Post Quantum Algorithm Beats Quantum Computer Hacks
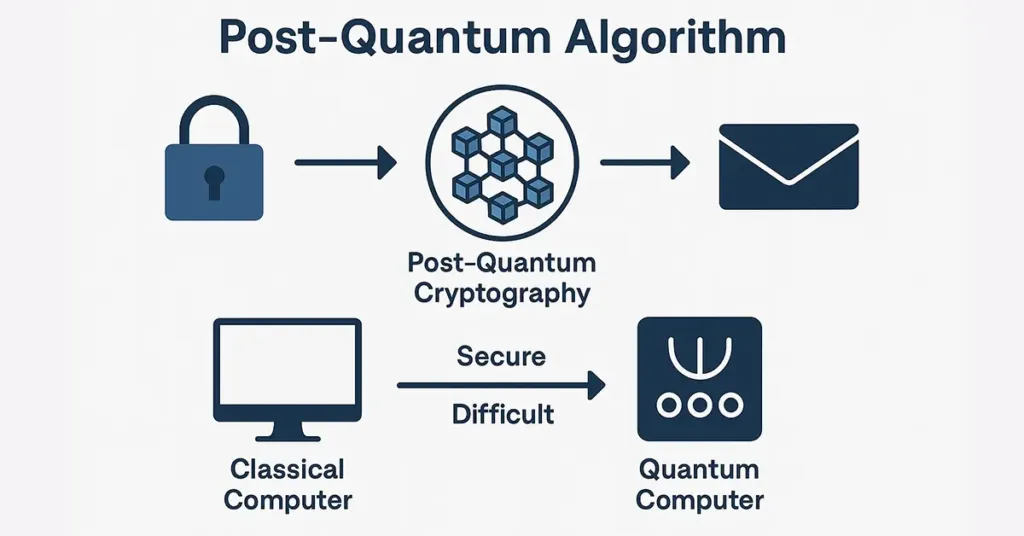
Post Quantum Algorithm Beats Quantum Computer Hacks A post quantum algorithm relies on the concept of using mathematical problems that are hard to break through quantum computers. they are resistant to both classical and quantum attacks. Post quantum cryptography (pqc) refers to cryptographic algorithms designed to be secure against both classical and quantum computers. importantly, these are not quantum algorithms —you don’t need a quantum computer to use them.
Post Quantum Algorithm Beats Quantum Computer Hacks The purpose of this study is to investigate a variety of post quantum algorithms, including lattice based, hash based, code based, multivariate, and isogeny based cryptography, and to evaluate the possibility of these algorithms to successfully defend against future quantum attacks. Post quantum cryptography (pqc), sometimes referred to as quantum proof, quantum safe, or quantum resistant, is the development of cryptographic algorithms (usually public key algorithms) that are currently thought to be secure against a cryptanalytic attack by a quantum computer. [1]. They are working on defensive strategies to meet the challenge — inventing cryptographic algorithms that run not just on quantum computers but on today’s conventional components. this technology has a name: post quantum cryptography. there have already been notable breakthroughs. This looming danger is known as quantum hacking, and it’s fueling a global race to develop post quantum encryption — algorithms that can resist even the most powerful quantum attacks.

Post Quantum Algorithm Beats Quantum Computer Hacks They are working on defensive strategies to meet the challenge — inventing cryptographic algorithms that run not just on quantum computers but on today’s conventional components. this technology has a name: post quantum cryptography. there have already been notable breakthroughs. This looming danger is known as quantum hacking, and it’s fueling a global race to develop post quantum encryption — algorithms that can resist even the most powerful quantum attacks. Learn how post quantum cryptography (pqc) defends against quantum hacking with quantum safe algorithms like lattice based cryptography. explore nist standards and best practices. Learn how to protect your applications from quantum computing threats with post quantum cryptography methods, implementation guides, and practical code examples. Quantum computers, leveraging algorithms like shor’s algorithm, can solve these problems exponentially faster, rendering existing encryption obsolete. this looming threat has spurred a global race to develop and deploy quantum resistant cryptography, also known as post quantum cryptography (pqc). Post quantum cryptography represents a forward looking approach to cybersecurity, designed to withstand the computational prowess of quantum computers. this segment focuses on the fundamentals of this emerging field, examining specific algorithms and their respective merits and challenges.
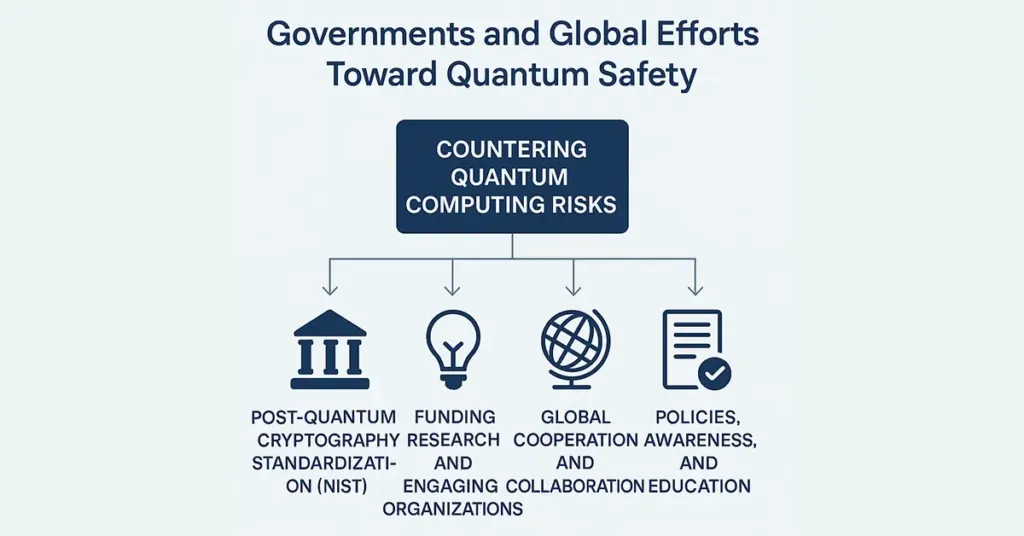
Post Quantum Algorithm Beats Quantum Computer Hacks Learn how post quantum cryptography (pqc) defends against quantum hacking with quantum safe algorithms like lattice based cryptography. explore nist standards and best practices. Learn how to protect your applications from quantum computing threats with post quantum cryptography methods, implementation guides, and practical code examples. Quantum computers, leveraging algorithms like shor’s algorithm, can solve these problems exponentially faster, rendering existing encryption obsolete. this looming threat has spurred a global race to develop and deploy quantum resistant cryptography, also known as post quantum cryptography (pqc). Post quantum cryptography represents a forward looking approach to cybersecurity, designed to withstand the computational prowess of quantum computers. this segment focuses on the fundamentals of this emerging field, examining specific algorithms and their respective merits and challenges.
Comments are closed.