers by researchers. sign up for an account to create a profile with publication list, tag and review your related work, and share bibliographies with your co authors. We have used ideas from game theory to transform two families of authentication protocols, namely password based authentication and manual authentication protocols, to make them resilient against a rational intruder.

Ch02 Authentication Pdf Radio Frequency Identification Biometrics We have used ideas from game theory to transform two families of au thentication protocols, namely password based authentication and man ual authentication protocols, to make them resilient against a powerful and rational intruder. This paper proposes an asymptotically optimal protocol family for data authentication that uses short manually authenticated out of band messages and provides security proofs for these protocols and proposes practically secure and efficient sub primitives for applications. Statistics pdf researchr is a web site for finding, collecting, sharing, and reviewing scientific publications, for researchers by researchers. sign up for an account to create a profile with publication list, tag and review your related work, and share bibliographies with your co authors. We have used ideas from game theory to transform two families of authentication protocols, namely password based authentication and manual authentication protocols, to make them resilient against a rational intruder.

Authentication Protocol Overview Oauth2 Saml Ldap Radius Kerberos Statistics pdf researchr is a web site for finding, collecting, sharing, and reviewing scientific publications, for researchers by researchers. sign up for an account to create a profile with publication list, tag and review your related work, and share bibliographies with your co authors. We have used ideas from game theory to transform two families of authentication protocols, namely password based authentication and manual authentication protocols, to make them resilient against a rational intruder.
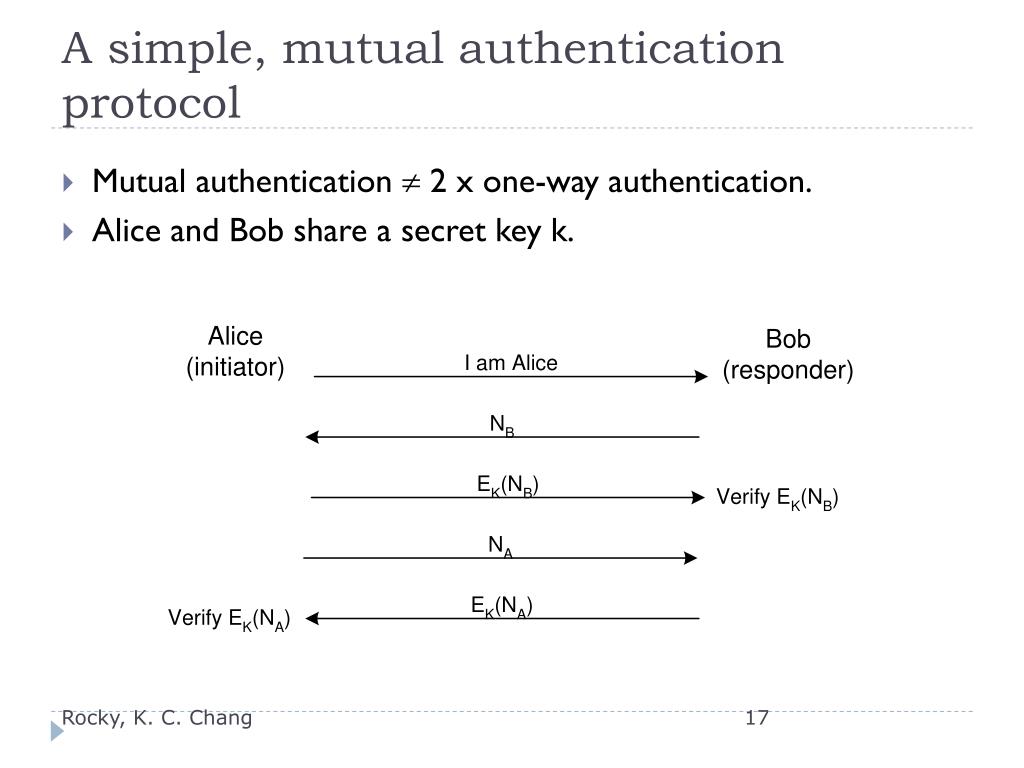
Ppt Authentication Protocols Powerpoint Presentation Free Download
Comments are closed.