Burp Suite Tutorial For Beginners Bug Hunter
Burpsuite Beginners Tutorial How To Use Burp Suite Pentest Jonathans Blog This burp suite tutorial walks you through the essential skills that penetration testers and bug bounty hunters use daily to find vulnerabilities before attackers do. **if you're serious about becoming a bug bounty hunter or ethical hacker, structured learning is key. check out this detailed training program that covers burp suite, owasp top 10, and live vulnerability testing.

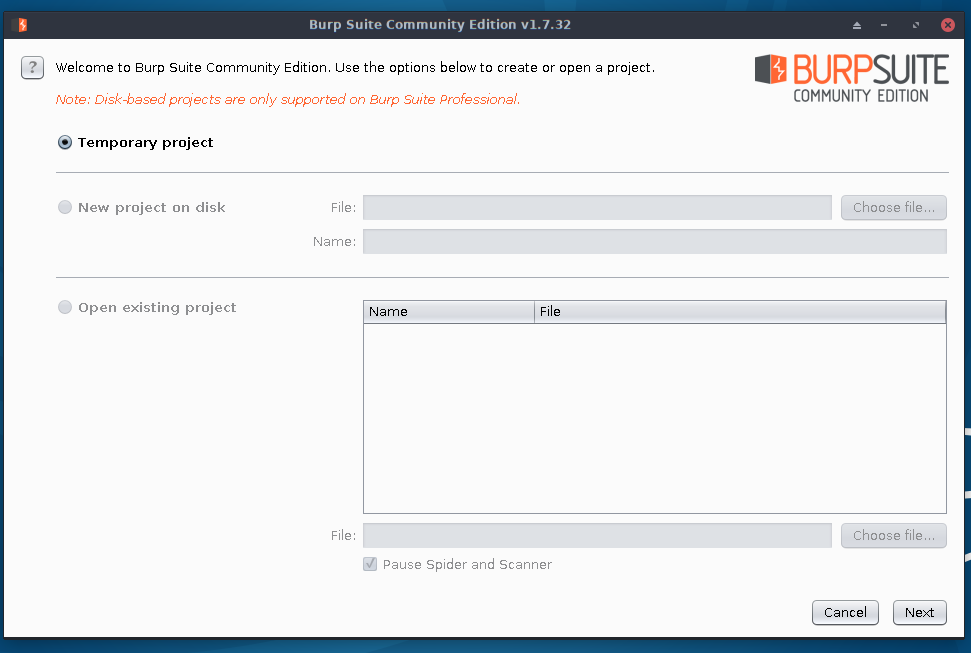
Burp Suite Tutorial Automation Based Security Software Welcome to the ultimate hands on burp suite masterclass by cybermindspace. if you want to become a serious web application pentester or bug bounty hunter, burp suit more. This tutorial is an in depth review of the popular web application security and penetration testing tool burp suite. also, learn about the system requirements and installation steps:. Whether you are a complete beginner, an aspiring ethical hacker, or a bug bounty hunter, this course provides a structured, step by step approach to mastering burp suite. you will start by learning how to install burp suite, configure your browser, and intercept http and https traffic. In this guide, inspired by the original tutorial from bugitrix, we’ll explore how burp suite works, why it’s so important in cybersecurity, and how beginners can start using it like real.
The Ultimate Beginner S Guide To Burp Suite Bugcrowd Whether you are a complete beginner, an aspiring ethical hacker, or a bug bounty hunter, this course provides a structured, step by step approach to mastering burp suite. you will start by learning how to install burp suite, configure your browser, and intercept http and https traffic. In this guide, inspired by the original tutorial from bugitrix, we’ll explore how burp suite works, why it’s so important in cybersecurity, and how beginners can start using it like real. A practical burp suite cheat sheet and learning guide designed for bug bounty hunters and penetration testers to efficiently discover web application vulnerabilities from low severity (p4) to critical (p1) using burp suite. In this course, bug bounty hunting with burp suite, you’ll learn how to leverage burp suite and its extensions to identify and exploit vulnerabilities in web applications. In this hands on class, attendees will learn how to design and develop burp suite extensions for a variety of tasks. after a quick intro to burp and its extension apis, we work on setting up an optimal development environment enabling fast coding and debugging. This beginner friendly tutorial aims to guide you through the basics of burp suite, its key features, how to intercept traffic, and harness its capabilities to enhance the security of your web applications.
Comments are closed.