Packet Analysis Locked Dorr Security

Packet Analysis Locked Dorr Security Packet analysis and why packet analysis is very important in discovering the events that have lead to a compromise, or even just troubleshooting. it is probably good to question the first thing that comes to mind when someone says packet analysis to discover the lens you are reading this post in. It stores and indexes network traffic in standard pcap format, providing fast, indexed access. provides an intuitive web interface for pcap browsing, searching, and exporting. exposes apis.

Packet Analysis Locked Dorr Security This paper is a comprehensive survey of the utilization of packet analysis, including deep packet inspection, in network forensics, and provides a review of ai powered packet analysis methods with advanced network traffic classification and pattern identification capabilities. Why packet analysis security breaches happens indicators of compromise (ioc) in network traffic network and internet applications way to get in and out of the network detection forensics – what happened?. Learn the techniques and tools used in packet analysis to identify potential security threats and understand network behavior. The room emphasizes practical skills in writing custom snort rules, troubleshooting syntax errors, and performing forensic analysis on captured network traffic. each task involves analyzing pcap files with custom snort rules and extracting specific information from the generated logs, simulating real world network security monitoring scenarios.
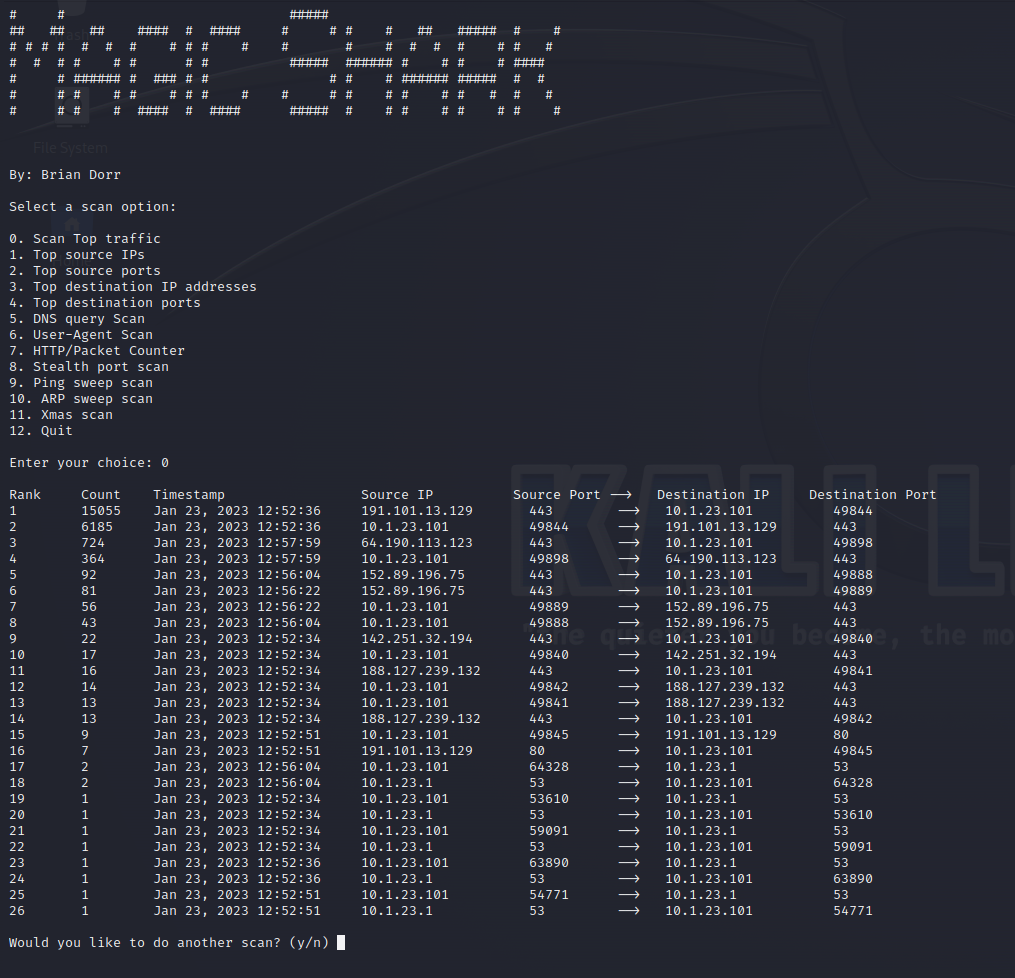
Packet Analysis With Magic Shark Locked Dorr Security Learn the techniques and tools used in packet analysis to identify potential security threats and understand network behavior. The room emphasizes practical skills in writing custom snort rules, troubleshooting syntax errors, and performing forensic analysis on captured network traffic. each task involves analyzing pcap files with custom snort rules and extracting specific information from the generated logs, simulating real world network security monitoring scenarios. With magic shark, i can quickly conduct a scan on what user agents are out there and have it ranked from highest to lowest in terms of how many times it was observed. the limit on what can be done is to the limit of a person's imagination. This paper is a comprehensive survey of the utilization of packet analysis, including deep packet inspection, in network forensics, and provides a review of ai powered packet analysis. Packet analysis is important in cybersecurity as it allows security analysts to monitor network traffic and identify potential security threats such as malware, intrusions, and attempts to exploit vulnerabilities. Read writing from locked dorr security on medium. diversified and experienced cyber operations technician with over 8 years of cyber operations and incident response experience.
Locked Dorr Security Keeping Every Byte Safe With magic shark, i can quickly conduct a scan on what user agents are out there and have it ranked from highest to lowest in terms of how many times it was observed. the limit on what can be done is to the limit of a person's imagination. This paper is a comprehensive survey of the utilization of packet analysis, including deep packet inspection, in network forensics, and provides a review of ai powered packet analysis. Packet analysis is important in cybersecurity as it allows security analysts to monitor network traffic and identify potential security threats such as malware, intrusions, and attempts to exploit vulnerabilities. Read writing from locked dorr security on medium. diversified and experienced cyber operations technician with over 8 years of cyber operations and incident response experience.

Locked Dorr Security Blog Locked Dorr Security Packet analysis is important in cybersecurity as it allows security analysts to monitor network traffic and identify potential security threats such as malware, intrusions, and attempts to exploit vulnerabilities. Read writing from locked dorr security on medium. diversified and experienced cyber operations technician with over 8 years of cyber operations and incident response experience.

Locked Dorr Security Blog Locked Dorr Security
Comments are closed.