Mfa From Untrusted Network Conditional Access Demo
Conditional Access Policy To Force Mfa Registration "conditional access for the real world security and accessibility at the same time" in this video, mattchatt shows you how to configure an azure ad conditional access policy to require. To resolve this, you need to adjust your conditional access policies to allow new users to register for mfa from untrusted locations. here's a step by step approach to resolve this issue:.

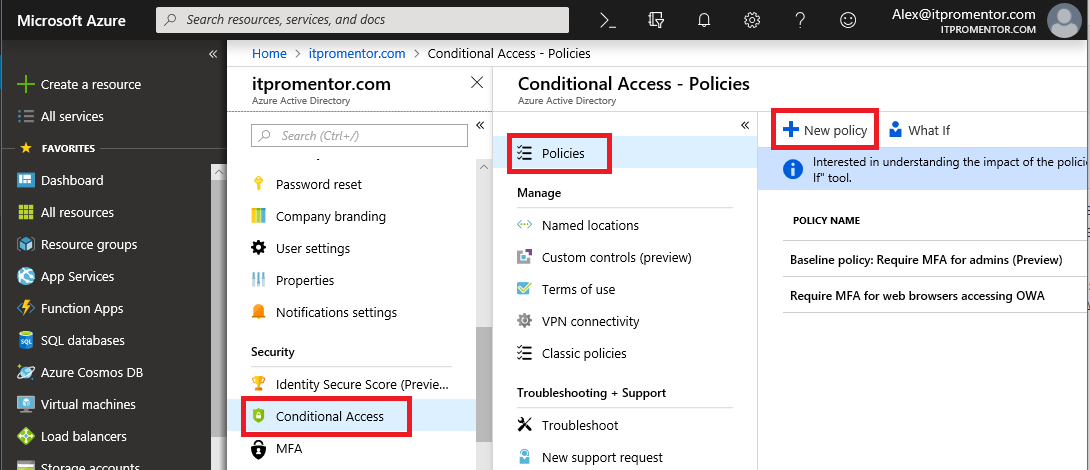
Mfa Vs Conditional Access What S The Difference And Why You Need Both The primary objective of this lab was to implement and validate a zero trust principle: enforce multi factor authentication (mfa) for users accessing sensitive cloud applications only when they are connecting from an untrusted network (outside the corporate perimeter). This guide is useful as if you are rolling out onedrive and seamless single sign on via gpo, microsoft do not support mfa 2fa with onedrive and seamless single sign on via gpo which causes the ssso to fail and onedrive to never login. Using conditional access, we can block this behavior and require users to be in certain locations or on certain devices to complete the security information registration. make sure you test this thoroughly before deploying it in production. from azure ad, navigate to security > conditional access. After you configure azure ad mfa and sspr, you might want to look at how to secure both registrations. for example, you don’t want a spray attack carried out, and the attacker registers for mfa or sspr. you can secure azure mfa registration and sspr registration with azure conditional access.

Mfa Vs Conditional Access What S The Difference And Why You Need Both Using conditional access, we can block this behavior and require users to be in certain locations or on certain devices to complete the security information registration. make sure you test this thoroughly before deploying it in production. from azure ad, navigate to security > conditional access. After you configure azure ad mfa and sspr, you might want to look at how to secure both registrations. for example, you don’t want a spray attack carried out, and the attacker registers for mfa or sspr. you can secure azure mfa registration and sspr registration with azure conditional access. In previous article we have seen how to block sales department to connect office from outside saudi arabia. this article : we will see how to require mfa ( multi factor authentication ) for hr department when connecting from untrusted ip address. I’m trying to require mfa for access from untrusted networks with conditional access per microsoft’s setup instructions. i have the trusted network in cidr notation in the named locations section of azure. In this post, i’ll share how i configured conditional access in microsoft 365 to block access from unauthorized devices. the goal was simple: only devices approved and managed by it should be able to access company resources. Introduction: multi factor authentication (mfa) is a method of confirming a user's claimed identity in which a user is granted access only after successfully presenting 2 or more pieces of evidence (or factors) to an authentication mechanism.

Mfa Conditional Access Trailkol In previous article we have seen how to block sales department to connect office from outside saudi arabia. this article : we will see how to require mfa ( multi factor authentication ) for hr department when connecting from untrusted ip address. I’m trying to require mfa for access from untrusted networks with conditional access per microsoft’s setup instructions. i have the trusted network in cidr notation in the named locations section of azure. In this post, i’ll share how i configured conditional access in microsoft 365 to block access from unauthorized devices. the goal was simple: only devices approved and managed by it should be able to access company resources. Introduction: multi factor authentication (mfa) is a method of confirming a user's claimed identity in which a user is granted access only after successfully presenting 2 or more pieces of evidence (or factors) to an authentication mechanism.
Conditional Access Mfa Australianoke In this post, i’ll share how i configured conditional access in microsoft 365 to block access from unauthorized devices. the goal was simple: only devices approved and managed by it should be able to access company resources. Introduction: multi factor authentication (mfa) is a method of confirming a user's claimed identity in which a user is granted access only after successfully presenting 2 or more pieces of evidence (or factors) to an authentication mechanism.

What Is Mfa Conditional Access Policy
Comments are closed.