Modernizing Siem Operations With Elastic Stack Infosecmap

Modernizing Siem Operations With Elastic Stack Infosecmap When applied to security operations, legacy siems restrict analysts by security use case, narrow their scope of work exclusively to security data, and prevent holistic data collection with restrictive licensing costs. Can your current siem adapt to your fast evolving business needs? in this webinar, learn how elastic helps teams bolster their security program to tackle their toughest challenges by applying a siem built for the modern soc.

Modernizing Siem Operations Elastic Videos This project focuses on building a security information and event management (siem) system using the elk stack (elasticsearch, logstash, kibana). the main objective was to create a lab setup that collects, analyzes, and visualizes security logs from endpoints, while implementing custom alerting mechanisms to detect potential cyber threats. This guide is tailored for cybersecurity professionals who want to understand and leverage the elastic stack as a siem solution to gain real time visibility, perform advanced correlation, and. Abstract: when applied to security operations, legacy siems restrict analysts by security use case, narrow their scope of work exclusively to security data, and prevent holistic data collection with restrictive licensing costs. Implementing siem with elastic security is one of the smartest decisions an organization can make, especially if you want power and flexibility without the enterprise price tag.
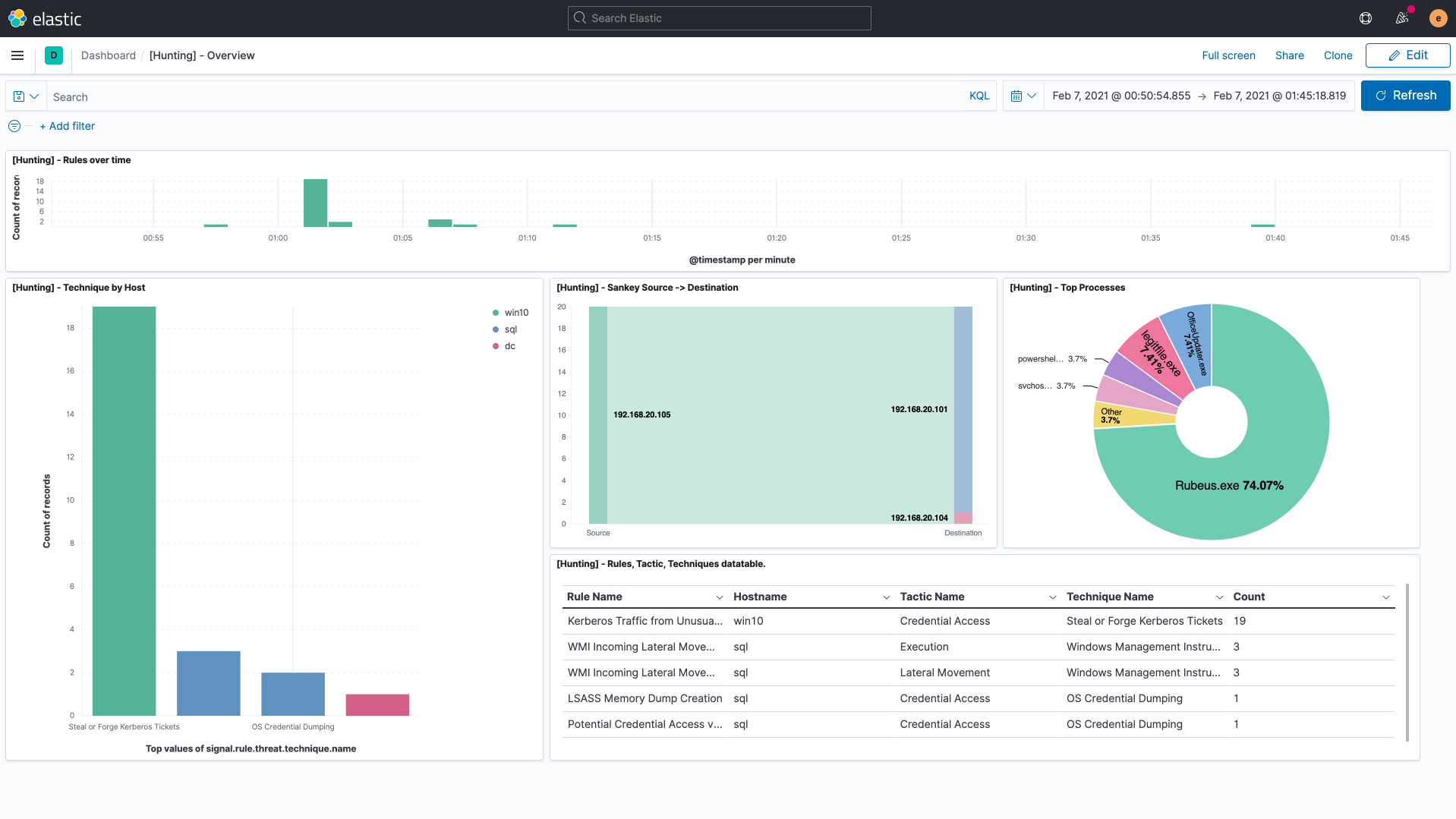
Siem Security Analytics Elastic Security Elastic Siem Abstract: when applied to security operations, legacy siems restrict analysts by security use case, narrow their scope of work exclusively to security data, and prevent holistic data collection with restrictive licensing costs. Implementing siem with elastic security is one of the smartest decisions an organization can make, especially if you want power and flexibility without the enterprise price tag. Hey cyberdefender folks, what we are going to do today is to setup a open source siem security solution, which is elk stack. after troubleshooting and setting up, let’s kick off a real time simulation investigation. I’ve seen too many siem projects fail. not because the technology was bad, but because teams jumped straight into complex alerting without laying the proper foundation. In this tutorial, we will cover the implementation of a threat intelligence driven siem system using the elk stack (elasticsearch, logstash, kibana). we will go through the technical background, implementation guide, and provide code examples to help you get started. The main contributing factor of this paper is that it combines and integrates various technologies to improve threat detection capabilities of the elastic stack based siem.
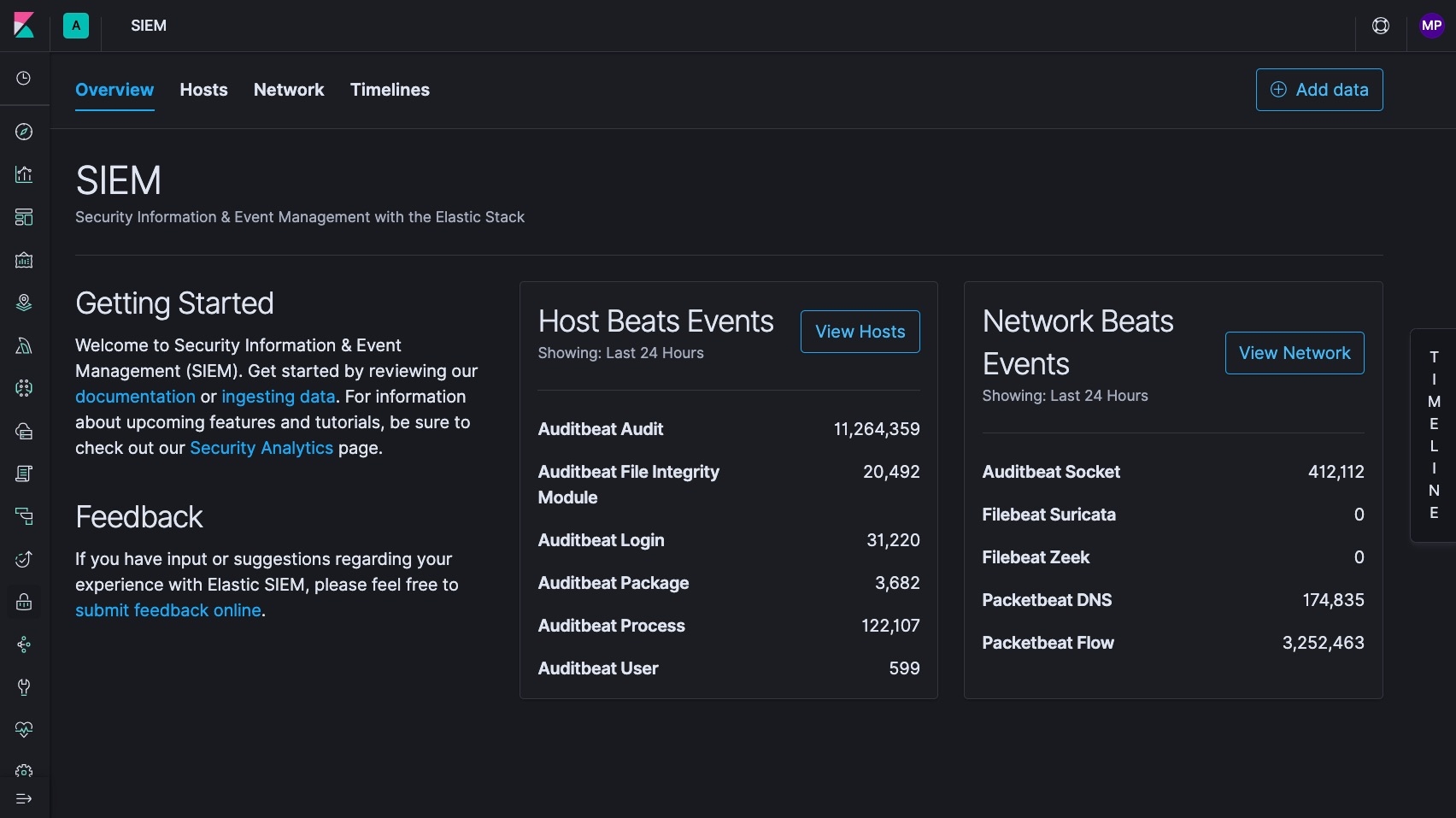
Introducing Elastic Siem Elastic Blog Hey cyberdefender folks, what we are going to do today is to setup a open source siem security solution, which is elk stack. after troubleshooting and setting up, let’s kick off a real time simulation investigation. I’ve seen too many siem projects fail. not because the technology was bad, but because teams jumped straight into complex alerting without laying the proper foundation. In this tutorial, we will cover the implementation of a threat intelligence driven siem system using the elk stack (elasticsearch, logstash, kibana). we will go through the technical background, implementation guide, and provide code examples to help you get started. The main contributing factor of this paper is that it combines and integrates various technologies to improve threat detection capabilities of the elastic stack based siem.
Comments are closed.