Proxmox Locked Dorr Security
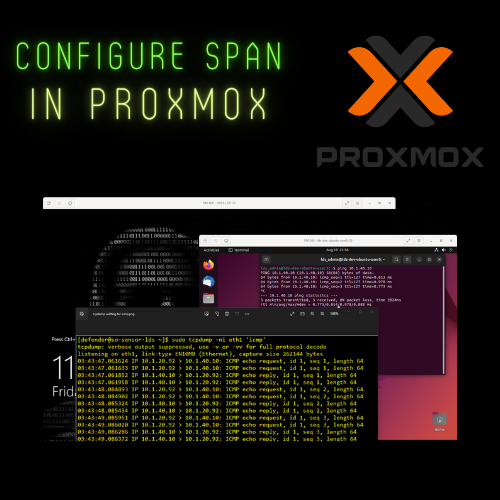
Proxmox Locked Dorr Security It looks like 5 individual sensors, but it is not. i am running 1 virtual machine (sensor) with 1 promiscuous port. the diagram is a depiction of what it effectively… if you have any questions, please comment below and hopefully i can be of assistance to you!. These guides are designed for system administrators and security engineers who need step by step hardening instructions, compliance alignment with the cis debian benchmark, and best practices for enterprise and homelab deployments.
Locked Dorr Security Keeping Every Byte Safe This guide walks you through securing proxmox ve using a defense in depth strategy: os level hardening, a dedicated firewall, a wireguard vpn, and strict access controls. We are planning on doing the hardening of proxmox hosts and implementing a security audit using lynis. during the course of this audit i am sure to hit many roadblocks and will seek help and guidance here in this thread. Read writing from locked dorr security on medium. diversified and experienced cyber operations technician with over 8 years of cyber operations and incident response experience. Set complex passwords and enable 2fa to enable secure logins on your proxmox server. create vlans for virtualized guests to isolate insecure containers. limit port access and set up.

Locked Dorr Security Blog Locked Dorr Security Read writing from locked dorr security on medium. diversified and experienced cyber operations technician with over 8 years of cyber operations and incident response experience. Set complex passwords and enable 2fa to enable secure logins on your proxmox server. create vlans for virtualized guests to isolate insecure containers. limit port access and set up. As we have seen in this post, there is a lot of low hanging fruit when it comes to hardening proxmox ve 9 like hardening ssh, using the proxmox firewall, enforcing 2fa, using trusted certs and others. Learn how to identify, unlock, and prevent locked vm issues in proxmox with this comprehensive guide. discover effective solutions using both the web interface and command line to ensure seamless vm management. There are two methods for removing a lock from a proxmox vm: 1) use the qm unlock command, or 2) manually delete the lock. when it comes to unlocking a proxmox vm, qm unlock should be the first option. to begin, locate the vm id (the number adjacent to the vm in the proxmox gui). Even if you lock down the authentication mechanisms, the additional exposure of the web service (pveproxy) attack surface is generally unacceptable. at some point, a zero day may be released which allows an attacker to own your machine with minimal effort, without authentication.

Locked Dorr Security Blog Locked Dorr Security As we have seen in this post, there is a lot of low hanging fruit when it comes to hardening proxmox ve 9 like hardening ssh, using the proxmox firewall, enforcing 2fa, using trusted certs and others. Learn how to identify, unlock, and prevent locked vm issues in proxmox with this comprehensive guide. discover effective solutions using both the web interface and command line to ensure seamless vm management. There are two methods for removing a lock from a proxmox vm: 1) use the qm unlock command, or 2) manually delete the lock. when it comes to unlocking a proxmox vm, qm unlock should be the first option. to begin, locate the vm id (the number adjacent to the vm in the proxmox gui). Even if you lock down the authentication mechanisms, the additional exposure of the web service (pveproxy) attack surface is generally unacceptable. at some point, a zero day may be released which allows an attacker to own your machine with minimal effort, without authentication.

Locked Dorr Security Blog Locked Dorr Security There are two methods for removing a lock from a proxmox vm: 1) use the qm unlock command, or 2) manually delete the lock. when it comes to unlocking a proxmox vm, qm unlock should be the first option. to begin, locate the vm id (the number adjacent to the vm in the proxmox gui). Even if you lock down the authentication mechanisms, the additional exposure of the web service (pveproxy) attack surface is generally unacceptable. at some point, a zero day may be released which allows an attacker to own your machine with minimal effort, without authentication.
Comments are closed.