Making Protocols Post Quantum
Making Protocols Post Quantum This mosca model shows how to estimate the timeline to post quantum vulnerability of your assets and helps you understand how soon to begin the journey to post quantum readiness. What does nist guidance say about transitioning from quantum vulnerable cryptographic algorithms to post quantum digital signature algorithms and key establishment schemes?.

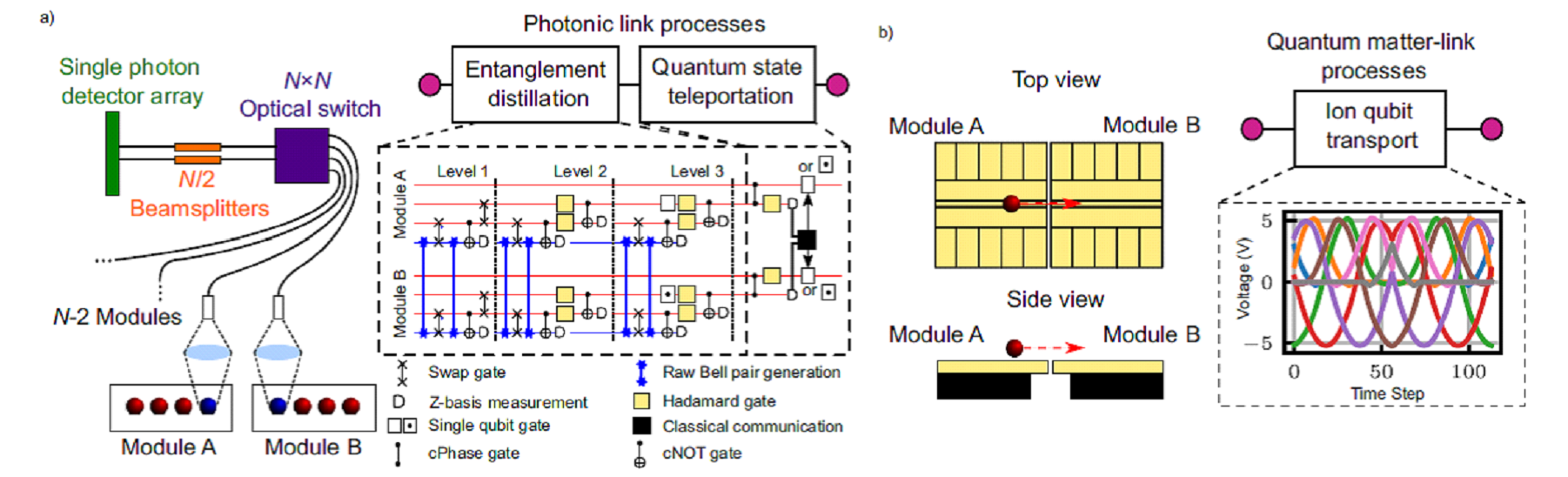
Making Protocols Post Quantum This document provides general information (such as parameter sizes, security assumptions, and targeted security models) on a range of widely studied post quantum cryptographic algorithms, including key encapsulation mechanisms (kems) and digital signature schemes. As described in the article on post quantum cryptography, elliptic curve digital signature algorithms (ecdsa) used in most blockchain protocols are vulnerable to shor's algorithm. public keys in many blockchain protocols are exposed when transactions are executed, creating windows of vulnerability. To protect data in transit against the “harvest now and decrypt later” attacks (i.e., passive network attacks), the simplest solution is to make the key exchange mechanism in communication protocols quantum safe while retaining classic handshake signatures and current public key infrastructure (pki). This paper presents a structured literature review of ongoing global efforts to integrate post quantum cryptography (pqc) into widely deployed communication and identity protocols. we analyze current readiness, standardization initiatives, hybrid cryptographic approaches, and deployment challenges across multiple layers of the protocol stack, including tls, ssh, vpns, certificate.
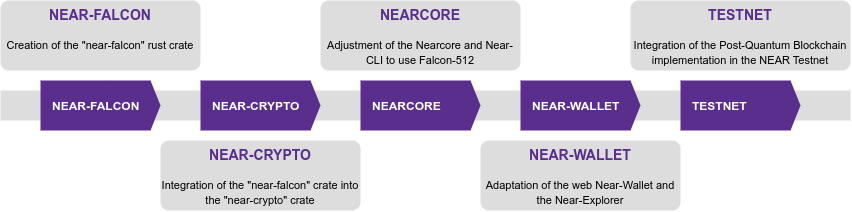
Post Quantum Blockchain To protect data in transit against the “harvest now and decrypt later” attacks (i.e., passive network attacks), the simplest solution is to make the key exchange mechanism in communication protocols quantum safe while retaining classic handshake signatures and current public key infrastructure (pki). This paper presents a structured literature review of ongoing global efforts to integrate post quantum cryptography (pqc) into widely deployed communication and identity protocols. we analyze current readiness, standardization initiatives, hybrid cryptographic approaches, and deployment challenges across multiple layers of the protocol stack, including tls, ssh, vpns, certificate. Hardening meta’s systems — and any other organization’s systems — to post‑quantum cryptography takes years of phased work across protocols, products, and infrastructure as standards and implementations and threats mature. The transition to post quantum cryptography (pqc) has gained momentum amid advancements like nist's standardization of quantum resistant algorithms. key developments include addressing implementation challenges, enhancing crypto agility, and exploring hybrid approaches. In this blog post, we will discuss how one might upgrade cryptographic protocols to make them secure against quantum computers. we will focus on the cryptography that they use and see what the challenges are in making them secure against quantum computers. While quantum computers may not be able to crack conventional encryption protocols until 2030, many cybersecurity and risk managers should evaluate their options now.
Polynom World S First Pqc Collabration Suite Hardening meta’s systems — and any other organization’s systems — to post‑quantum cryptography takes years of phased work across protocols, products, and infrastructure as standards and implementations and threats mature. The transition to post quantum cryptography (pqc) has gained momentum amid advancements like nist's standardization of quantum resistant algorithms. key developments include addressing implementation challenges, enhancing crypto agility, and exploring hybrid approaches. In this blog post, we will discuss how one might upgrade cryptographic protocols to make them secure against quantum computers. we will focus on the cryptography that they use and see what the challenges are in making them secure against quantum computers. While quantum computers may not be able to crack conventional encryption protocols until 2030, many cybersecurity and risk managers should evaluate their options now.
Comments are closed.