Letsdefend Malware Analysis Challenges Malicious Doc

Malware Analysis Challenge Analyzing Malicious Word Document Analyze malicious .doc file. hey there! hack the box and letsdefend accounts are becoming one. if you use both platforms, please link them now to avoid any disruption to your access. Letsdefend is a blue team training platform. this writeup is a challenge on letsdefend.

Malware Analysis Challenge Analyzing Malicious Word Document In this article, i’ll walk you through the steps i took to solve the "malicious doc challenge" on lets defend. the goal is to analyze a suspicious document, identify its behavior, and. In this letsdefend challenge, we analyze a weaponized .doc file delivered inside a zip archive and uncover the exploit, payload, and command and control (c2) communication. this write up. Analyzing a potentially malicious word document requires a cautious approach to protect your system from harm and the most crucial step is preparing a secure environment that isolates the document. What is the relevant exploit cve code obtained as a result of the analysis? checking out the extracted object from the rtf, it seems to be an ole file, judging by the file signatures. taking a peek at the hex of the .bin file, it looks like it's running some sort of shell code. let's put this to the test with scdbg.
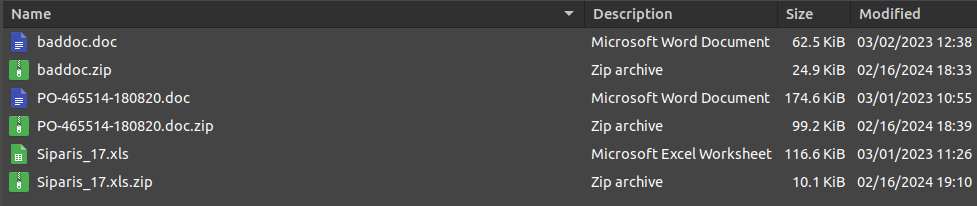
Malware Analysis Challenge Analyzing Malicious Word Document Analyzing a potentially malicious word document requires a cautious approach to protect your system from harm and the most crucial step is preparing a secure environment that isolates the document. What is the relevant exploit cve code obtained as a result of the analysis? checking out the extracted object from the rtf, it seems to be an ole file, judging by the file signatures. taking a peek at the hex of the .bin file, it looks like it's running some sort of shell code. let's put this to the test with scdbg. What is the relevant exploit cve code obtained as a result of the analysis? 00:57 3. what is the name of the malicious software downloaded from the internet as a result of the file running?. This week, we’re tackling the mshtml challenge from letsdefend. our mission is to analyze four malicious document (maldoc) samples, discover the ip addresses and domains hidden within them, and use that information to figure out which vulnerability or cve that the threat actor is exploiting. Summary this doc file is a crafted rtf file to exploit remote code execution vulnerability to a system using cve 2017 11882. it is a stager that once it opened it tries to download an actual malware from a certain url using http get method and it also drops a file after it runs. Malicious document files are really popular nowadays. generally, attackers use these files to gain initial access and we'll teach you how you can analyze these types of files.

Introduction To Malware Analysis Prepared For Beginners Security What is the relevant exploit cve code obtained as a result of the analysis? 00:57 3. what is the name of the malicious software downloaded from the internet as a result of the file running?. This week, we’re tackling the mshtml challenge from letsdefend. our mission is to analyze four malicious document (maldoc) samples, discover the ip addresses and domains hidden within them, and use that information to figure out which vulnerability or cve that the threat actor is exploiting. Summary this doc file is a crafted rtf file to exploit remote code execution vulnerability to a system using cve 2017 11882. it is a stager that once it opened it tries to download an actual malware from a certain url using http get method and it also drops a file after it runs. Malicious document files are really popular nowadays. generally, attackers use these files to gain initial access and we'll teach you how you can analyze these types of files.

Malicious Document Analysis Letsdefend Summary this doc file is a crafted rtf file to exploit remote code execution vulnerability to a system using cve 2017 11882. it is a stager that once it opened it tries to download an actual malware from a certain url using http get method and it also drops a file after it runs. Malicious document files are really popular nowadays. generally, attackers use these files to gain initial access and we'll teach you how you can analyze these types of files.
Comments are closed.