Malicious Doc Letsdefend Malware Analysis Challenge

Malware Analysis Challenge Analyzing Malicious Word Document In this article, i’ll walk you through the steps i took to solve the "malicious doc challenge" on lets defend. the goal is to analyze a suspicious document, identify its behavior, and. Letsdefend is a blue team training platform. this writeup is a challenge on letsdefend.

Malware Analysis Challenge Analyzing Malicious Word Document Analyze malicious .doc file. hey there! hack the box and letsdefend accounts are becoming one. if you use both platforms, please link them now to avoid any disruption to your access. In this letsdefend challenge, we analyze a weaponized .doc file delivered inside a zip archive and uncover the exploit, payload, and command and control (c2) communication. this write up. The malicious file " root desktop questionfiles siparis 17.xls" is trying to download files from an address. from which domain is it trying to download the file?. Analyzing a potentially malicious word document requires a cautious approach to protect your system from harm and the most crucial step is preparing a secure environment that isolates the document.
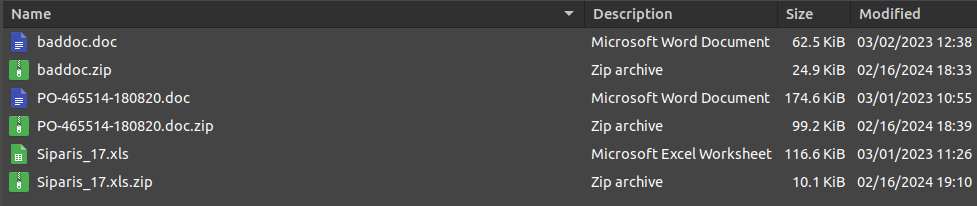
Malware Analysis Challenge Analyzing Malicious Word Document The malicious file " root desktop questionfiles siparis 17.xls" is trying to download files from an address. from which domain is it trying to download the file?. Analyzing a potentially malicious word document requires a cautious approach to protect your system from harm and the most crucial step is preparing a secure environment that isolates the document. Description: performing malware analysis on a malicious document from the iceid malware family let’s defend icedid malware family app.letsdefend.io challenge icedid malware family. What is the relevant exploit cve code obtained as a result of the analysis? 00:57 3. what is the name of the malicious software downloaded from the internet as a result of the file running?. This week, we’re tackling the mshtml challenge from letsdefend. our mission is to analyze four malicious document (maldoc) samples, discover the ip addresses and domains hidden within them, and use that information to figure out which vulnerability or cve that the threat actor is exploiting. In this letsdefend dynamic malware analysis walkthrough part 2, we will use wireshark, process hacker, anyrun, and cyberchef to conduct dynamic malware analysis.

Malware Analysis Challenge Analyzing Malicious Word Document Description: performing malware analysis on a malicious document from the iceid malware family let’s defend icedid malware family app.letsdefend.io challenge icedid malware family. What is the relevant exploit cve code obtained as a result of the analysis? 00:57 3. what is the name of the malicious software downloaded from the internet as a result of the file running?. This week, we’re tackling the mshtml challenge from letsdefend. our mission is to analyze four malicious document (maldoc) samples, discover the ip addresses and domains hidden within them, and use that information to figure out which vulnerability or cve that the threat actor is exploiting. In this letsdefend dynamic malware analysis walkthrough part 2, we will use wireshark, process hacker, anyrun, and cyberchef to conduct dynamic malware analysis.
Comments are closed.