Network Parameter Analysis And Malware Detection Using Wireshark

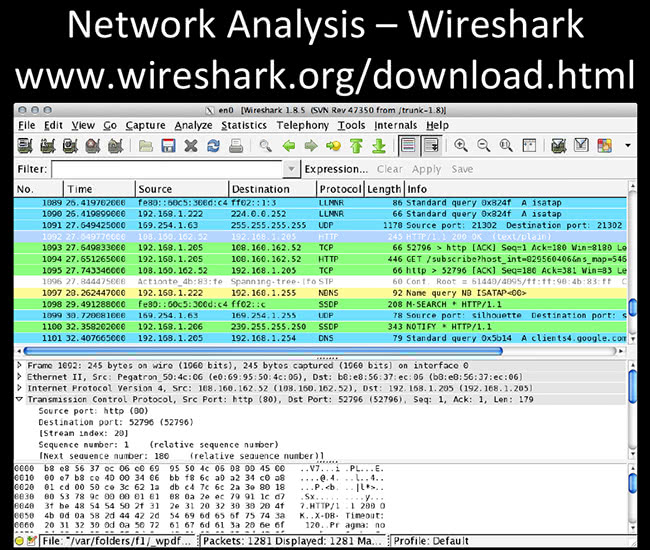
Wireshark Network Forensic Analysis Tutorial Pdf Denial Of Service The purpose of this paper is to demonstrate how wireshark is applied in network protocol diagnosis and can be used to find some basic indicators of compromise for a malware. This video presents my digital assignment (da3) on network parameter analysis and malware detection using wireshark. in this project, i have performed malware analysis using a.

Malicious Network Traffic Analysis With Wireshark Hackmethod Pdf Soc analyst lab — network analysis (malware) using wireshark hello everyone! today’s challenge will be using wireshark to investigate a network pcap consisting of abnormal traffic. Estimating malware impact on network traffic analysis by using wireshark or effective cybersecurity measures that can detect and visualize malware attacks. this research introduces an integrated approach that combines malware detection techniques with geospatial. This book is suitable for both beginners and professionals to learn some simple yet magical tricks for strengthening network security. it specifically provides tip o tricks on the effective use of the network security tool – wireshark. By applying various filters and examining protocol details, the lab aims to enhance our ability to detect suspicious behavior and correlate it with known malware indicators. this hands on experience helps build essential skills in network forensics and cybersecurity threat analysis.
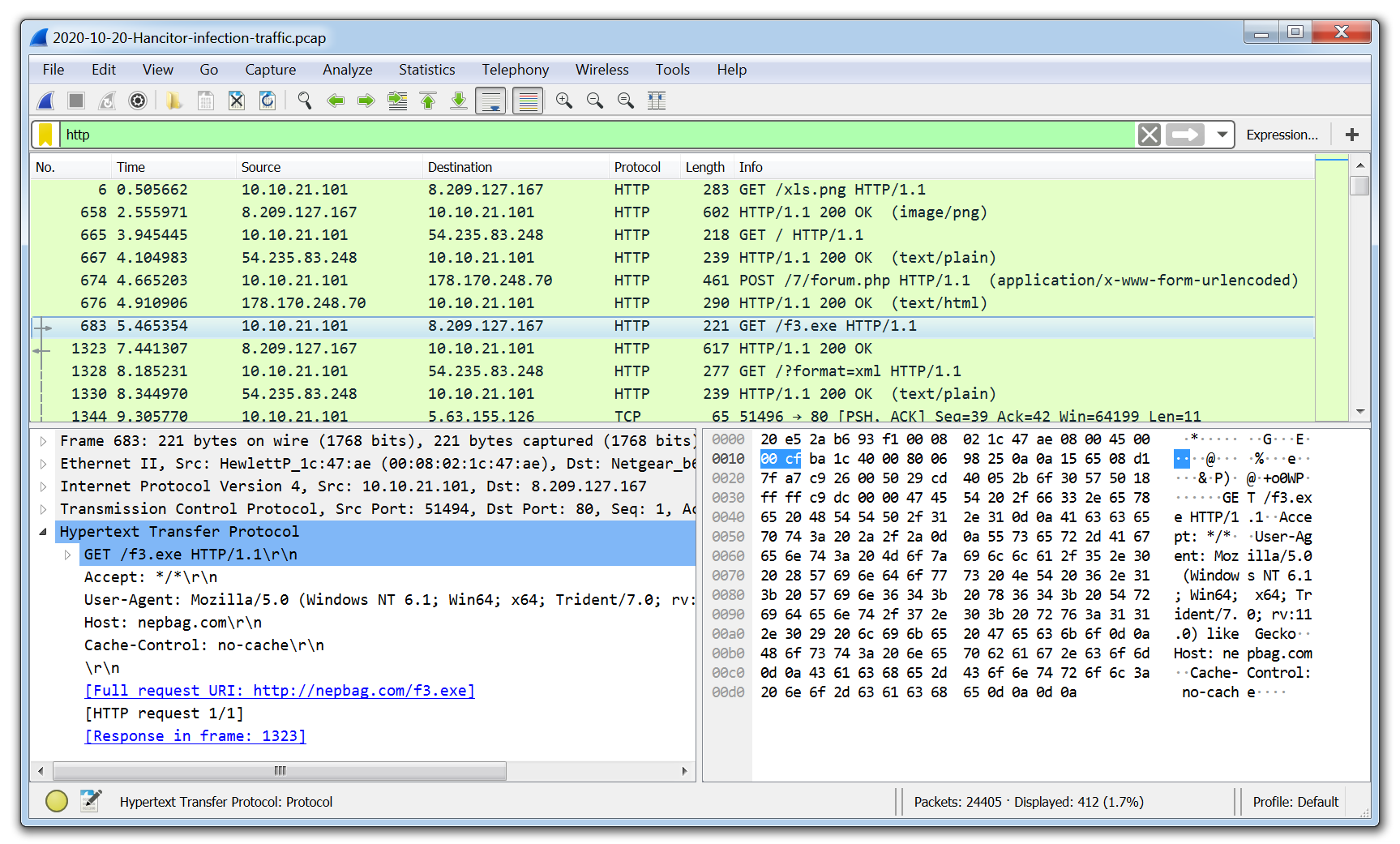
11 Best Malware Analysis Tools And Their Features This book is suitable for both beginners and professionals to learn some simple yet magical tricks for strengthening network security. it specifically provides tip o tricks on the effective use of the network security tool – wireshark. By applying various filters and examining protocol details, the lab aims to enhance our ability to detect suspicious behavior and correlate it with known malware indicators. this hands on experience helps build essential skills in network forensics and cybersecurity threat analysis. Introduction : this data analysis focuses on identifying malware presence using passive network traffic analysis on the pcap dataset dated 2020 04 24. the file was analyzed using wireshark without executing any malicious code. a layered approach was applied by examining dns, http, tcp, and ip level behavior to detect suspicious communication. This paper focuses on real time packet level analysis, dissecting communication patterns, and identifying potential vulnerabilities. employing a comprehensive methodology, the research aims to unveil insights into network behavior, detect anomalies, and enhance overall network performance. The main objective of this research is to analyze the performance and various other parameters related to the integrity of a network in a home based network environment using wireshark. This chapter aims to give an introduction to ethical hacking and networking concepts that will help you to use wireshark for network analysis to identify potential vulnerabilities and weaknesses in a network and to understand how data is being transmitted over the network.
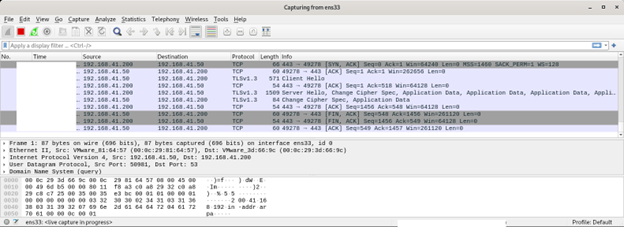
Malware Analysis Basics Introduction : this data analysis focuses on identifying malware presence using passive network traffic analysis on the pcap dataset dated 2020 04 24. the file was analyzed using wireshark without executing any malicious code. a layered approach was applied by examining dns, http, tcp, and ip level behavior to detect suspicious communication. This paper focuses on real time packet level analysis, dissecting communication patterns, and identifying potential vulnerabilities. employing a comprehensive methodology, the research aims to unveil insights into network behavior, detect anomalies, and enhance overall network performance. The main objective of this research is to analyze the performance and various other parameters related to the integrity of a network in a home based network environment using wireshark. This chapter aims to give an introduction to ethical hacking and networking concepts that will help you to use wireshark for network analysis to identify potential vulnerabilities and weaknesses in a network and to understand how data is being transmitted over the network.
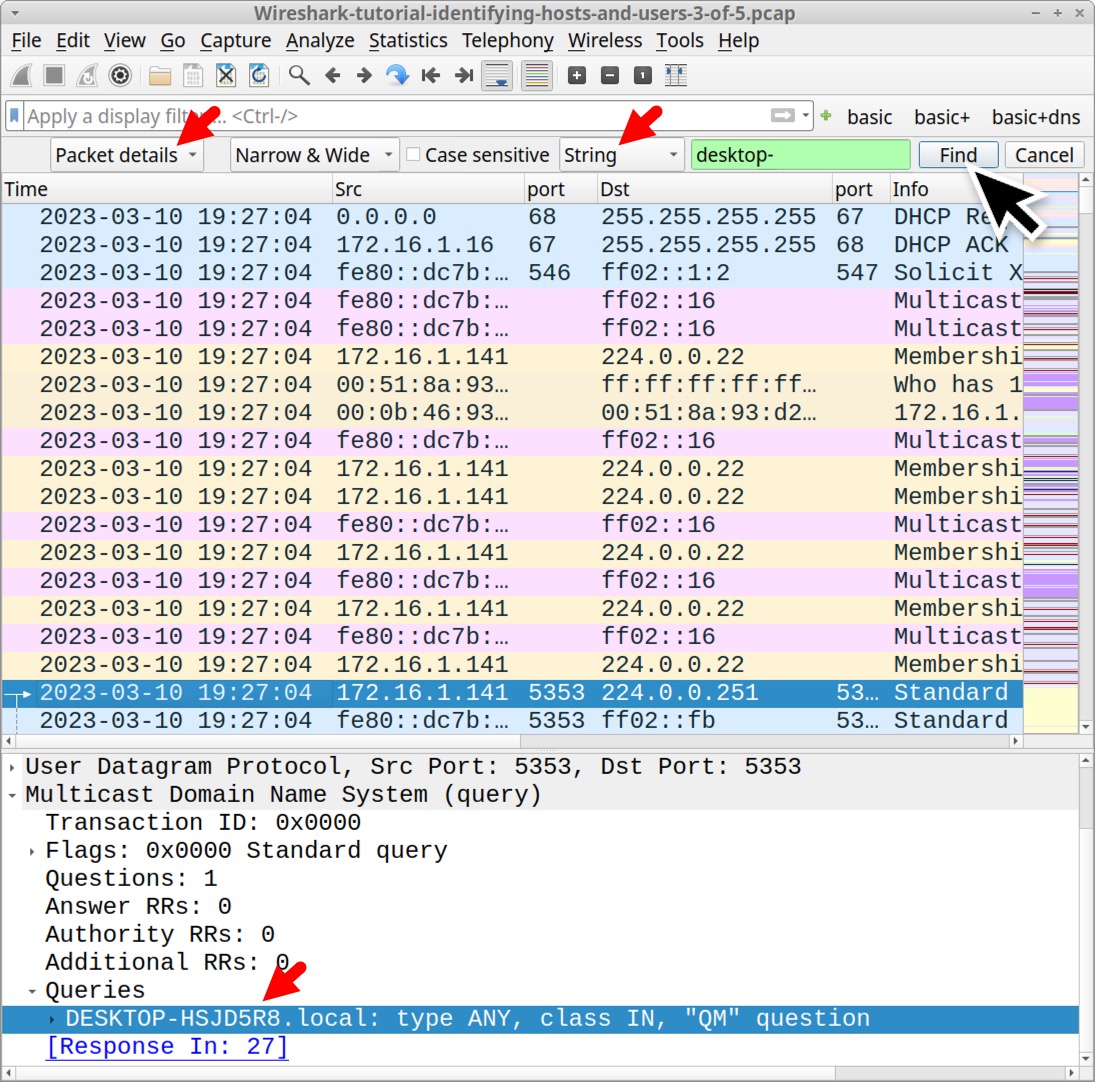
Github Wm171 Malware Traffic Analysis The main objective of this research is to analyze the performance and various other parameters related to the integrity of a network in a home based network environment using wireshark. This chapter aims to give an introduction to ethical hacking and networking concepts that will help you to use wireshark for network analysis to identify potential vulnerabilities and weaknesses in a network and to understand how data is being transmitted over the network.
Reverse Engineering Mac Malware Part 5 Macsecurity
Comments are closed.