Soc Analyst Lab Network Analysis Malware Using Wireshark By
11 Best Malware Analysis Tools And Their Features Soc analyst lab — network analysis (malware) using wireshark hello everyone! today’s challenge will be using wireshark to investigate a network pcap consisting of abnormal traffic. Instead of only listing wireshark as a skill, this project demonstrates how i used wireshark in realistic malware investigation scenarios. i created this project as part of my transition into cybersecurity, specifically toward entry level cybersecurity analyst and soc analyst roles.
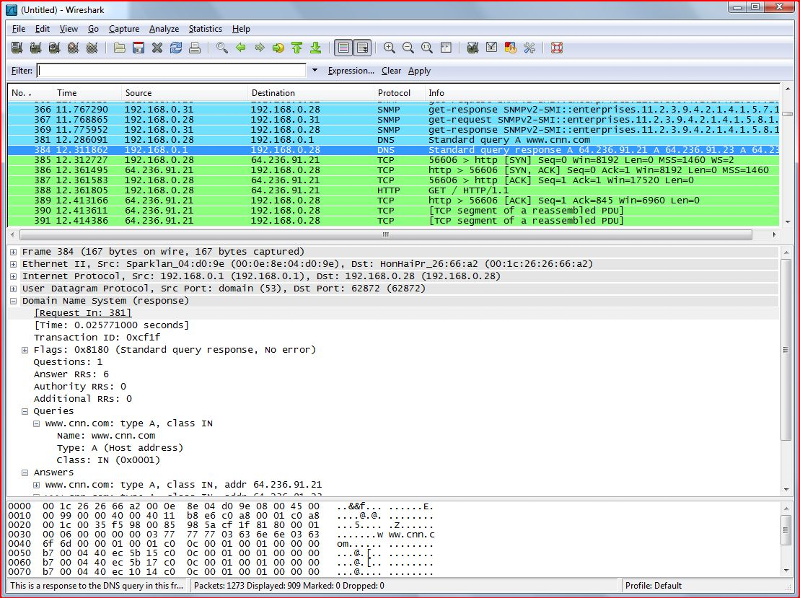
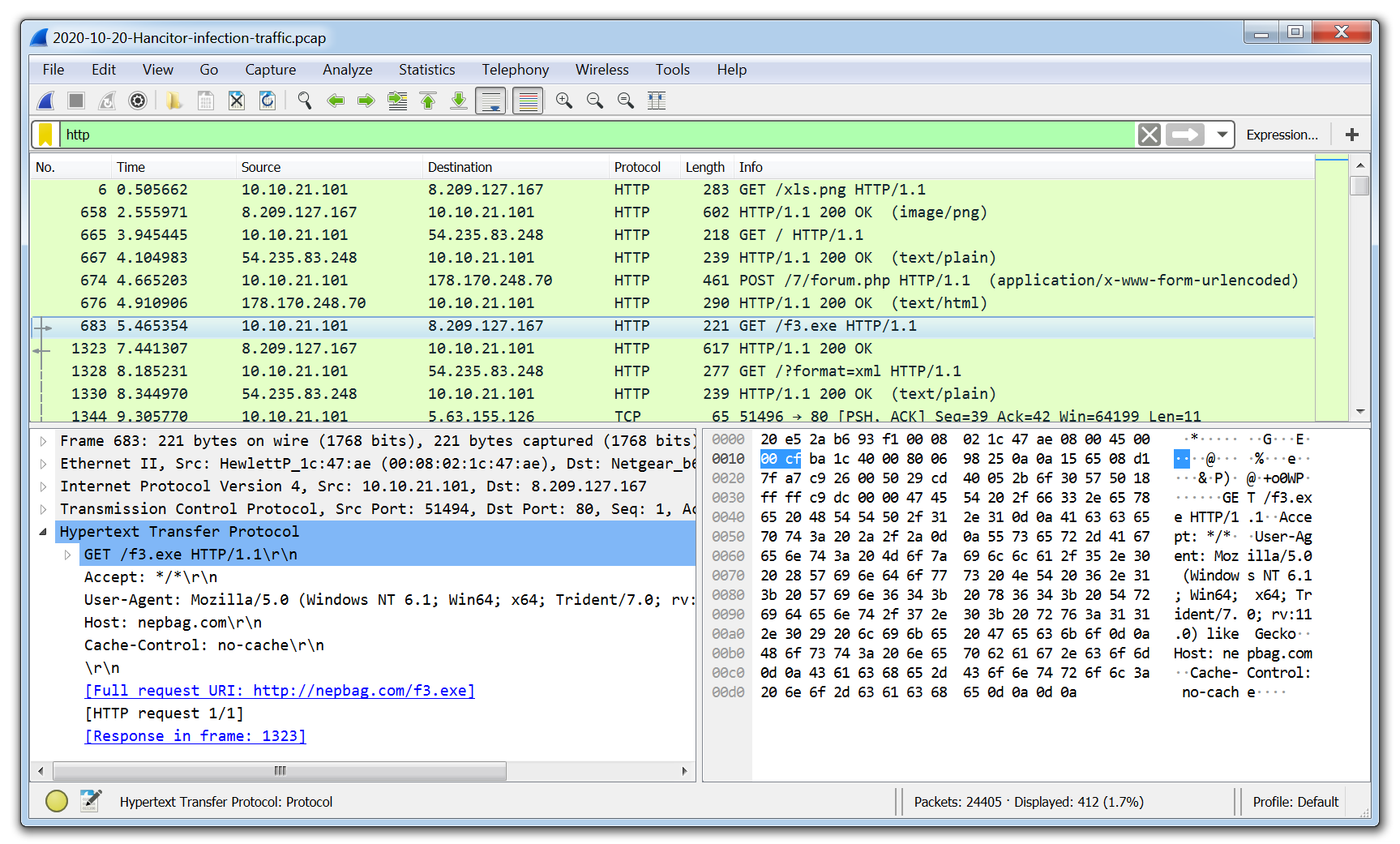
Setting Up A Malware Analysis Lab Experts Exchange Can you spot a malware infection just by looking at the network packets? in lecture 7, we master wireshark to identify hidden threats and malicious traffic patterns in a real world soc lab. This guide delves into the practical, hands on techniques for using wireshark to validate threats, from beaconing malware to data exfiltration attempts. learning objectives: learn to extract key indicators of compromise (iocs) from pcap files, including malicious ips, domains, and file hashes. Whether you're an aspiring soc analyst or just exploring traffic analysis — this hands on session will stretch your network detection muscles. A soc analyst at umbrella corporation is going through siem alerts and sees the alert for connections to a known malicious domain. the traffic is coming from sara’s computer, an accountant who receives a large volume of emails from customers daily.
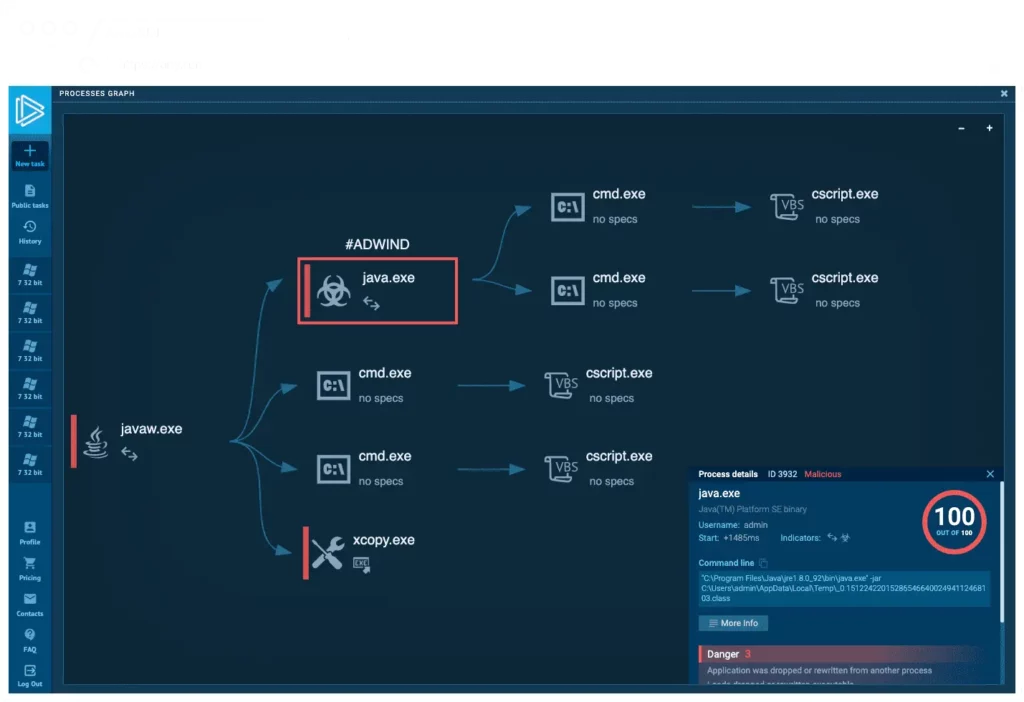
The 13 Best Soc Analysts Resources And Tools Lupovis Whether you're an aspiring soc analyst or just exploring traffic analysis — this hands on session will stretch your network detection muscles. A soc analyst at umbrella corporation is going through siem alerts and sees the alert for connections to a known malicious domain. the traffic is coming from sara’s computer, an accountant who receives a large volume of emails from customers daily. The purpose of this paper is to demonstrate how wireshark is applied in network protocol diagnosis and can be used to find some basic indicators of compromise for a malware. This study aimed to perform a quantitative and observational analysis of network traffic to detect threats within a soc context using wireshark as the principal analysis tool. In this challenge, the analyst is expected to investigate the occurrence of malware from a .pcap file using wireshark. q1 what’s the private ip of the infected host?. Soc analysts can use it to analyze network traffic for signs of vulnerabilities that can be exploited by attackers. overall, wireshark is a powerful tool that can help soc analysts and malware analysts gain insights into network behavior and identify potential security threats.

Mastering Threat Detection With Virustotal A Guide For Soc Analysts The purpose of this paper is to demonstrate how wireshark is applied in network protocol diagnosis and can be used to find some basic indicators of compromise for a malware. This study aimed to perform a quantitative and observational analysis of network traffic to detect threats within a soc context using wireshark as the principal analysis tool. In this challenge, the analyst is expected to investigate the occurrence of malware from a .pcap file using wireshark. q1 what’s the private ip of the infected host?. Soc analysts can use it to analyze network traffic for signs of vulnerabilities that can be exploited by attackers. overall, wireshark is a powerful tool that can help soc analysts and malware analysts gain insights into network behavior and identify potential security threats.

Ethical Hacking And Network Analysis With Wireshark Exploration Of In this challenge, the analyst is expected to investigate the occurrence of malware from a .pcap file using wireshark. q1 what’s the private ip of the infected host?. Soc analysts can use it to analyze network traffic for signs of vulnerabilities that can be exploited by attackers. overall, wireshark is a powerful tool that can help soc analysts and malware analysts gain insights into network behavior and identify potential security threats.
Comments are closed.