Mfa Conditional Access Trailkol
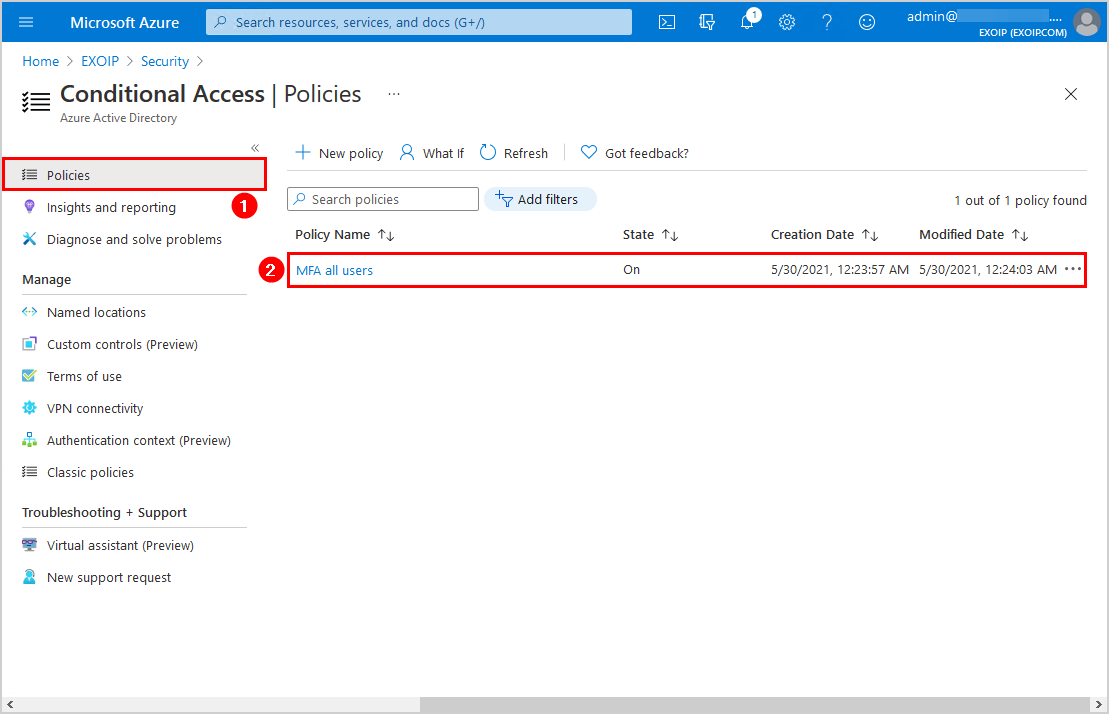
Conditional Access Policy To Force Mfa Registration The following steps help create a conditional access policy to require all users do multifactor authentication, using the authentication strength policy, without any app exclusions. Practical guide to microsoft entra conditional access in 2026. learn the 10 baseline policies to reduce risk (mfa, legacy auth block, compliant devices, session controls, device code flow) without breaking business operations.

Mfa Vs Conditional Access What S The Difference And Why You Need Both Create a custom conditional access policy with authentication strength to require specific multifactor authentication (mfa) methods for external users. Learn how to configure conditional access in microsoft entra id to require multi factor authentication (mfa) before users can join your organization’s entra id. enhance security and prevent unauthorized access. Learn how to configure and test conditional access policies in microsoft entra id to granularly control your users' access and authentication. Conditional access in microsoft entra is a security feature that helps organizations control access to applications and resources based on specific conditions. instead of allowing or blocking access outright, conditional access evaluates signals such as user identity, location, device, and risk level before granting access.

Mfa Vs Conditional Access What S The Difference And Why You Need Both Learn how to configure and test conditional access policies in microsoft entra id to granularly control your users' access and authentication. Conditional access in microsoft entra is a security feature that helps organizations control access to applications and resources based on specific conditions. instead of allowing or blocking access outright, conditional access evaluates signals such as user identity, location, device, and risk level before granting access. Understand the phases of conditional access policy enforcement in microsoft entra and how to apply them to secure user access. Conditional access policies are the first line of defense against unauthorized access to your entra id tenant. individually, each policy in this guide closes a specific gap that both we and threat actors regularly exploit. These policies determine who gets access to what resources, under which conditions, and with what authentication requirements. let's explore practical implementations through real world scenarios you can apply today. Administrators can specify an authentication strength to access a resource by creating a conditional access policy with the require authentication strength control. they can choose from three built in authentication strengths: multifactor authentication strength, passwordless mfa strength, and phishing resistant mfa strength.
Mfa Conditional Access Trailkol Understand the phases of conditional access policy enforcement in microsoft entra and how to apply them to secure user access. Conditional access policies are the first line of defense against unauthorized access to your entra id tenant. individually, each policy in this guide closes a specific gap that both we and threat actors regularly exploit. These policies determine who gets access to what resources, under which conditions, and with what authentication requirements. let's explore practical implementations through real world scenarios you can apply today. Administrators can specify an authentication strength to access a resource by creating a conditional access policy with the require authentication strength control. they can choose from three built in authentication strengths: multifactor authentication strength, passwordless mfa strength, and phishing resistant mfa strength.

Mfa Conditional Access Trailkol These policies determine who gets access to what resources, under which conditions, and with what authentication requirements. let's explore practical implementations through real world scenarios you can apply today. Administrators can specify an authentication strength to access a resource by creating a conditional access policy with the require authentication strength control. they can choose from three built in authentication strengths: multifactor authentication strength, passwordless mfa strength, and phishing resistant mfa strength.

Boost Security With Mfa Conditional Access Lbmc
Comments are closed.